Financial risk management used to live quietly in treasury, looped in once a quarter and otherwise left alone.
That's not where it sits anymore.
This guide covers what financial risk management is in 2026, the categories worth understanding, how to run a meaningful assessment, the frameworks that hold up, and the tools available.
TL;DR
- Financial risk management is operational work that touches the balance sheet every day. It's the running job of finding exposure, deciding what each one is worth, and giving someone a deadline to act on it.
- Six categories cover most of what matters: credit, liquidity, market, operational, compliance and regulatory, and the newer model and AI risk. Each calls for its own response, so teams that lean on a single playbook end up with blind spots.
- Assessments run as a loop. Map exposures, size them, choose responses, track the indicators, and the cycle restarts the moment conditions change.
- Frameworks define the layers, not the program itself. ISO 31000, COSO ERM, Basel IV, and FAIR each address something different, and most working programs pull from several rather than picking one.
- Tooling decisions tend to get underweighted. Spreadsheets fail at scale, enterprise GRC suites take quarters to install, and SmartSuite fills the gap between them with a connected workspace that doesn't need a heavyweight stand-up.
What is Financial Risk Management?
Financial risk management is the practice of identifying where money could be lost, sizing the potential damage, choosing how to respond, and confirming the response is doing its job over time.
In writing, it sounds tidy.
In day-to-day reality, it looks like a treasurer locking in a hedge ahead of a quarterly close, a credit team pulling back on a counterparty whose ratios slipped, or a CFO modeling the refinancing window against a possible rate shock.
It also isn't only a banking concern.
Any organization that extends credit, carries debt, transacts in foreign currency, manages a pension, or parks reserves in market instruments is doing financial risk management, whether it appears in someone's job title or not.
The 2023 collapse of Silicon Valley Bank wasn't a black swan.
It was a duration mismatch combined with an unusually concentrated depositor base, the kind of stress combination a serious scenario program is built to surface.
Businesses that surface exposure early get to choose their response.
What are the different types of Financial Risk Management?
Financial risk shows up as a family of related but distinct exposures, each calling for its own toolkit.
- Credit risk is the risk that someone owing you money fails to pay. For a bank, that's a defaulted loan. For a software vendor, it's a customer that goes under before settling its invoice
- Liquidity risk has two types:
Funding liquidity is the inability to roll over short-term obligations, such as a corporation that can't access commercial paper markets when conditions tighten.
Asset (or market) liquidity is the inability to sell something fast enough at anything close to its carrying value.
- Market risk captures losses from price, rate, or currency movements.
Interest rate, equity, commodity, and FX risks all live under this umbrella. A US manufacturer buying euro-denominated components has FX exposure on every order, with the only real choice being whether to hedge it, price it in, or absorb it.
- Operational risk is the financial cost when something breaks inside the company.
The list runs long: a misrouted wire, a reconciliation that fails on close night, a fraud event, a senior person leaving with undocumented institutional knowledge.
Basel IV is moving banks off internal models for operational risk and onto a standardized approach driven by income and historical losses.
- Compliance and regulatory risk is the cost of being out of step with the rules.
Recent activity is a good measure of how active this category is. The UK PRA finalized Basel 3.1 in January 2026 for January 1, 2027 implementation and US agencies released their capital proposals on March 19, 2026.
- Model and AI risk is the youngest entry and one of the most contested.
As more credit decisioning, fraud screening, and trading signals lean on machine learning, the risks of bad training data, model drift, and unsanctioned AI use inside the business have crossed from theoretical to practical.
"The model produced this" no longer satisfies a regulator.
However, all of these categories don't live in separate boxes.
Credit risk turns into liquidity risk the moment a defaulted counterparty starves a desk of cash.
Operational risk turns into market risk when a botched hedge execution leaves a position naked.
And a pricing model that drifted can quietly accumulate credit losses across thousands of loans before anyone notices, with reputational damage following close behind.
What are the benefits of managing financial risk?
The payoff lands across several dimensions of managing financial risk:
- Decisions get sharper. When risk shows up next to a deal in numerical form, the room is comparing apples to apples instead of arguing intuitions.
- Capital costs come down. Lenders, investors, and insurers reward maturity. They charge less for credit and quote tighter premiums when the program looks credible.
- Surprises stop being surprises. Loss events still happen. They just stop arriving without warning, and the team has a playbook ready before improvisation kicks in.
- Audits and regulator engagements get easier. When risks, controls, evidence, and remediation history live together, the conversation shifts from "find me the file" to "here's the dashboard."
- Speed becomes a differentiator. Firms that mapped their DORA exposure before its January 17, 2025, application date arrived ready, while peers were still parsing the regulation.
How can you approach Financial Risk Management?
Once a risk is on the table, the response menu is short.
There are five options: avoid the exposure, reduce it, transfer it to someone better placed to bear it, share it through a structure, or accept it.
The right choice rarely lives in instinct. Two questions decide it: how much of the outcome can be shaped through deliberate action, and how badly would the worst case hurt.
- Reduction is where most active risk work concentrates.
Hedging FX exposure, tightening credit policy and enforcing it through real limits, diversifying funding so a single market closing doesn't shut the business down, training staff to spot fraud before the wire goes out.
These are the levers a finance team pulls when both probability and damage are within reach.
- Some exposures stay outside reach.
Macroeconomic shocks, sovereign downgrades, and geopolitical pressure can close a market overnight.
When those threaten serious damage, the response shifts to transferring the risk by sharing it through structures like joint ventures with split liability, or to outright avoidance, which is just declining to enter the market or take the deal.
A bank walking away from a sanctioned jurisdiction is the cleanest example of that last one.
- Smaller risks need lighter handling.
Document the exposure, assign a review owner, schedule the next check, and pay attention to the bigger problems waiting in the queue.
The lowest-priority risks (small impact, no real influence) get logged once and revisited only if they shift category. Most registers carry a long tail.
The pattern teams fall into is reaching for reduction by default, because mitigation looks like effort, and effort looks like responsibility.
The trap is that low-impact, low-influence risk consumes the same control budget as a high-impact one.
And waving through a high-impact risk you could've shaped is mismanagement that someone will trace back to that decision.
How to conduct a Financial Risk Management assessment
A financial risk assessment is the structured way to figure out where the business is exposed, how big the exposures are, what to do about them, and what to watch.
The textbook version is a five-step waterfall.
The version that works is a loop, because financial conditions don't politely wait for analysis to finish before they shift:
Start with the scope and then identify
Trying to assess "everything" produces shallow output. Bounded scopes produce useful work.
- "Counterparty credit risk in the top fifty customers."
- "FX exposure in our European subsidiaries over the next four quarters."
- "Liquidity coverage if our largest funding source goes offline."
Inside the scope, identification draws on interviews with people closest to the risk, reviews of past loss events, and external signals like ratings actions, regulator bulletins, and peer disclosures.
Each surfaced exposure goes into a register. That register is the spine of the rest of the work.
Move to measurement
For exposures where dollar figures hold up, lean on quantitative methods: VaR, expected shortfall, credit VaR, scenario analysis, stress testing.
The point is to translate exposure into a number that leadership can compare to other risks and to the firm's appetite.
For exposures where the math is shaky (reputational damage from a regulatory finding, say), narrative scoring with clear criteria beats false precision.
Then choose treatment and assign accountability
Once an exposure is sized, the response choice follows from the framework above.
Each treated risk gets an owner, a control or set of actions, a due date, and a tracking mechanism so progress is visible without weekly check-ins.
End with monitoring, which is where everything starts again
Conditions move, counterparties weaken, hedges decay, and regulations shift.
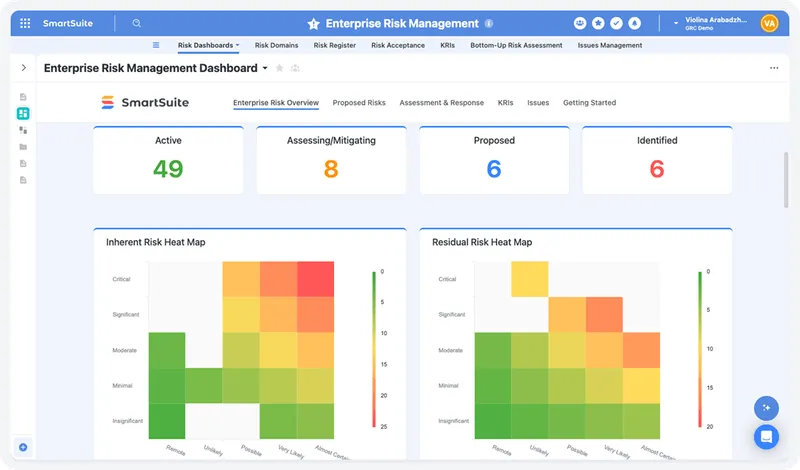
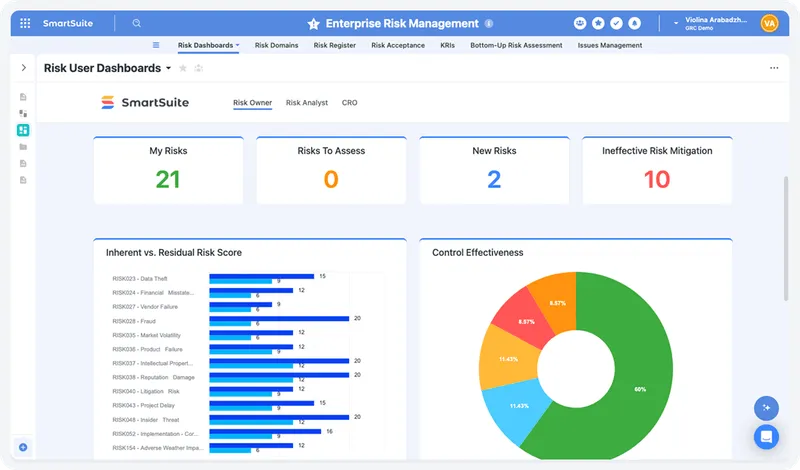
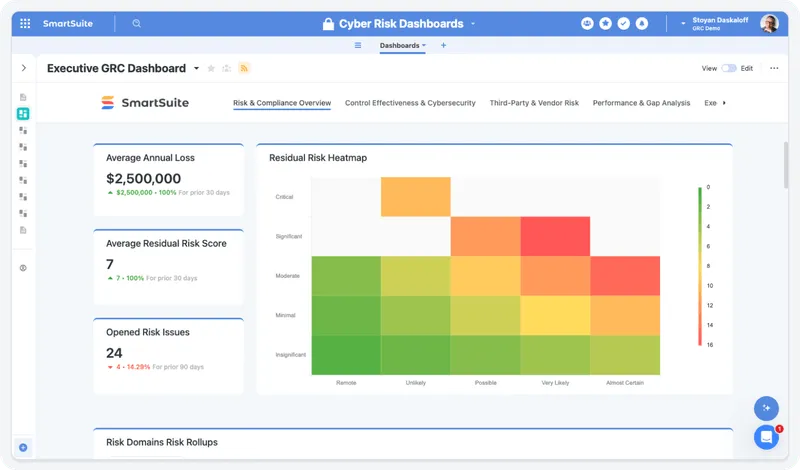
I’ve noticed that KRIs in dashboards do most of the heavy lifting here, with thresholds set high enough not to spam the team and low enough to fire before damage is done.
Near-misses get logged with the same discipline as actual losses, because near-misses are the cheapest data the program will ever generate.
The reason this works as a loop and not a sequence is that step four feeds step one.
New risks surface, old treatments fade, and the cycle gets faster as the program matures because registers, controls, KRIs, and evidence are wired together by then.
What are the different Financial Risk Management frameworks?
Most well-run financial risk programs don't operate inside a single framework. They borrow from several, layered to cover different parts of the work.
- ISO 31000 is the international principles standard.
It's deliberately non-prescriptive, giving you a process model adaptable to any organization regardless of size or industry.
For teams building from scratch, it's a sensible foundation that won't lock anyone into a heavyweight methodology before the program proves out.
- COSO ERM is a more directive framework that links risk management explicitly to strategy and performance.
US public companies and regulated financial institutions often default to COSO because their audit committees are already aligned on it.
Its strength is the connection between risk-taking and value creation, which makes it easier to position risk as a strategic input rather than a compliance line item.
- Basel IV (also referenced as Basel III Endgame or Basel 3.1) is the framework reshaping bank capital and risk practice in 2026.
The framework removes the advanced internal ratings-based approach for large corporate exposures, introduces an output floor that caps internal-model capital benefit at 27.5% below the standardized approach, and standardizes operational risk capital calculation.
- FAIR (Factor Analysis of Information Risk) is the framework to know if cyber exposure needs to be expressed in financial terms.
Boards increasingly want loss exposure quantified rather than rated on a heat map, and FAIR is the open standard most cyber quantification programs build on.
What kinds of tools can you use for Financial Risk Management?
Tooling decisions span a wide range, from a single spreadsheet to a six-figure GRC implementation, with several useful options between them.
- Spreadsheets are where most programs begin.
Excel or Sheets handles a small register, a few VaR calculations, and a loss event log without much friction, and the cost is essentially zero.
The breakdown shows up later, when the program needs cross-functional visibility, real-time data, version history that holds up under audit, and permission controls that prevent accidental edits to source data.
Spreadsheets are also a recurring source of material reporting errors, mostly because there's no governance layer.
- Dedicated GRC platforms like Archer, MetricStream, IBM OpenPages, ServiceNow IRM, and Onspring occupy the heavyweight end of the market.
These were engineered for complex enterprise programs with deep risk libraries, formal control testing, internal audit workflows, and board-grade reporting.
Large banks, insurers, and other heavily regulated firms run on these for good reason.
The catch is the implementation: budgets typically run into six or seven figures, with dedicated admins and multi-quarter rollouts.
- Compliance automation platforms, including Vanta, Drata, Sprinto, Scytale, and Secureframe specialize in evidence collection for SOC 2, ISO 27001, and similar attestations.
They're highly effective at the certification problem.
The mismatch is that financial risk goes well beyond what a SOC 2 scope covers, so credit, liquidity, market, and operational risk still need somewhere to live.
- Quantitative risk and analytics tools like Bloomberg, Moody's Analytics, MSCI, and Numerix do the modeling: VaR distributions, credit migrations, scenario libraries, stress engines.
Trading desks, asset managers, and quant teams depend on them. They work alongside a broader risk program rather than replacing it.
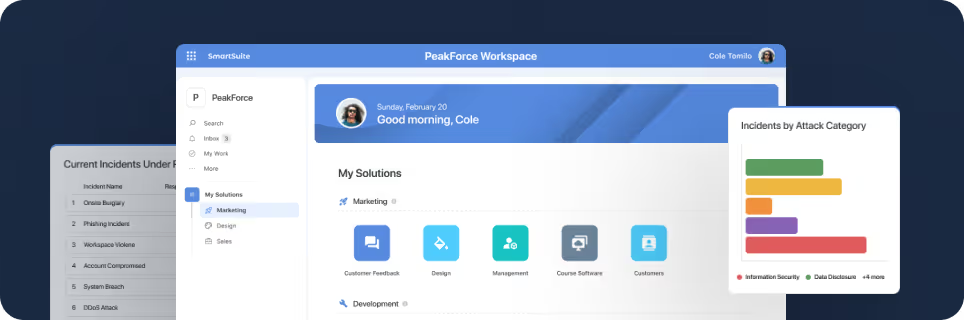
- Connected work platforms: Instead of treating risk as a separate stack, they put risk, compliance, and audit work in the same flexible system as the rest of the business.
SmartSuite (that’s us) is an example in this category, and the approach tends to fit mid-market companies and growing finance teams whose risk work needs to stay close to operations rather than getting parked in a tool the rest of the company never opens.
➡️ For teams that have outgrown spreadsheets but aren't ready to commit to enterprise GRC, SmartSuite is a credible middle path.
It's an AI-native work platform that supports risk registers, scoring methodologies, KRI tracking, mitigation plans, third-party risk, and incident workflows in a single connected workspace.
The platform is no-code, which means finance and risk teams can shape the program around how they actually work rather than fitting their work into someone else's data model.
Automation handles the recurring grind: testing reminders, threshold-based escalation when KRIs trip, vendor review cycles, and incident routing.
Live dashboards keep leadership in the loop on exposure and remediation without anyone exporting to a deck.
SmartSuite AI takes on the time-sink work like questionnaire summarization, incident report drafting, and gap detection in risk documentation, while keeping a human reviewer in the loop on every governance-relevant decision.
Pricing starts at $15/user/month for the Team plan, with solution-based pricing for regulated organizations that need to scope access by department, region, or program.
Learn more about SmartSuite’s risk management solution for enterprises:
Make your financial risk program easier to live with
For most finance teams, the real choice isn't between best tools and second-best.
It's between a system the team uses and one that becomes shelfware after the implementation team leaves.
The fit usually depends on a few practical things:
- How tightly the risk program needs to plug into the rest of the business.
- How much customization the team needs over the next two years.
- And how quickly leadership wants something live.
An enterprise GRC platform pays back when risk operates as its own function with its own data model and dedicated admins.
Compliance automation tools are the right buy when a specific certification is the primary objective.
A spreadsheet still works while one person can hold the program in their head.
Outside those lanes, the better answer is a platform flexible enough to model the program around how the business runs, governed enough to satisfy auditors, and quick enough to deploy so that finance teams prove value before the next budget review.
That's where SmartSuite earns its spot for finance teams whose risk work touches procurement, IT, legal, and operations every week and shouldn't live in a tool nobody else opens.
➡️ Start a free SmartSuite trial or book a demo to see how your team can manage governance, risk, and compliance in one place.
⚠️ Disclaimer: This article is for general information and isn't legal advice. Regulatory dates, scope, and enforcement details change. Confirm with qualified counsel before making compliance decisions.
SmartSuite provides work platform for standardizing workflows in the following areas:
- Governance, Risk & Compliance
- IT & Service Ops
- Project / Portfolio Management
- Business Operations















