If your organization runs anything governance, risk, or compliance related, this guide walks through what a GRC audit actually involves, why it matters, how to run one without it turning into a fire drill, and what tools make the work less painful.
TL;DR
- A GRC audit is a structured review of how your governance, risk management, and compliance programs actually function together, tested against real evidence and not just policy documents.
- The reason why GRC audits matter is that they surface control gaps, policy drift, and unowned risks before regulators, customers, or an incident finds them first.
- The difference between internal and external audits is that internal audits are self-assessments run on your own schedule, while external audits are done by independent third parties, usually for certifications like SOC 2 or ISO 27001.
- The way you run an audit is by defining scope, pulling evidence, testing controls, interviewing the people doing the work, documenting findings with root causes, assigning owners and deadlines, and then following up.
- Tools that would help you in your GRC audit would be compliance automation platforms for certifications, enterprise GRC suites for large regulated organizations, and connected work platforms like SmartSuite for teams that want audit workflows tied to the rest of their operations.
What is a GRC audit?
A GRC audit is a review of how your governance structure, risk management program, and compliance obligations are actually functioning together.
But not separately: here, together is the word that matters.
Most organizations audit compliance controls in one spreadsheet, track risks in another, and handle governance at quarterly board meetings as if these three things don't depend on each other.
A GRC audit cuts across all of it because, in reality, the three are connected, even if your tech stack keeps them siloed.
When an auditor walks in (internal or external), they're really trying to answer four questions:
- Are the policies you wrote down actually being followed day to day?
- Do the controls you claim to have actually work when tested against real samples?
- Is the organization managing the right risks, at the right severity, with real owners assigned?
- Can you prove any of it with evidence that holds up under scrutiny?
If the answers are fuzzy, that's the audit's whole point. A clean audit report isn't really the goal. An honest one is.
Organizations that prepare well find and fix most of their gaps before the external auditor shows up. The audit then validates the clean state rather than discovering the mess.
I’ve seen many teams treat the audit itself as the discovery mechanism; however, they’re basically paying an external auditor to do internal work that should've happened six months earlier.
Why are GRC audits important?
Regulators don't care how busy you were last quarter.
Neither do enterprise customers reviewing your security posture before signing a contract, nor do partners who need to know that outsourcing critical work to you won't become their problem.
GRC audits exist because claims about governance, risk, and compliance need verification.
Otherwise, every vendor security questionnaire ever filled out would be a work of fiction.
A good audit surfaces things like:
- Missing controls you assumed were in place (surprisingly common once you actually look).
- Controls that exist on paper but nobody actually runs in practice.
- Risks that got logged once and never reviewed again after someone moved roles.
- Policies that have drifted so far from day-to-day practice that the two barely recognize each other.
- Framework gaps between your stated compliance posture and the standards you said you'd follow.
Audits also do something less tangible. They create accountability.
From what I’ve seen in the industry, when people know their work is going to be inspected, they tend to do it more carefully.
What are the different kinds of GRC audits?
There are two types of GRC audits: internal and external, and they serve different purposes.
- Internal GRC audits are run by your own team, or by a firm you contract directly.
The goal is self-assessment. You're looking for weak spots before someone external finds them.
Internal audits run more often, quarterly or bi-annually is common in regulated industries, and they're forgiving of messy in-progress work.
Nobody loses a certification because an internal audit surfaced a problem. In fact, this is the entire point of internal audits: finding issues.
- External GRC audits are run by an independent third party, usually tied to a certification (SOC 2, ISO 27001, PCI DSS) or requested by a regulator, investor, or major customer.
The auditor has no skin in the game whether you pass or fail, which is exactly why their report carries weight.
External audits typically happen annually, though some frameworks require surveillance audits more often.
As you might guess, the goal of internal audits is to catch the issues so external audits don't have to.
How can you conduct a GRC audit in your organization?
Running an internal audit isn't particularly mysterious once you've done one end-to-end. It’s also important to note that the sequence matters more than the tools:
Start with the scope
Pick the frameworks or standards you're auditing against (ISO 27001, SOC 2, NIST CSF, internal policy, whatever applies), the business units, the systems, and the time period. Write it down. Get sign-off.
Scope creep is one of the biggest reasons audits go off the rails.
Assemble the team
You need at least one person who knows the controls and at least one person who isn't responsible for operating them.
If the same person who writes the policy also tests the policy, you don't have an audit. You have a self-assessment with a different name.
Pull the evidence
For each control in scope, decide what would actually prove it's working.
Policies, logs, tickets, screenshots, meeting minutes, training records, system exports.
Your goal is to collect it and organize it under control.
This is where most programs lose the first two or three weeks of an audit cycle.
Test the controls
For each one, pick a sample and walk through it.
Did access reviews actually happen last quarter? Were vulnerabilities patched inside SLA? Did the incident response team run a tabletop exercise? Document what you found, including what you didn't find.
Interview the people running the work
Policies look great on paper. Ask an SRE on call what happens when a production incident fires at 3 AM, and you'll often hear a different story.
Both matter. Both go in the audit.
Write the findings
For each gap, rate it by severity and document the root cause. A finding without a root cause is just a complaint. Fixing the symptom without addressing the cause means you'll see the same finding again next cycle.
Assign owners and deadlines
Remediation without a named owner doesn't happen. You can treat this like any other project: owner, deadline, definition of done.
Follow up
Six months later, revisit the findings:
- Did the fixes stick?
- Did new gaps appear in the same area?
Close the loop before the next audit opens. That's the whole pattern.
Frameworks like OCEG's Red Book and Burgundy Book give you structured guidance if you want it, and CMMC, PCI DSS, and ISO/IEC 27001 each bring their own control catalogs. The mechanics don't really change.
What are the benefits of conducting a GRC audit?
The obvious benefit is avoiding penalties, especially if you work in the finance industry.
Fines, failed certifications, or lost deals. A good audit surfaces the issues before they become expensive.
Less obvious benefits usually matter more over time.
Audits force documentation to catch up with reality. Most organizations have some drift between what their policies say and what people actually do. The audit process pulls the two back together.
What are the common challenges in GRC audits?
Most audits don't fail outright. They just get messy. Here are the ones that actually trip up mature programs, not just beginners:
Framework overlap creating duplicate control testing
An organization carrying SOC 2 and ISO 27001 often has three overlapping access control requirements getting audited three separate times against three slightly different standards.
The underlying control is one thing.
The audit burden multiplies because most teams don't map their controls to multiple frameworks at once, so the same evidence gets collected three times a year.
Sample size theater
External auditors typically test samples of 5 to 10 records per control.
That's statistically thin. A control that fails 15% of the time has a decent chance of passing a sample of 10 purely by luck.
Passing an audit doesn't mean the control actually works.
It means it worked on the handful of records the auditor pulled. Internal teams that rely on external audit results for operational confidence get blindsided by this eventually.
Evidence staleness windows
Most external auditors reject evidence collected more than 90 days before the audit window opens.
Teams that collect evidence throughout the year and then try to "refresh" it in the final month end up with evidence that's technically compliant with the rule and practically useless for the period it's supposed to cover.
The refresh scramble itself often creates new findings.
Compensating controls that don't actually compensate
When a primary control fails, the standard move is to point at a compensating control and claim equivalent coverage.
Auditors are getting stricter on this.
Going into an audit with a clear list of which compensating controls have been validated as genuinely equivalent (and which haven't) saves a painful conversation later.
Cross-functional coordination breakdown
GRC audits touch security, engineering, HR, legal, finance, and operations. If these teams don't talk to each other routinely, the audit turns into a game of telephone.
Interviews contradict each other.
Evidence contradicts policy. Nobody's quite sure who owns a given control. The fix isn't a new tool.
It's standing meetings between the audit team and each domain owner at least a month before the audit window opens.
Scattered evidence sources
Screenshots in SharePoint. Ticket exports in email. Approvals in Slack DMs. Meeting notes in somebody's personal Notion.
It all works until the day the auditor asks for last March's change approvals, and three people need a week to piece them together.
Most programs don't fix this until after their first genuinely painful external audit.
What tools can you use for a GRC audit?
Teams running GRC audits tend to fall into one of a few tooling categories.
- Compliance automation platforms like Vanta, Drata, Sprinto, Secureframe, and Scytale focus heavily on certification readiness.
They automate evidence collection against specific frameworks (SOC 2, ISO 27001, and so on), connect to cloud and identity providers, and produce audit-ready reports.
These are a good fit if your main goal is getting certified quickly and your compliance program doesn't stretch much beyond the certifications themselves.
- Enterprise GRC suites like ServiceNow GRC, IBM OpenPages, MetricStream, and OneTrust are built for large regulated organizations.
They cover enterprise risk management, policy management, internal audit, third-party risk, and regulatory change management at real scale.
Powerful, but the price tags and implementation timelines match.
- Dedicated audit management tools like Optro (formerly AuditBoard) and Hyperproof sit in the middle, focused specifically on the audit workflow: planning, fieldwork, findings tracking, and remediation management.
- Spreadsheets still show up a lot at smaller organizations. They work until they don't.
The day they stop working is usually the day you realize a third of your audit prep depends on one person's local Excel file.
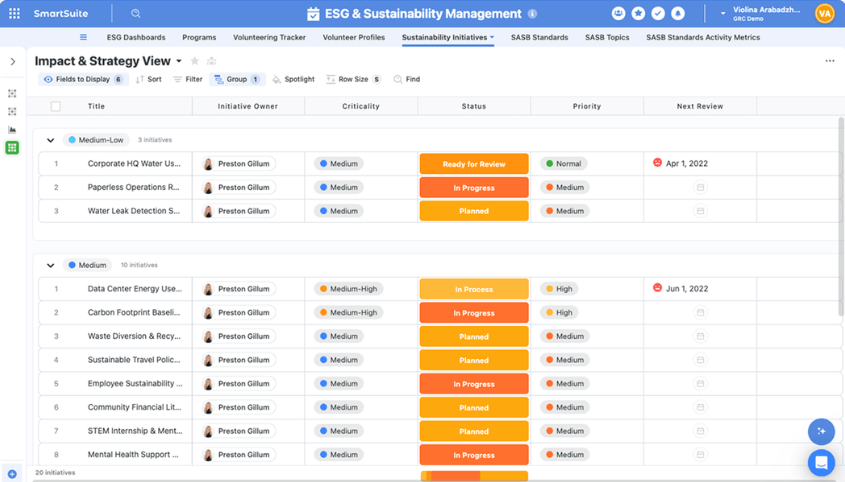
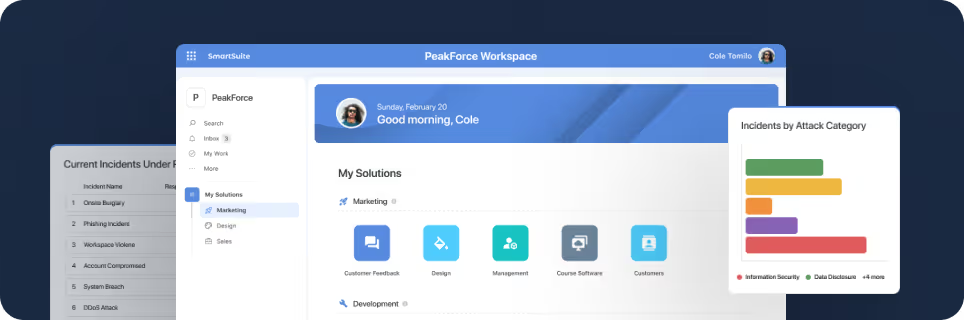
- Connected work platforms like SmartSuite are a different category entirely.
Instead of being a dedicated GRC tool, these tools let you build GRC workflows inside the same system that runs the rest of operations.
Risk registers, audit fieldwork, policy reviews, and remediation tasks can live next to project management, incident response, and vendor onboarding.
Now, where does SmartSuite fit?
Our platform takes the connected-work-platform approach: governance, risk, internal audit, compliance, third-party management, and operational resilience all live in one system, linked together with no-code workflows and relational data.
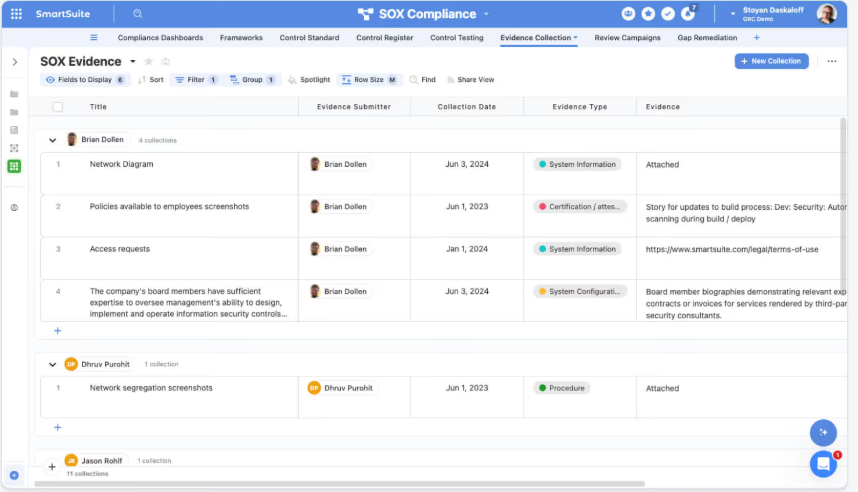
When a control fails during testing, you can trace it back to the risks it mitigates, the frameworks it maps to, the owner responsible, and the remediation task that's supposed to fix it, without jumping between five tools.
Internal audit teams can plan fieldwork, collect evidence, track findings, and monitor remediation inside the same workspace the rest of the business runs on, so audit evidence isn't scattered across SharePoint folders and inbox threads.
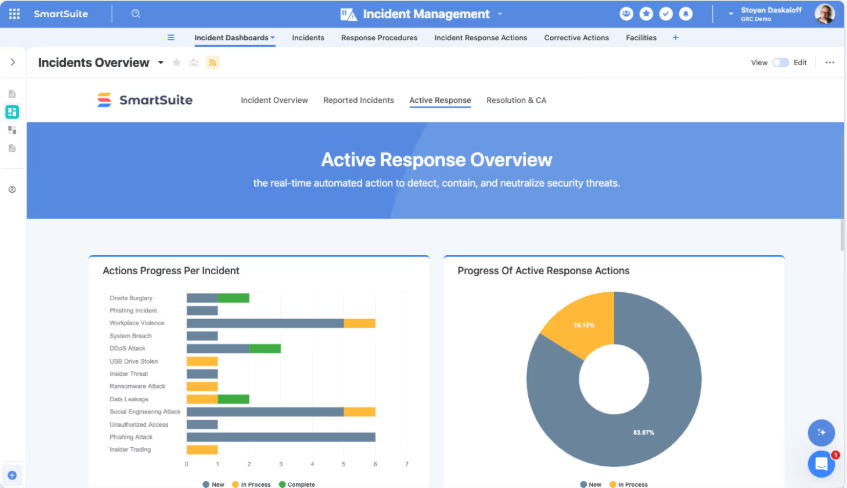
AI sits inside the workflows, summarizing vendor questionnaires, flagging anomalies in risk data, and drafting policy updates, while every change is logged for auditability.
Dashboards update in real-time as work moves, so your leadership doesn't wait three days for a status deck.
For mid-market teams and regulated financial institutions tired of either babysitting a spreadsheet-based audit program or paying enterprise GRC suite prices, it's a category worth putting on the shortlist.
Ready to run cleaner GRC audits?
Most teams shopping for GRC tools end up picking between two extremes: a certification-focused automation platform that handles SOC 2 well but nothing beyond it, or an enterprise GRC suite that handles everything but costs six figures a year and takes nine months to stand up.
If your audit process looks like pulling evidence from 7 different systems, chasing control owners for screenshots, pasting findings into a Word doc, and hoping the remediation tickets don't disappear into a Jira backlog, you're doing it the hard way.
But I believe that now there’s a middle ground.
SmartSuite brings risks, controls, audits, evidence, policies, vendors, and remediation into one connected workspace, with dashboards that stay current and AI that handles the rote parts.
Regulated organizations use our solution to replace spreadsheets and glue code with purpose-built GRC workflows, while mid-market companies use it to get audit-ready without enterprise GRC pricing.
Regardless of whether your team is building its first risk register or managing complex, multi-framework compliance across departments, SmartSuite gives you the flexibility to start where you are and grow without hitting a wall.
Start a free SmartSuite trial or book a demo to see how your team can manage governance, risk, and compliance in one place.
SmartSuite provides work platform for standardizing workflows in the following areas:
- Governance, Risk & Compliance
- IT & Service Ops
- Project / Portfolio Management
- Business Operations