Problem
Fragmented Workflows, Increasing Regulatory Pressure
Operating in one of the world’s most tightly regulated financial environments, Helaba Bank’s US and UK Information Security teams were managing cybersecurity assessments across multiple systems and processes.
Each regulatory cycle required coordination across stakeholders, with reporting and evidence collection involving significant manual effort. This created challenges around consistency, visibility, and scalability.
As regulatory obligations continued to expand, the complexity of maintaining audit readiness increased. What was once manageable evolved into a time-consuming process that limited efficiency and made it harder to maintain a clear, real-time view of risk.
Q1
Solution
From Fragmentation to Unified, Audit-Ready Workflows
When evaluating platforms, simplicity and usability were non-negotiable. The goal was to find a solution that could be implemented quickly without heavy configuration or reliance on external resources. SmartSuite stood out immediately.
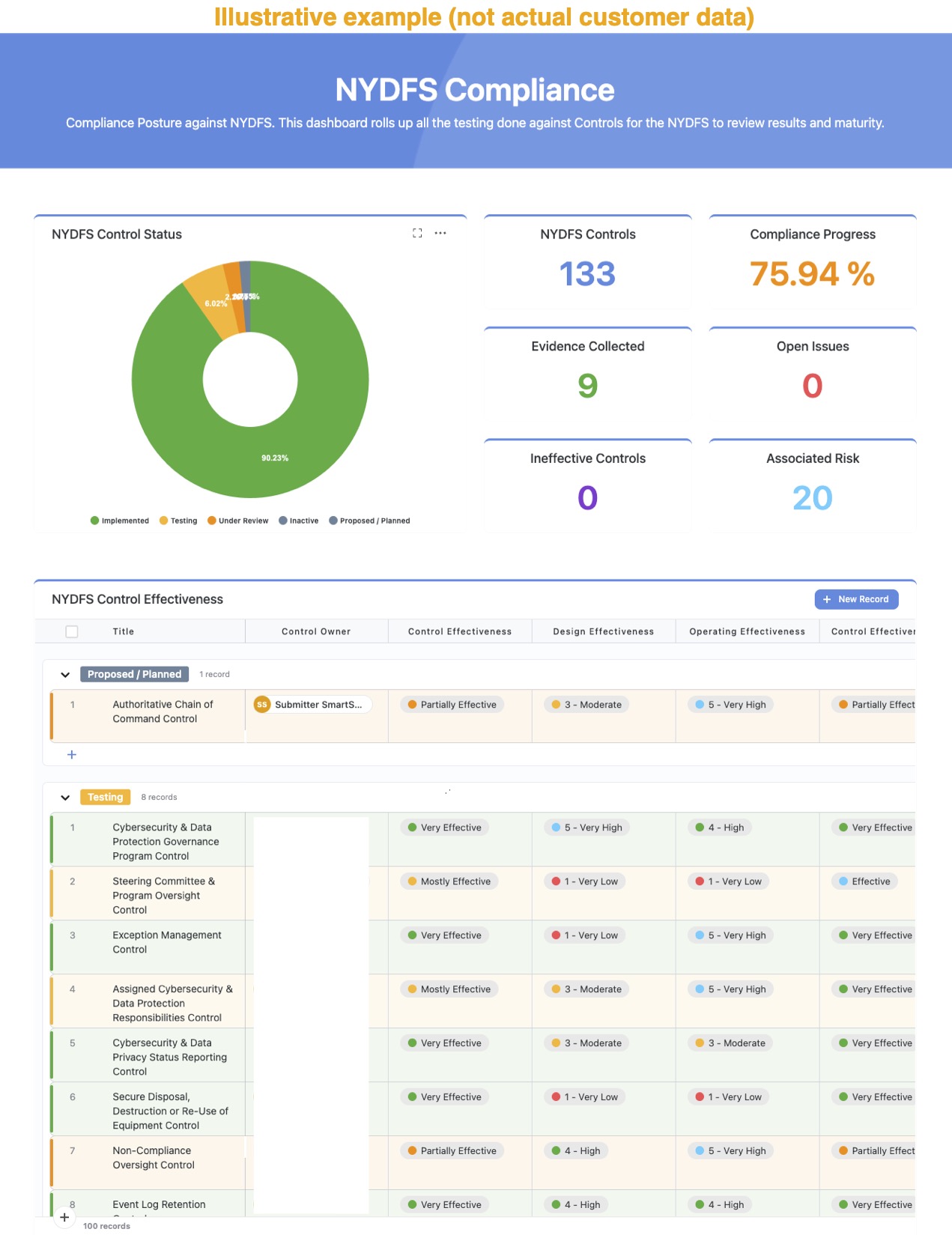
The transition to a centralized assessment model was straightforward. Instead of working across disconnected processes, assessments, evidence collection, and approvals were brought into a single system with full audit history.
Reporting, which previously required manual effort, is now generated in real time. Stakeholders can access up-to-date insights into assessment progress without waiting for reports to be compiled.
Regulatory requirements across multiple frameworks were consolidated into a unified control structure, reducing duplication and enabling more efficient reporting. Evidence can now be collected once and reused where applicable, streamlining audit preparation.
Adoption across the team was seamless, enabling users to quickly build and manage workflows without significant technical barriers.
Q2
Result
From Administrative Burden to Strategic Advantage
The impact on Helaba Bank’s assessment program was immediate, but the broader transformation was operational.
Where the team once spent time coordinating processes and compiling information, they now operate from a single, controlled source of truth. Assessment progress is visible at any moment, and audit trails are built in rather than reconstructed. Reporting is consistently available, accurate, and up to date.
Instead of reacting to regulatory demands, the team is now able to prepare proactively. A more structured approach to control management has improved consistency and reduced duplication across the program.
The success within Information Security has also driven expansion into adjacent areas, supporting a more connected and scalable approach to risk and compliance across the organization.Looking ahead, the focus is on further integration across processes to reduce redundancy and continue improving operational efficiency.















%2520(1).jpeg)


%2520(1).jpeg)


-min.jpeg)
.png)
.png)
-min.jpeg)



.png)
.png)




-min.png)
-min.png)
-min.jpeg)
-min.png)
-min.png)
-min.jpeg)
-min.png)



-min.jpeg)
-min.png)
-min.png)
-min.jpeg)
-min.png)
-min.png)

-min.png)
-min.png)
-min.jpeg)
-min.png)
-min.png)
-min.jpeg)
-min.png)
-min.png)
%2520(1).jpeg)
%2520(1).jpeg)
.png)
.png)
-min.jpeg)
.png)
.png)
%2520(1).jpeg)
-min.jpeg)
.png)
.png)
.jpeg)
.png)
.png)
-min.jpeg)
.png)
.png)
%2520(1).jpeg)


-min.jpeg)
.png)
.png)
-min.jpeg)
.png)
.png)



%2520(1).jpeg)
%2520(1).png)
%2520(1).png)
-min.jpeg)
%2520(1).png)
%2520(1).png)
-min.jpeg)
-min.png)
-min.png)
-min.jpeg)
-min.png)
-min.png)
-min.jpeg)
-min.png)
-min.png)
-min.jpeg)
-min.png)
-min.png)



-min.jpeg)
-min.png)
-min.png)




.png)
-min.png)
-min.jpeg)
-min.png)
-min.png)
-min.jpeg)
-min.png)
-min.png)
-min.jpeg)
-min.png)
-min.png)
-min.jpeg)
-min.png)
-min.png)
-min.jpeg)
-min.png)
-min.png)



-min.jpeg)
-min.png)
-min.png)






.jpeg)
.png)
.png)
.jpeg)
.png)
.png)
.jpeg)
.png)
.png)
.jpeg)
.png)
.png)

.png)
.png)







%2520(1).jpeg)


%2520(1).jpeg)
%2520(1).png)
%2520(1).png)
%2520(1).jpeg)
.png)
.png)



%2520(1).jpeg)
%2520(1).png)
%2520(1).png)
-min.jpeg)
.png)
.png)

.png)
.png)



%20(1).jpg)
-min.png)
-min.png)
-min.jpeg)
-min.png)

-min.jpeg)
-min.png)
-min.png)
-min.jpeg)
-min.png)
-min.png)



-min.jpeg)
-min.png)
-min.png)



























-min.jpeg)
-min.png)
-min.png)
.jpg)
-min.png)
-min.png)












-min.jpeg)
-min.png)
-min.png)
























.jpeg)
.png)
.png)



.jpg)
.png)
.png)
.jpg)
.png)
.png)

