In 2026, GRC has become the operating model for any organization that needs enterprise risk management, internal controls, and compliance programs working together rather than against each other.
In this guide, I'll break down what GRC really means in practice, how it works, where organizations get stuck, and what types of tools exist to support it.
What is GRC?
Governance, Risk, and Compliance (GRC) is a discipline that unifies how organizations manage policies, identify and mitigate risks, and meet regulatory obligations, all under one coordinated strategy instead of three separate silos.
The term was first coined by OCEG (the Open Compliance and Ethics Group) in 2003, but the practice itself grew out of decades of corporate governance failures, from the financial scandals that produced COSO's internal control frameworks in the 1990s to the Sarbanes-Oxley Act of 2002.
Instead of treating each discipline as its own separate function (which is how most companies handled it for decades), GRC aligns all three, so they work toward the same business objectives.
OCEG defines this as "principled performance," meaning an organization reliably achieves its goals, manages uncertainty, and acts with integrity, all at the same time.
The idea is simple:
- Your policies should reflect real risks.
- Your enterprise risk management program should account for regulatory requirements.
- And your compliance efforts should feed back into how the organization is governed.
When those three pillars are connected, decision-making gets faster, risk visibility improves, and you stop duplicating effort across departments.
Without GRC, you end up with legal doing one thing, IT doing another, finance managing their own risk register, and nobody seeing the full picture.
That's not just inefficient. It's dangerous, especially in regulated industries where gaps between departments can lead to failed audits, control deficiencies, or regulatory penalties.
To us and many companies that we work with, GRC isn't a single tool or a checklist.
It's a discipline, a mindset, and increasingly, a category of software built to make enterprise-wide risk and compliance programs manageable at scale.
What does GRC stand for?
GRC stands for governance, risk management, and compliance.
- Governance refers to the policies, rules, and decision-making frameworks an organization puts in place to run itself responsibly.
It defines who's accountable for what, how resources are managed, and how the board and senior leadership set direction.
Think of it as the control environment, the tone at the top that shapes everything from ethics policies and conflict-of-interest rules to how information flows between leadership and the rest of the organization.
Frameworks like COSO's Internal Control framework provide a structured model for building this governance layer.
- Risk management is the process of identifying, assessing, and responding to threats that could affect the business.
These can be financial, operational, legal, strategic, or cybersecurity-related.
The goal of enterprise risk management (ERM) isn't to eliminate every risk (that's impossible) but to understand which risks matter most and take deliberate steps to reduce them.
A strong ERM program helps you predict problems before they happen and respond quickly when they do, whether that's a data breach, a supply chain disruption, or a regulatory change.
Standards like ISO 31000 and NIST's Risk Management Framework give organizations structured approaches for building these programs.
- Compliance means following the rules.
That includes external laws and regulations, like the EU's General Data Protection Regulation or the Sarbanes-Oxley Act (which reshaped corporate financial reporting after the Enron scandal in 2001).
It also covers internal policies the organization sets for itself.
Compliance programs exist to make sure the company doesn't just have policies on paper but actually enforces them through internal controls, evidence collection, and continuous monitoring across every department, role, and process.
Most organizations have practiced governance, risk management, and compliance in some form for years.
The problem is they did it in silos, with no shared data, no common framework, and no unified reporting.
GRC brings all three together so they reinforce each other instead of operating in isolation.
Why is GRC important?
The reason why GRC is important is that, without a coordinated GRC program, every department is flying blind in its own corner, making decisions based on incomplete information, duplicating work that's already been done elsewhere, and leaving gaps that only surface when an auditor or a regulator comes knocking.
Here’s what GRC can do for your organization:
- It connects your data to your decisions. When governance, risk, and compliance feed into the same system, leadership gets a real-time view of what's happening across the business.
That means faster decisions grounded in actual risk data, not quarterly reports assembled by hand from four different spreadsheets.
Instead of waiting weeks for a cross-departmental status update, you can see where the organization stands right now and act on it.
- It kills duplicated effort. In most mid-size companies, compliance is running its own process, IT security is running a parallel one, legal has a third, and finance has a fourth.
Each team is documenting controls, tracking risks, and generating reports independently, often covering the same ground.
GRC collapses that overlap. When your risk register, control library, and audit schedule live in one place, you stop paying five teams to do variations of the same work.
This is why OCEG's GRC Capability Model emphasizes integration as the baseline requirement, not something you get to eventually.
- It strengthens your security and regulatory posture together. Cybersecurity doesn't exist in a vacuum. A data breach isn't just a technical problem.
It's a compliance problem, a reputational problem, and potentially a legal problem all at once.
GRC programs tie security controls directly to the regulations they're meant to satisfy (GDPR, HIPAA, PCI-DSS, and others), so when your IT team closes a vulnerability, that action automatically maps back to the regulatory requirement it fulfills.
That connection is what keeps organizations out of trouble when auditors start asking questions.
- The cost of not having GRC is real and measurable. Organizations without a coordinated program tend to discover their gaps the hard way: a failed audit, a regulatory fine, a breach that could have been caught earlier, or a compliance deadline missed because nobody knew it was someone's responsibility.
Those aren't hypothetical risks. They're the exact scenarios that push companies to implement GRC in the first place.
And the longer you wait, the more expensive the cleanup becomes, because retroactive compliance always costs more than proactive governance.
How does GRC work?
Contrary to popular beliefs, GRC doesn't work through a single department or a single document.
It's a cross-functional effort that touches every layer of the organization, from the board down to individual contributors.
Here's how it comes together in practice:
GRC starts with stakeholders across the business
GRC requires buy-in and participation from multiple teams. Your C-suite weighs potential threats every time they make a strategic call.
Legal works to keep the company out of regulatory trouble. Finance tracks whether reporting obligations and audit requirements are actually being met.
HR sits on sensitive personnel data that carries its own compliance burden. And IT is responsible for keeping infrastructure, applications, and customer data safe from cyberattacks.
None of these groups can do GRC alone, and when they try, gaps form fast.
Most mature organizations structure this collaboration around the three lines of defense model, a widely adopted approach endorsed by ISACA and the IIA (Institute of Internal Auditors).
The first line is operational management, the people who own and manage risks day to day.
The second line is risk management and compliance oversight, the teams that set policies, monitor controls, and flag issues.
The third line is the internal audit, providing independent assurance that the first two lines are actually working.
When all three lines are operating with shared data and clear accountability, the GRC program has structural integrity. When they're disconnected, you get blind spots.
GRC is structured around a framework
A GRC framework is the blueprint an organization uses to define its key policies, map them to business goals, and create a shared understanding across teams.
Think of it as the connective tissue that links risk appetite, compliance obligations, and the overall control environment into one model.
Once a framework is adopted, stakeholders use it to design workflows, assign responsibilities, and measure outcomes. Some companies build their own frameworks from scratch.
Others adopt established ones and customize from there.
Common choices include COSO's Enterprise Risk Management framework, COBIT for IT governance, ISO 31000 for risk management, and the NIST Cybersecurity Framework for IT and security risk.
GRC matures over time
GRC maturity is a measure of how tightly these three disciplines are woven into the way an organization actually operates.
A company with low GRC maturity might have each department running its own processes with no shared data, no cross-team visibility, and no consistent reporting.
A mature GRC program, on the other hand, looks like cost-efficient operations, proactive risk identification, and consistent compliance, with every team working from the same playbook.
Getting there takes deliberate investment in process design, technology, and culture.
GRC follows a continuous cycle
The GRC Capability Model (developed by OCEG) gives organizations a structured way to think about this cycle. You learn about your company's context, values, and risk appetite.
You align your strategy, policies, and actions with those realities. You perform, taking action and keeping a close eye on whether anything unexpected shifts mid-course.
And then you review, revisiting your approach as regulations shift, risks evolve, or business goals change. It's not a one-time project.
It's an ongoing loop, and the organizations that treat it that way are the ones that stay ahead of regulatory change instead of reacting to it.
What are some of the challenges of GRC implementation?
Knowing what GRC is and actually implementing it are two very different things.
Here are the obstacles I see organizations run into most often:
- Getting people to change how they work. GRC generates insights that should drive faster, smarter decisions.
But acting on those insights requires a real commitment to change management.
Without it, risk reports sit in inboxes and nothing moves.
Leaders need to be willing to adjust processes, reallocate resources, and follow through on what the data tells them, even when it means disrupting established workflows.
- Cleaning up fragmented data. Most organizations have spent years letting every team build its own data habits, its own spreadsheets, and its own systems of record.
Bringing all of that together under an integrated risk management program surfaces a mess of duplicates, inconsistencies, and conflicting records.
Data management becomes a massive undertaking before you can even start getting value from the unified view GRC promises.
- Building a framework that actually covers everything. A partial GRC framework is almost worse than no framework at all.
If your framework doesn't connect governance policies, the risk register, internal controls, and compliance monitoring into a system that adapts as regulations change, you end up with fragmented implementation that creates blind spots.
The framework needs to be complete, living, and flexible enough to evolve alongside your regulatory environment.
- Creating an ethical culture from the top down. GRC isn't just a process. It's a culture. And building a culture of ethical accountability across every level of an organization takes serious effort.
Senior leadership has to set the tone, model the behavior, and make sure information reaches every team, not just the compliance department.
- Keeping communication clear and consistent. GRC implementation lives and dies on communication.
If compliance teams, leadership, and frontline employees aren't sharing information openly, then creating policies, making decisions, and coordinating responses becomes exponentially harder.
Transparency isn't optional here. It's a prerequisite.
How can you define and implement a GRC strategy for your organization?
Implementing GRC isn't something you do in a weekend. It's an iterative process that gets better over time.
But there's a clear path that makes it more manageable:
Start by defining what you're trying to solve
Every GRC strategy should begin with clear goals.
- Are you trying to reduce the risk of non-compliance with data privacy laws like GDPR or HIPAA?
- Improve audit readiness for SOX or ISO 27001?
- Get better visibility into third-party risk across your vendor portfolio?
The answer shapes everything that follows, from framework selection to tool choice.
Audit your current state
Before building anything new, take stock of what processes, tools, and frameworks you already have in place.
Most organizations aren't starting from zero.
They're starting from a scattered collection of spreadsheets, standalone tools, and manual workflows that sort of work but don't talk to each other.
Map your existing internal controls, risk registers, and compliance processes so you can identify the gaps and redundancies before you plan what to fix first.
Get senior leadership fully committed
GRC can't be a middle-management initiative.
If the CEO, CRO, CCO, CIO, and board aren't actively behind the program, it won't get the resources, attention, or cultural support it needs to succeed.
Leaders set the tone at the top. They define risk appetite.
And they make the hard calls when GRC insights conflict with short-term business goals.
Get buy-in across the entire organization
This is the part most companies underestimate.
If employees at every level don't understand why GRC matters and how it affects their work, control failures slip through, no matter how good your framework looks on paper.
GRC has to feel like everyone's responsibility, not just compliance's.
The three lines of defense model only works when all three lines actually operate with shared understanding.
Assign clear roles and ownership
The board provides oversight and approves the GRC framework. The CRO manages day-to-day risk governance.
The CCO handles compliance. The CIO and CTO manage technology risk. Finance, legal, HR, IT, and line-of-business managers all play a role.
But none of this works unless every person knows exactly what they're responsible for and how to escalate issues when something goes wrong.
Pick the right tools
Relying on spreadsheets and word processors for GRC is a recipe for manual tracking that can't scale, can't report accurately, and can't keep up with regulatory change.
GRC software gives you the ability to manage risk registers, map controls to regulatory frameworks, track the policy lifecycle, and generate audit-ready reports from one system.
Test before you scale
If I were you, I wouldn’t roll out GRC across the entire organization on day one. You should pick a single team or a single workflow as your pilot.
See if the framework holds up, if the tools work as expected, and if the workflows make sense.
The goal is to fix what's broken while the blast radius is still small, then expand.
What are the different use cases of GRC?
GRC isn't limited to one industry or one department.
It shows up wherever organizations need to balance performance with accountability.
Here are the main use cases of GRC:
Regulatory compliance and audit readiness
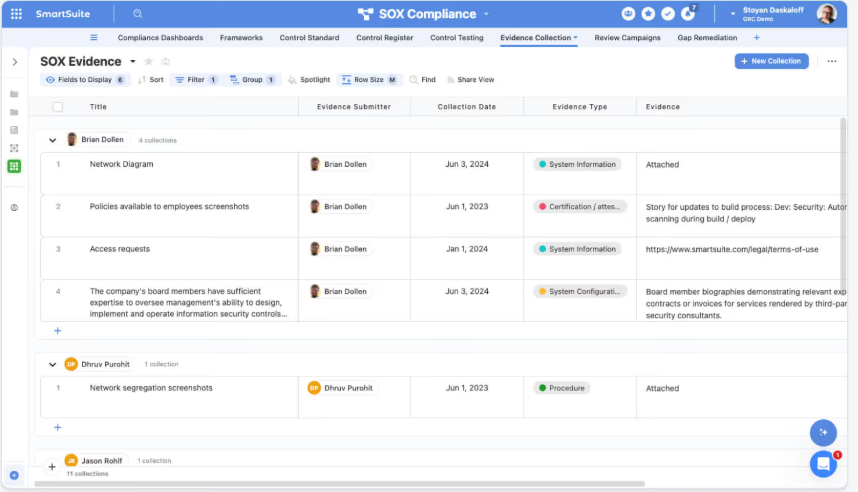
This is the most common entry point. Organizations in financial services, healthcare, and government need to prove they're following specific laws and standards like the Sarbanes-Oxley Act, HIPAA, GDPR, PCI-DSS, and industry-specific mandates.
A GRC program centralizes evidence collection, control testing, and audit preparation so you're not scrambling every time an internal or external auditor shows up.
For SOX compliance alone, this means tracking control scoping, testing, deficiency management, and certification in one connected workflow.
Cybersecurity and IT risk
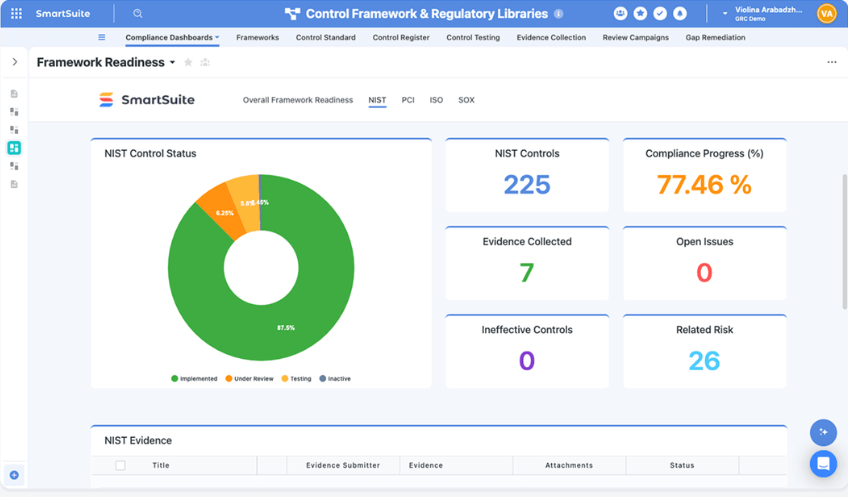
As cyber threats grow more complex, IT teams use GRC frameworks alongside standards like the NIST Cybersecurity Framework and ISO 27001 to connect security controls to business risk.
That means mapping vulnerabilities to the assets they affect, tracking remediation, and proving to regulators that your security posture meets required standards.
In practice, this often involves maintaining a unified view of cyber risks, incidents, vulnerability management, and control effectiveness.
Third-party and vendor risk management
Most companies rely on dozens (sometimes hundreds) of external vendors. Each one introduces risk, from data handling and security posture to regulatory compliance.
GRC gives you a structured way to manage the full vendor lifecycle: onboarding, due diligence, ongoing monitoring, and remediation, all assessed against your compliance requirements and risk tolerance.
Operational resilience and business continuity
When something goes wrong (a system outage, a natural disaster, a supply chain failure), GRC programs help organizations respond.
Business continuity planning, business impact analysis, incident management, and recovery workflows all fall under the GRC umbrella.
ESG and sustainability reporting
Environmental, social, and governance (ESG) reporting is becoming a regulatory requirement in many regions, including under the EU's Corporate Sustainability Reporting Directive (CSRD).
GRC programs increasingly include ESG tracking, disclosure management, and KPI reporting alongside traditional compliance work.
AI governance
This is a newer use case, but it's growing fast as regulations like the EU AI Act take shape.
As organizations adopt AI tools across their operations, they need structured programs to manage the risks that come with it: model inventories, bias monitoring, regulatory compliance, and lifecycle tracking.
GRC provides the framework to govern AI adoption responsibly.
What are the different types of GRC software tools?
There's a wide range of software that falls under the GRC category.
Not every tool does the same thing, and understanding the differences matters when you're evaluating options.
Dedicated GRC platforms
These are purpose-built systems designed to manage governance, risk, and compliance workflows end to end.
They typically include risk registers, control mapping, audit management, policy lifecycle management, and compliance tracking, all in one place.
The best ones connect these workflows so a change in one area (say, a failed control test) automatically updates related records in the risk register, the audit plan, and the remediation queue.
User and access management tools
These tools focus specifically on controlling who can access what within your organization.
Granular permissions, role-based access, and identity governance all help ensure sensitive data stays protected, and audit trails stay clean.
Security information and event management (SIEM) tools
SIEM software helps IT and security teams detect threats in real time by aggregating and analyzing security events from across your infrastructure.
While SIEM isn't a full GRC solution on its own, it feeds critical data into the risk and compliance side of a GRC program.
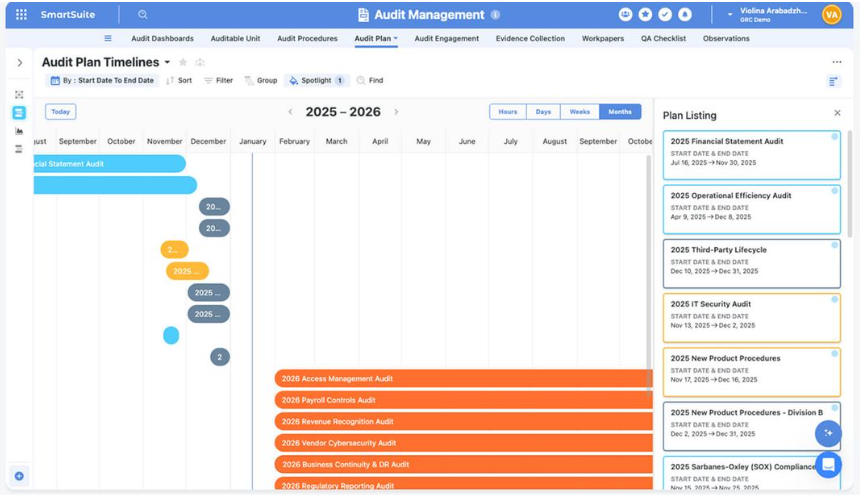
Audit management software
These tools help organizations plan, execute, and track internal audits.
They're especially useful for benchmarking GRC program performance against stated objectives and identifying areas that need improvement.
Workflow and work management platforms with GRC capabilities
This is where things get interesting. Some platforms weren't built as traditional GRC tools but offer enough flexibility to manage GRC workflows alongside other business operations.
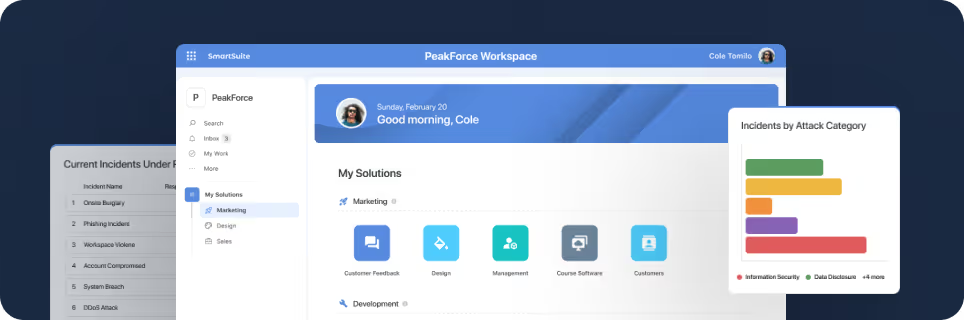
SmartSuite (that’s us) falls into this category, and it's worth a closer look if you want GRC capabilities without locking yourself into a rigid, compliance-only system.
SmartSuite is an AI-native work management platform that lets you manage GRC, audits, incidents, and remediation inside one connected workspace instead of spreading those workflows across disconnected tools.
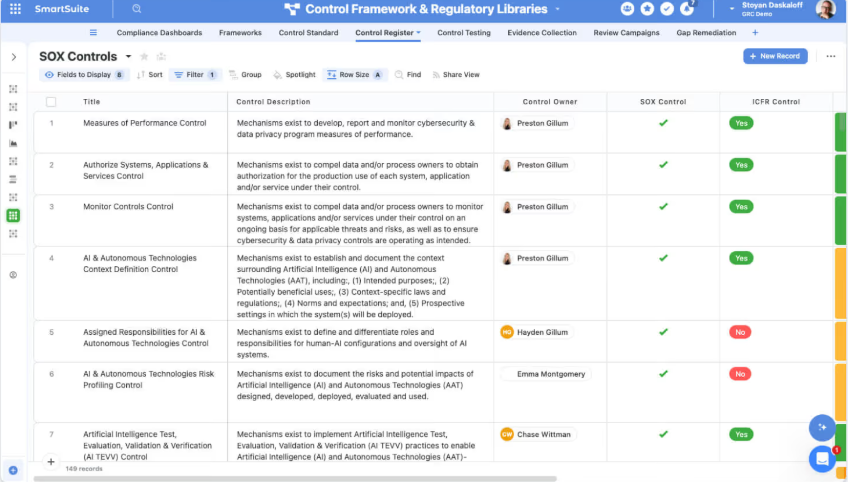
What makes our platform different from traditional GRC tools is that it ties compliance work to business operations, so risk registers connect to control libraries, audit schedules link to findings, and remediation tasks stay visible across teams.
The platform is fully no-code, meaning GRC teams can design their own data models, build custom dashboards, and configure role-specific views without waiting on developers or consultants.
AI is built directly into workflows for things like summarizing vendor questionnaires, flagging gaps in evidence collection, surfacing risk patterns, and generating policy drafts.
It covers a wide range of GRC use cases out of the box, including enterprise risk management, cyber risk, internal audit, third-party risk, SOX compliance, operational resilience, AI governance, and ESG tracking.
And because it's a broader work management platform, teams outside compliance (IT, operations, HR, finance) can use the same system for their own workflows, which eliminates the data silos that make most GRC implementations fragile.
Which type of GRC tool actually fits your organization?
Each category of GRC software serves a different need.
Dedicated GRC platforms like ServiceNow GRC, Archer, or Optro (formerly AuditBoard) are built for large enterprises with established compliance teams and mature risk programs.
They're powerful, but they can be expensive, slow to configure, and rigid once implemented.
SIEM tools and access management platforms handle specific pieces of the puzzle, mainly cybersecurity monitoring and identity governance, but they don't manage the full GRC lifecycle on their own.
Audit management software helps with internal audit workflows, but it typically operates in isolation from risk registers, policy management, and compliance tracking.
And then there are certification-focused tools like Vanta, Drata, and Sprinto that do a great job of helping startups get SOC 2 or ISO 27001 certified fast, but they tend to stop there.
Once you need to manage broader risk programs, third-party oversight, operational resilience, or cross-departmental compliance, those tools start to feel limiting.
If what you're really after is a platform that connects governance, risk, compliance, and audit workflows to the rest of your business without forcing you into a rigid system or a six-figure contract, that's where SmartSuite fits.
It's built for organizations that don't just want to pass audits but want GRC wired into how their teams actually operate day to day.
Here's what you get when you try SmartSuite:
- A connected GRC workspace that links risks, controls, audits, incidents, policies, and remediation in one system instead of scattered tools.
- No-code customization so your team can build and adapt GRC workflows, dashboards, and data models without developers.
- AI built into workflows for vendor questionnaire summaries, risk scoring, evidence gap detection, policy generation, and incident analysis.
- Real-time dashboards and reporting tied to live data, so leadership always sees the current risk posture without waiting for manual exports.
- Coverage across GRC use cases, including enterprise risk, cyber risk, internal audit, third-party risk, SOX, operational resilience, AI governance, and ESG.
- A 14-day free trial with no credit card required, so you can test real workflows before making any commitment.
Curious to see it in action?
Start a free SmartSuite trial or book a demo to see how your team can manage governance, risk, and compliance in one place.
Read More
- 10 Best Riskonnect Alternatives For GRC In 2026
- Riskonnect Pricing: Is It Worth It In 2026?
- 10 Best MetricStream Alternatives for GRC in 2026
- MetricStream Pricing: Is It Worth It In 2026?
- Top 10 Compliance AI Alternatives & Competitors
- Compliance AI Pricing: Is It Worth It?
SmartSuite provides work platform for standardizing workflows in the following areas:
- Governance, Risk & Compliance
- IT & Service Ops
- Project / Portfolio Management
- Business Operations















