In this guide, I'll cover what internal audit management is, the types of audits you'll run into, the frameworks worth knowing, and the tools that fit different audit functions in 2026.
TL;DR
- Internal audit isn't compliance. It's the third line of defense, giving the board independent assurance over how management actually runs risk, controls, and governance.
- Audits come in many flavors. Financial, operational, IT, compliance, integrated, ESG, AI, and investigative audits each test different parts of the business with different methods.
- Risk-based planning drives everything. A real annual plan tells you what to audit, when, and why, instead of just rolling last year's plan forward.
- The work runs in three connected stages. Planning and scoping, fieldwork and documentation, then reporting and follow-up. Each one feeds the next instead of running in a clean line.
- Tooling matters more than people think. Spreadsheets break under pressure, enterprise audit platforms cost real money and take time to implement, and connected work platforms like SmartSuite give mid-market teams a serious middle option.
What is internal audit management?
Internal audit management is the work of running an internal audit function end-to-end.
That covers building the audit universe, setting an annual plan, executing engagements, documenting findings, and tracking remediation through to closure.
The keyword is independent.
Internal audit owns neither risk nor controls.
Its job is to tell the audit committee, the board, senior leadership, and (when it matters), external regulators, whether the people who own those things are doing them well.
This is the third line of defense in the classic Three Lines model:
- First line is operational management, the people doing the actual work.
- Second line is risk and compliance, the people setting the rules and watching for breaks.
- Third line is internal audit, the people independently checking that lines one and two are doing what they claim.
Most teams I've seen split internal audit work into four moving parts: audit universe management, annual planning, fieldwork, and reporting plus follow-up.
When people say "internal audit management," they usually mean the operating system that holds those four parts together.
What are the different types of internal audit management?
Different audit types test different parts of the business.
- Financial audits look at the integrity of financial reporting, the controls behind it, and whether the numbers tie out. SOX engagements live here for public companies.
- Operational audits look at process efficiency, quality, and whether teams are actually hitting their objectives. Less about pass or fail, more about "is this working as designed?"
- IT and cyber audits test access controls, change management, system reliability, and the security posture sitting underneath everything else.
- Compliance audits check whether the organization is meeting its legal and regulatory obligations. Think DORA for EU financial firms, HIPAA for healthcare, FFIEC guidance for US banks.
- Integrated audits combine two or more of the above in one engagement. A revenue cycle review that tests financial controls, the IT systems running them, and the process steps in between.
- ESG and sustainability audits are newer ground. They test the data behind the disclosures companies are now making under CSRD, climate reporting rules, and supply chain regulations.
- AI audits are even newer. The methodology is still being figured out, but the work usually covers model inventories, training data lineage, bias testing, governance committees, and ongoing monitoring.
- Investigative audits kick in when something's already gone wrong: fraud, ethics breaches, whistleblower complaints. These follow a different rulebook entirely.
The mix you actually run depends on industry, regulatory exposure, audit committee priorities, and what last year's external auditors flagged.
A regional bank's plan looks nothing like a SaaS company's plan.
Why is internal audit management important?
The economics of audit are simple: who finds the problem first determines how expensive it gets.
A control failure caught by your own team is a learning moment.
The same failure caught by a regulator, an external auditor, the audit committee in panic mode, or a customer reading a breach disclosure, is something else entirely.
A working internal audit function does several things at once:
- The board gets independent eyes on the business.
- Management gets early warning before small issues turn into reportable ones.
- Regulators, customers, and insurers see a documented assurance trail when they ask for one.
- First-line teams behave differently knowing an audit will be looking, which lifts the control environment as a side effect.
➡️ Companies that mapped their DORA exposure early in 2024 walked into the January 2025 deadline ready.
The ones that didn't most likely ended up running audit work and remediation in parallel, which is usually a recipe for missed deadlines and burnt-out teams.
According to statistics, DORA applies to approximately 22,000 financial entities across the EU and has been enforceable since January 17, 2025. Per Deloitte's Wave 3 survey on DORA operational resilience, only 50% of financial institutions expected to reach full compliance by the end of 2025, while 38% were targeting 2026.
What are the benefits of internal audit management?
The payoff from a real audit function isn't always visible engagement by engagement. It compounds.
Here are the benefits of internal audit management:
- Earlier issue detection, before something becomes a reportable event.
- Cleaner board reporting, because the audit committee gets one source of truth instead of three slide decks that don't agree with each other.
- Stronger control environments, since teams behave differently when they know an audit is going to look at the work.
- Lower cost of compliance, because mapped controls can serve multiple frameworks at once instead of being tested separately for each.
- Better external audit relationships, because well-run internal audit takes work off the external auditor's plate, and that often shows up in the fee.
- Faster M&A diligence, when a clean audit trail and a documented control environment shorten the buyer's review cycle.
- Talent retention in finance and risk teams, because nobody wants to work somewhere with constant fire drills and no internal controls.
The compounding effect is the real prize.
Organizations that take audit seriously end up taking controls seriously, which usually means fewer fires, which usually means people can do their actual jobs.
How can you approach internal audit management?
Different functions take different shapes, and there isn't one universally right answer.
The choice usually comes down to two things:
- Where does the risk in your business concentrate?
- What kind of audit function does your board want?
If you're a regional bank, you live and die by financial reporting and regulatory compliance, so your audit function tilts toward integrated SOX-style work and IT general controls.
If you're a SaaS company, your function probably tilts toward cyber, vendor risk, and revenue recognition.
The plan has to mirror where the risk actually sits in the business, not where it's easiest to find.
Beyond risk concentration, the second piece is the independence model.
Some boards want a fully in-house function that knows the business inside and out.
Others go co-source or fully outsource, with external specialists running some or all of the work.
There's no wrong answer, but the model you pick shapes hiring, budget, software, and how engagements get scoped from the start.
➡️ A common failure mode is setting up a function too small for the risk profile. A 200-million-dollar bank with one auditor and a spreadsheet isn't going to satisfy regulators, no matter how talented that auditor is.
Regulators expect a bank's internal audit function to be "commensurate with its size, the nature of its operations and the complexity of its organisation."
The audit functions I've seen work well do four things:
- They build the plan from a real risk assessment.
- They tie every engagement to a business objective.
- They keep findings on the table until they're truly closed.
- They report in plain language so the board can act on what they hear.
How to conduct an internal audit management assessment
The textbook version of this process has five linear steps: plan, fieldwork, report, follow-up, and monitor.
The version that actually plays out inside a working audit function is messier, with stages overlapping and feeding each other instead of running one after the next.
I'll break it into three working stages that capture how the work tends to flow.
Planning and scoping
Building the audit universe is step one: every entity, process, and risk that could be audited gets logged.
Each item picks up a risk rating, usually a mix of inherent risk, residual risk, and coverage history.
From there, the annual plan pulls engagements based on rating, regulatory pressure, and audit committee input.
For each engagement, you scope down to what's in and what's out, draft a planning memo, and align with management on timing and deliverables.
Scoping is where most engagements go wrong.
Too broad and you can't finish. Too narrow and you miss the thing that mattered most.
Fieldwork and documentation
Fieldwork is what people outside audit usually picture when they hear the word.
It's where you walk through processes, interview owners, request evidence, sample transactions, and test controls against criteria.
A few practitioner-level details matter here:
- Walkthroughs aren't testing. They confirm you understand the process. Testing comes after.
- Sampling needs a methodology that survives review; "we picked a few" isn't one.
- Workpapers need to stand on their own. Anyone reading them six months later should reach the same conclusion you did.
- Review notes from senior auditors stay in the record as evidence that supervisory review actually happened.
Findings get drafted as you go, not at the end.
The longer a finding sits in someone's head before it gets written down, the more context gets lost.
Reporting, follow-up, and closure
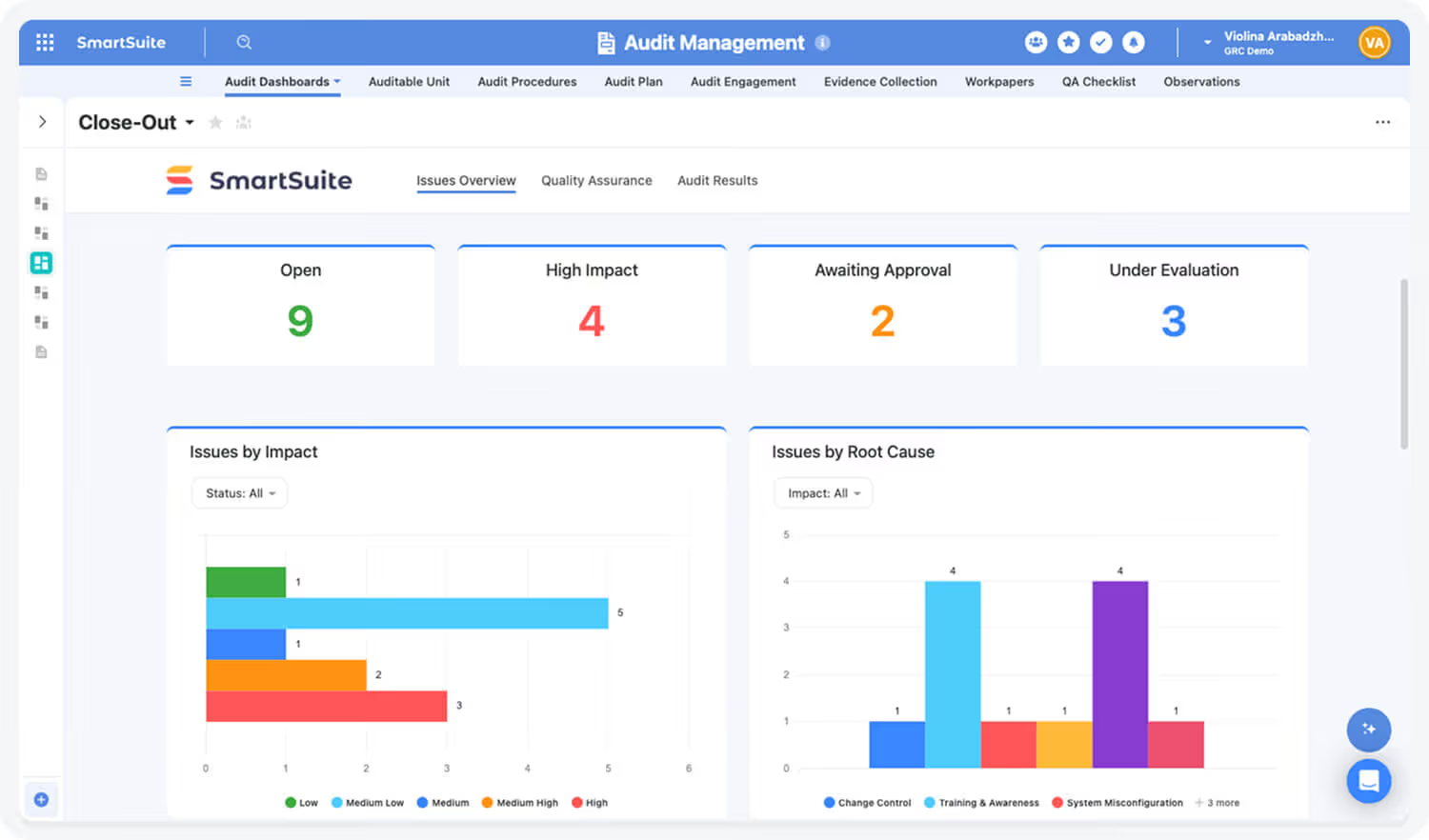
The audit report is the visible artifact. After the report comes the work that decides whether the audit truly mattered: tracking, escalation, sign-off, and final closure of findings.
Each finding gets a root cause, a recommendation, a management response, an owner, and a target date.
After that, the audit team monitors remediation through to closure.
A finding that's been "in progress" for 18 months has stopped being a finding. It's a control gap the business has decided to live with, which is a different conversation entirely.
The stages feed each other. Closed findings update the audit universe, which updates the risk rating, which feeds next year's plan.
💡 The most established audit functions layer continuous auditing over the annual plan.
Automated testing on high-risk controls (access reviews, journal entry exceptions, vendor onboarding, segregation of duties) shows up in the audit dashboard on its own, instead of waiting for someone to pull it each cycle.
What are the different internal audit management frameworks?
Audit functions usually blend a few based on what their regulators expect, what their boards are familiar with, where the function operates, and how the team has historically been trained.
Here are the frameworks worth knowing:
- The IIA's Global Internal Audit Standards are the closest thing to a global standard for internal audit work. Released in January 2024 and effective January 9, 2025, they replaced the 2017 Standards and now cover everything from purpose and ethics through engagement-level methodology.
- COSO Internal Control – Integrated Framework is the dominant control framework, especially for SOX work. Most financial controls testing maps back to COSO's components and principles.
- ISO 19011 is the international guideline standard for auditing management systems. If your business runs on ISO certifications like 9001 or 27001, this is the methodology your auditors will recognize.
- COBIT shows up heavily in IT audits, especially in regulated industries. It maps IT processes to business objectives in a way external auditors can follow.
- The Three Lines model isn't strictly a framework, but it's the mental model most audit committees expect you to use when explaining how the audit function fits into the broader assurance picture. The IIA updated it from the older "Three Lines of Defense" position paper in July 2020.
What kind of tools can you use for internal audit management?
The tooling question depends on the size of the function, the regulatory pressure on the business, the budget the audit committee is willing to release, and the maturity of how the function operates today.
Four lanes are worth knowing:
Spreadsheets and shared drives
Excel is where almost every audit function lives at the start.
The risk universe sits in a sheet, workpapers in shared folders, findings in Word, and the CAE's mental map fills in the gaps.
The setup holds together as long as one person can carry the whole picture in their head.
Once you have two auditors running engagements in parallel, or the audit committee starts asking for live status, the cracks show up fast:
Version control disasters, missed follow-ups, lost evidence, and conflicting status updates: the kind of mess nobody wants to explain to the external auditors next quarter.
Dedicated audit and GRC platforms
This is the enterprise tier.
Optro (the AuditBoard rebrand from earlier this year), Workiva, IBM OpenPages, and MetricStream sit here.
They were purpose-built for audit and assurance work, which shows up in the depth of what they do well: structured workpaper review, three-way linking between risks, controls, and audits, board-pack generation, and regulator-ready evidence trails.
The catch is the catch you'd expect at this tier.
Annual contracts at this enterprise tier are typically in the high five to six-figure range based on user counts and modules, implementation cycles often run multiple quarters, complex rollouts need a consulting partner to land properly, and the change management work to get auditors using the platform consistently is its own project.
Compliance automation platforms
Vanta, Drata, Sprinto, Scytale, and Secureframe live in the compliance automation category.
Their job is continuous monitoring of a defined set of controls against a certification framework like SOC 2 or ISO 27001, with automation pulling evidence from cloud accounts, identity providers, code repos, and ticketing systems.
Connected work OS platforms
This category sits in between the spreadsheet floor and the enterprise ceiling.
A no-code work platform like SmartSuite, Asana, and Monday can get configured into an audit workspace that handles the audit universe, annual plan, fieldwork, findings, and follow-up, while sitting alongside the rest of the business's risk, compliance, vendor management, and operational work in the same system.
The fit is strongest for mid-market audit functions and regulated companies that have outgrown spreadsheets but aren't ready (or willing) to commit to a 12-month enterprise audit platform implementation.
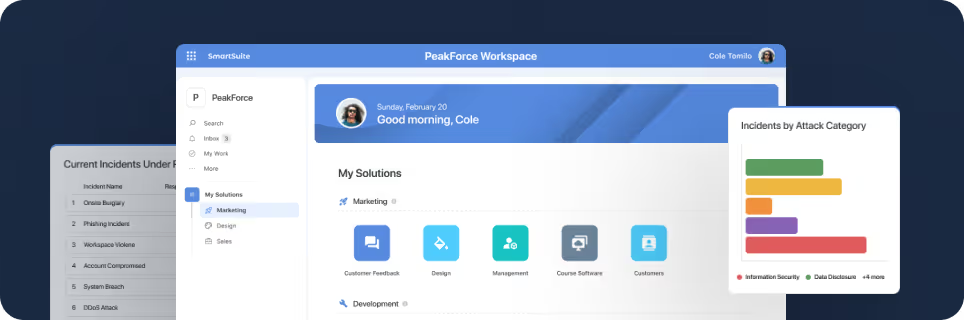
One platform worth a closer look in this lane is SmartSuite.
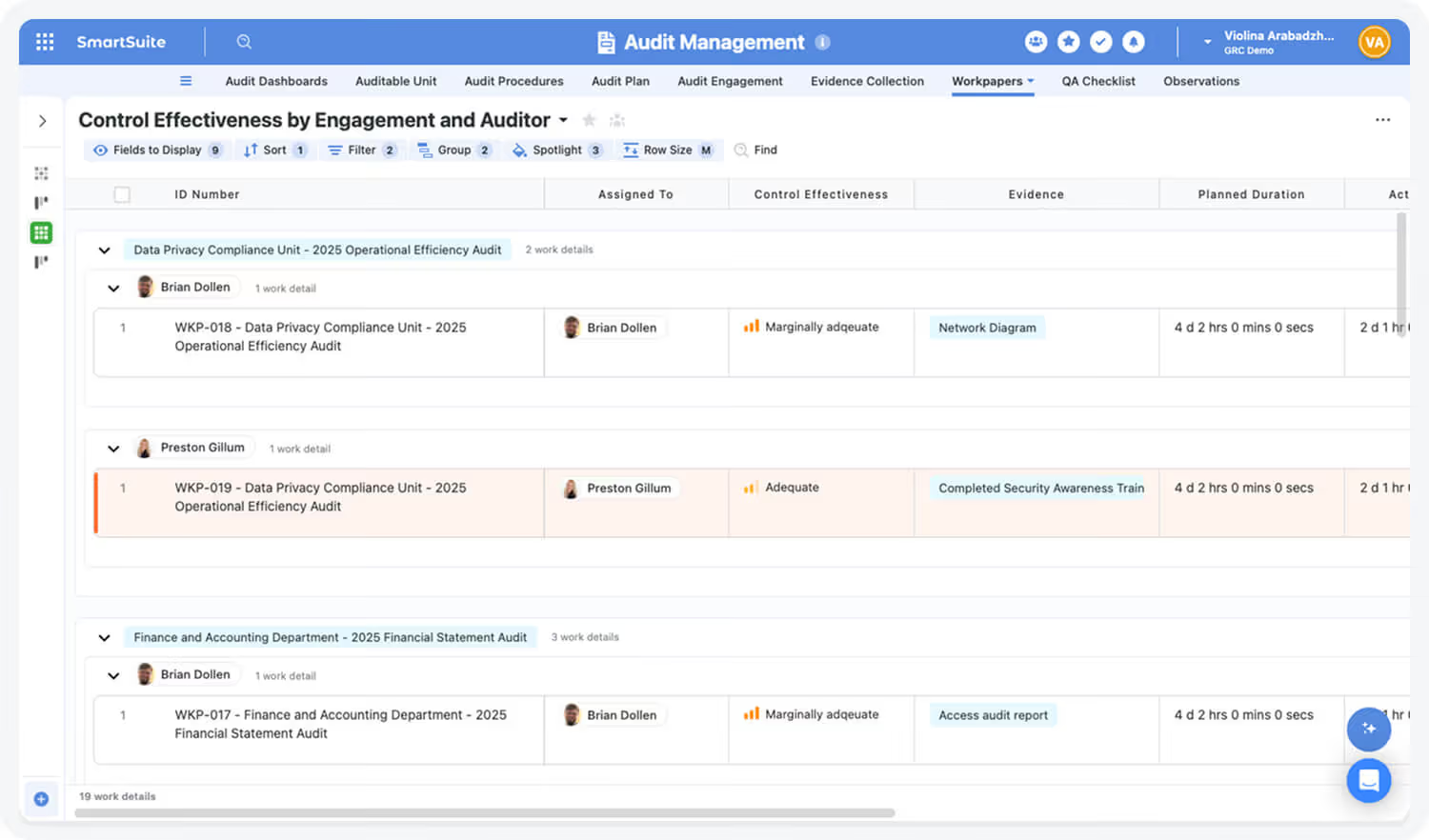
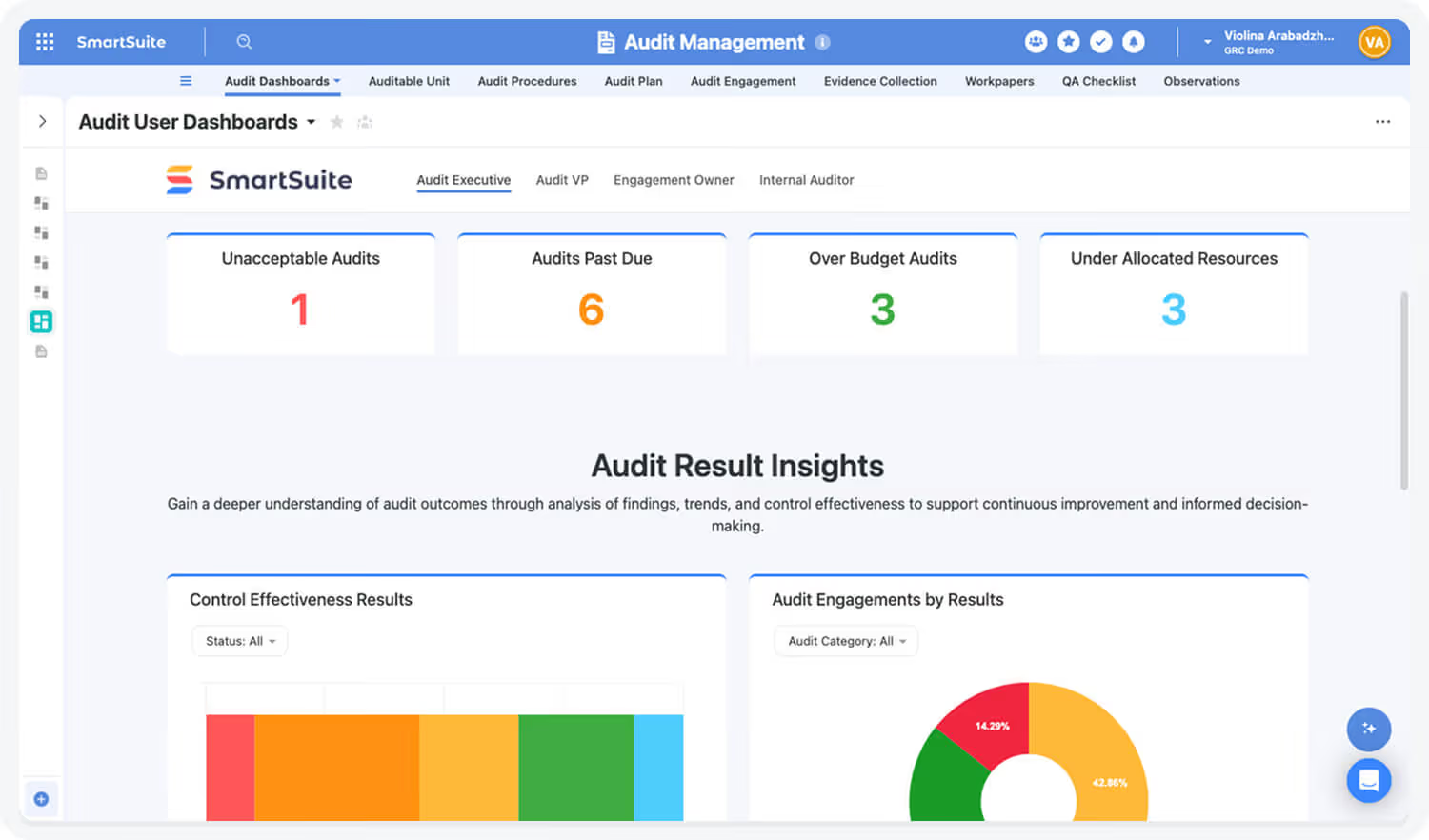
It's an AI-native work platform that audit teams can configure into a complete audit workspace: the audit universe, annual plan, engagement fieldwork, workpapers, findings, and remediation tracking, all linked to the risks and controls each engagement covers.
Evidence, review notes, sign-offs, and approvals sit in the same workspace, kept audit-ready for external auditors or regulators when they ask for them.

What makes the platform genuinely useful for audit work isn't any single feature.
It's that engagements, risks, findings, controls, and management owners all stay connected in the same data model, and the audit committee can pull a live view from that model whenever they need one.
Permissions keep audit's working files independent from the teams being reviewed, even when the underlying data (risks, controls, findings, and remediation tasks) is shared across the workspace.
The workflows that usually eat up audit team capacity (review reminders, overdue finding escalations, recurring control tests, audit committee follow-ups) run on no-code automation in the background.
The same automation layer supports continuous auditing for functions ready to move past annual-only cycles, pulling control test results, exception data, KRI movements, and access review breaks into the audit dashboard as they happen.
SmartSuite AI handles the tedious lifts on top of that: summarizing fieldwork interviews, drafting initial finding language, surfacing themes across evidence collections, and tightening executive summaries before review, with auditors keeping the final call on every conclusion.
The platform fits best for mid-market companies and regulated organizations in banking, healthcare, fintech, and insurance where audit can't afford to be cut off from the risk, compliance, ITSM, and operational work happening around it.
Rollout works in stages instead of as a big-bang implementation: audit teams typically begin with a single capability (annual planning, fieldwork execution, issue tracking, or evidence management), prove value, then expand into the full audit suite as the function matures.
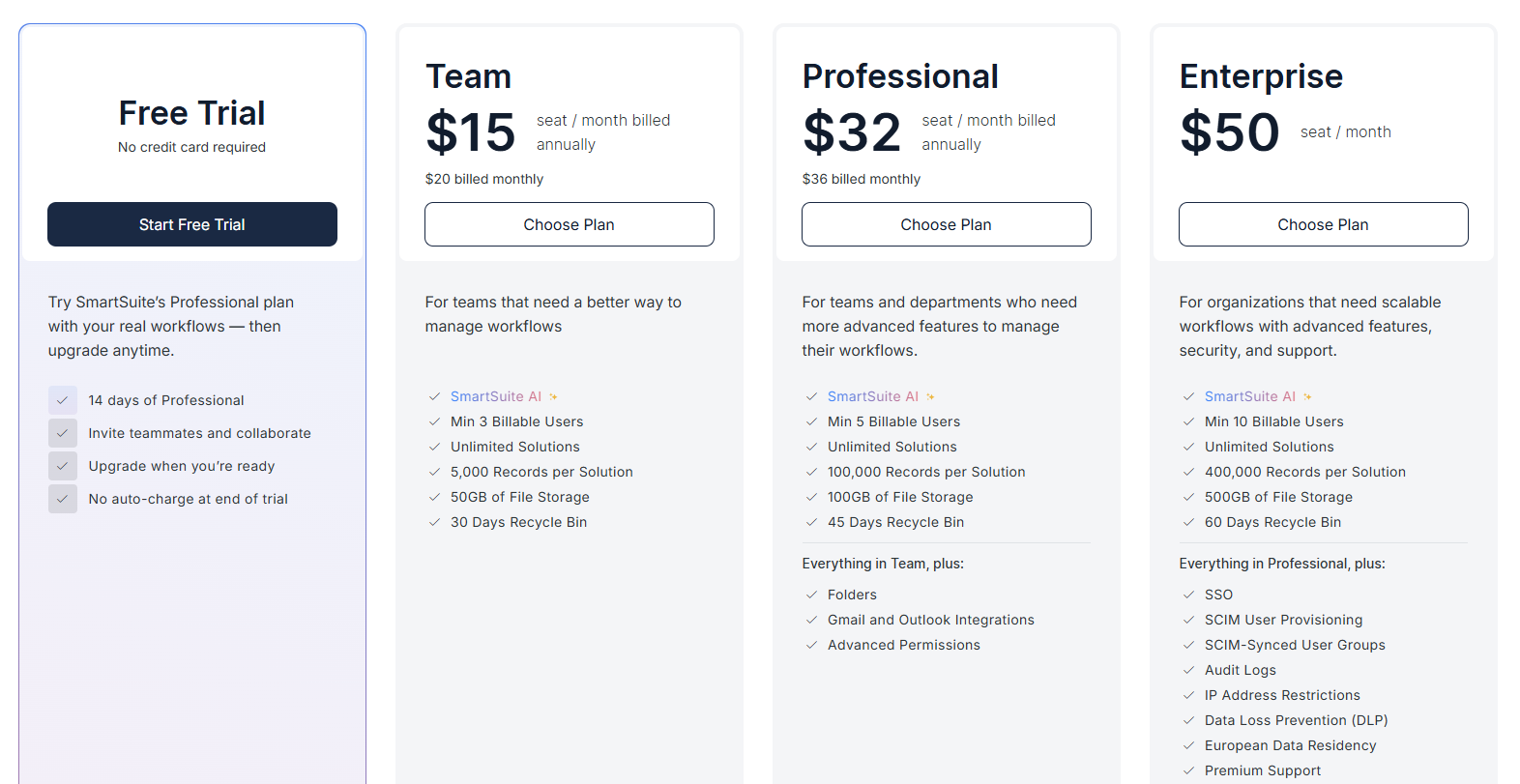
SmartSuite’s pricing starts at $15/user/month, with solution-based pricing available for larger regulated organizations that need access carved out by department, region, regulatory scope, or business unit.
Choose the platform that matches where your audit function is today
The right tool depends almost entirely on where your audit function actually sits right now.
- A two-person team running a handful of engagements a year doesn't need a six-figure enterprise audit contract.
- A 30-person assurance function inside a global bank can't run on Excel and shared drives.
The problem growing audit teams tend to hit is the gap between those two extremes.
Compliance automation tools cover certification work cleanly but stop well short of being a comprehensive audit platform.
Dedicated audit and GRC platforms handle everything an audit function needs, but ask for a budget and an implementation cycle that's hard to justify until the function is operating at real scale.
That middle gap is where SmartSuite sits in.
A connected work management solution configured into an audit workspace gives you the structure of a dedicated audit tool (audit universe, annual plan, engagements, findings, remediation) without the deployment timeline or the price tag.
And because audit ends up living in the same workspace as risk, compliance, ITSM, and the operational work being reviewed, the assurance picture stops being something the audit team has to manually reassemble before every committee meeting.
➡️ Start a free SmartSuite trial or book a demo to see how your team can manage governance, risk, and compliance in one place.
⚠️ Disclaimer: This article is for general information and isn't legal advice. Regulatory dates, scope, and enforcement details change. Confirm with qualified counsel before making compliance decisions.
Read more
- Financial Risk Management: Definitions & Best Practices
- What is GRC (Governance, Risk, and Compliance)?
- How To Choose a GRC Tool: Factors To Evaluate & Vendors
- GRC Audit: What Is It & How To Conduct One?
- Risk Management: What Is It & Why It's Important?
- How To Choose a Risk Management Platform?
- Third-Party Risk Management: What Is It & How It Works?
- Compliance Risk: What Is It & Why You Should Care?
- Vendor Compliance: What Is It & Why You Should Care?
- AI Risk Management: Definitions & Frameworks
SmartSuite provides work platform for standardizing workflows in the following areas:
- Governance, Risk & Compliance
- IT & Service Ops
- Project / Portfolio Management
- Business Operations















