Every business decision you make carries some degree of risk, and in 2026, the organizations that pull ahead are the ones that treat risk management as a working capability instead of a compliance afterthought.
In this guide, I’ll go over what risk management is, why it’s important, and how you can conduct a risk management assessment for your organization.
TL;DR
- Risk management is a discipline, not a checklist: it's the ongoing work of spotting, analyzing, responding to, and monitoring threats that could derail business objectives.
- There are many types of risk companies face today, including strategic, operational, financial, compliance, cyber, reputational, third-party, and AI-related risks, and each one calls for its own approach.
- The right response depends on two variables: how much control you have over the risk, and how much impact you can afford to absorb. Those two variables determine whether you avoid, reduce, transfer, share, or accept.
- Frameworks like ISO 31000, COSO ERM, and NIST CSF give teams a shared language, but almost nobody runs on a single framework; mature programs blend two or three.
- The right platform matters because spreadsheets and disconnected tools create blind spots. Connected GRC platforms like SmartSuite can help you bring risk, controls, audits, and incidents into one governed workspace.
What is risk management?
Risk management is the ongoing work of spotting potential threats to your business, weighing their likelihood and impact, deciding what to do about each one, and monitoring whether your response is actually working.
That sounds simple on paper. However, in practice, it can be messy.
Risks can hide in many places:
- A contract clause nobody re-read.
- A vendor's security posture that quietly deteriorated.
- A new regulation that shifts your obligations overnight.
- A piece of legacy software that one employee barely keeps alive.
For example, this article itself is somewhat of a risk for SmartSuite.
If I say something that is objectively wrong or bad about our competitors, there can be consequences, including lost business and legal troubles.
A risk program exists to surface those things early, keep them visible to the people who can act, and tie each one to a control with a clear owner.
What are the different types of risk?
Every business deals with risk, but not every business deals with the same risks in the same way.
- Strategic risk shows up when market shifts, a competitor's move, or a big internal decision changes your ability to hit long-term goals. Think about regional banks caught off guard by the 2023 deposit flight, or consumer goods brands blindsided by the 2025 tariff swings.
- Operational risk covers the day-to-day stuff: process breakdowns, human error, equipment failures, and supply chain hiccups. It's the kind of risk that rarely makes headlines on its own but quietly eats margin.
- Financial risk includes credit risk, liquidity risk, currency exposure, and anything else that puts the balance sheet under pressure.
- Compliance risk is about the consequences of not keeping up with regulations. GDPR, HIPAA, SOX, DORA, the SEC cybersecurity disclosure rules, the EU AI Act: the list grew longer in the last two years, not shorter.
- Cyber risk covers data breaches, ransomware, phishing, and everything that travels over a network. This category keeps expanding because the attack surface keeps expanding.
- Reputational risk is the downstream effect when something goes wrong publicly. Think about a viral social media post that puts your company in a bad spot.
- Third-party risk comes from vendors, suppliers, contractors, and partners whose problems become your problems, such as when your payroll provider goes down or your SaaS vendor has a breach.
- AI risk is the newest category that most risk teams are scrambling to build programs around. Model drift, training data integrity, bias, hallucinations, and shadow AI usage inside the company are all things regulators and auditors now ask about.
Why is risk management important?
The short answer: because the cost of being surprised is almost always higher than the cost of preparing.
The longer answer is that risk management does a few things at once:
- It shields the business from losses that can be forecasted.
- It gives leadership a structured way to weigh opportunities against their downsides.
- And it builds confidence across stakeholders, from investors and regulators to customers and employees, that the organization actually knows where its weak points are.
According to PwC's Global Risk Survey, organizations that take risk management seriously are meaningfully more likely to deliver on stakeholder expectations and hit revenue growth targets.
That tracks with what most GRC professionals have been saying for years.
➡️ Companies that know where they're exposed can move faster, not slower, because they've already decided in advance what they'll tolerate and what they won't.
What are the benefits of risk management?
A working risk program pays off in ways that are hard to measure individually but obvious in aggregate:
- You avoid losses you never had to eat.
- You catch compliance gaps before an auditor does.
- You make decisions with cleaner data because risk context sits alongside every proposal.
Some benefits worth calling out:
- Cleaner decision-making: leadership gets to weigh options against a real view of risk appetite, not a gut feel.
- Fewer surprises: incidents still happen, but they stop being mystery events; the team has a playbook.
- Board and regulator readiness: when someone asks "what are our top risks and what are we doing about them?," you can answer in 10 minutes instead of 10 days.
- More affordable insurance: insurers, banks, and investors can look at how mature your risk program is before they price you.
- Stronger compliance posture: when risks and controls are mapped together, audits stop being fire drills.
- Room to innovate: this one surprises people. Good risk management doesn't kill growth; it clears a path for it.
Banks that mapped their DORA exposure early in 2024 entered the January 2025 deadline with compliance already in place, while competitors scrambled.
That head start turned into a sales advantage when enterprise customers asked hard security questions.
How can you respond to risks?
Once you know a risk exists, you've got choices.
Most frameworks list five: avoid, reduce, transfer, share, and accept.
That list is accurate, but it doesn't tell you which choice to make for a given risk. For that, two variables do most of the work.
Variable 1: How much control do you actually have over this risk?
Some risks you can genuinely influence through your own actions.
Patching a vulnerability, training employees on phishing, hardening a process, or fixing a broken approval workflow. High control.
Other risks you can't do much about on your own.
Currency swings, geopolitical events, a regulator's enforcement priorities, or macroeconomic shifts. Low control.
Variable 2: How much of the impact can you afford to absorb?
If the risk lands and the worst case plays out, does it cost you a bad quarter, or does it cost you the company?
Some impacts are survivable. Others aren't.
Together, those two variables shape the decision:
High control and high-impact exposure: mitigate hard
This is where most risk work actually lives.
You can influence the probability, and the stakes are too high to ignore.
Training, MFA, backups, penetration tests, segmented networks, and updated SOPs all fit here.
Low control and high-impact exposure: transfer, share, or avoid
You can't reduce the probability much through your own actions, but if it lands, you're in serious trouble.
Cyber insurance, indemnification clauses, syndicated partnerships, or walking away from the activity entirely.
- A bank declining to enter a sanctioned jurisdiction is avoiding.
- A company buying catastrophic breach coverage is transferring.
- Two companies jointly launching a product and splitting liability are sharing.
High control and low-impact exposure: accept with light monitoring
You could put controls in place, but the juice isn't worth the squeeze.
Document the exposure, assign an owner, monitor it, and move on to bigger problems.
Low control and low-impact exposure: accept and revisit
Nothing to do except log it and check that it hasn't moved into another quadrant.
Most risk registers have a long tail of these.
The reason this framing matters: most teams default to "mitigate" for everything because mitigation feels responsible.
But mitigating a low-impact risk you have little control over is wasted effort.
Accepting a high-impact risk you have lots of control over is negligence.
Real risk registers use all five responses because real programs sort risks into the right quadrant first, then pick the response that fits.
How to conduct a risk management assessment
A risk management assessment is the structured process of figuring out where you're exposed, how badly, and what to do about it.
Most educational content breaks this into five linear steps.
In practice, it works better as three overlapping phases that cycle continuously, because real risk work doesn't wait for you to finish "step 2" before a new threat shows up.
Phase 1: Scope and discover
This is where you define what you're assessing and hunt for what could go wrong inside that scope.
Scope matters more than most teams give it credit for.
- An assessment of "the whole company" turns into a shallow survey of nothing.
- An assessment of "our third-party AI tooling" gets you somewhere useful.
Discovery happens through interviews with department heads, questionnaires to process owners, reviews of recent incident reports, and external signals like regulator bulletins, threat intel feeds, peer industry reports, and analyst commentary.
Everything lands in a risk register, which becomes your single source of truth for the next two phases.
Phase 2: Assess and decide
For every risk you surface, you're answering two questions: how likely is it, and what happens if it lands?
A risk matrix helps you put those two variables into conversation.
Plot likelihood against impact on a 5 by 5 grid, and the risks cluster into a priority order.
- Quantitative methods work for risks you can put a dollar figure on, like cyber loss scenarios or supplier concentration.
- Qualitative methods (high, medium, low with narrative context) work better for reputational and strategic risks where numbers would be guesswork.
Once a risk is prioritized, you pick the right response based on how much control you have and how much impact you can absorb.
Each risk gets an owner, a plan, a due date, and one or more controls tied to it.
Phase 3: Operate and monitor
This is the phase that separates a real program from a binder exercise.
Threats evolve, business priorities shift, controls decay, and new regulations appear.
💡 Your risk register needs to be a living document, with scheduled reviews, automated alerts on changing conditions, and a clear reporting cadence to leadership and the board.
Annual assessments are table stakes.
Mature programs run continuous monitoring on top, pulling control effectiveness data, incident trends, KRI (key risk indicator) movements, and near-miss reports into dashboards that update in near real time.
The phases overlap:
- New risks identified in Phase 3 feed back into Phase 1.
- Treatment decisions made in Phase 2 get adjusted when monitoring in Phase 3 shows a control isn't working the way anyone expected.
What are the different risk management frameworks?
Here's what nobody tells you in the vendor pitch: almost no mature program runs on a single framework.
The teams doing this well blend two or three.
- ISO 31000 sets the enterprise-level principles.
- NIST CSF handles cyber.
- COSO ERM ties risk to strategy and performance (especially in public companies).
- FAIR quantifies cyber exposure when the board wants dollar figures.
Pick your combination based on your industry, your regulators, your board's expectations, and how your team actually works.
With that framing out of the way, here's what each framework gives you:
- ISO 31000 is the international standard from the International Organization for Standardization.
It gives you principles plus a process model you can adapt to almost any organization. It’s a good starting point if you're building from zero.
- COSO Enterprise Risk Management (ERM) Framework was developed by the Committee of Sponsoring Organizations of the Treadway Commission.
It's more opinionated than ISO 31000 and deeply tied to strategy and performance.
If your board or audit committee is already COSO-aligned (many are, especially in public companies), this is the natural choice.
- NIST Cybersecurity Framework (CSF) comes from the US National Institute of Standards and Technology.
CSF gets used well beyond federal contractors. CSF 2.0, which added the "Govern" function, is now widely adopted across industries that weren't traditionally NIST-aligned.
- GRC Capability Model (OCEG Red Book) from the Open Compliance and Ethics Group is less a framework and more an integration blueprint.
It's designed for organizations that want governance, risk, and compliance working as one system instead of three separate functions.
- FAIR (Factor Analysis of Information Risk) is the one to know if you're quantifying cyber risk.
It lets you put probability distributions and dollar figures on cyber loss scenarios, which matters more every year as boards push for cyber exposure to be reported in financial terms.
The goal here isn't framework purity. It's a risk program that fits your business, picks the right tool for each layer, and doesn't force your team to relearn methodology every time a new regulation lands.
What are the kinds of tools you can use for risk management?
Tools for risk management fall into a few broad buckets, and which one you need depends on your program's maturity and scope.
- Spreadsheets: Most programs start here.
A risk register in Excel or Google Sheets works fine when the program is small and a single person can keep it current.
However, it breaks the moment you need cross-team visibility, audit trails, or real-time updates.
- Dedicated GRC platforms: Tools like Archer, MetricStream, IBM OpenPages, Onspring, and Diligent were built specifically for GRC work at enterprise scale.
They give you deep risk modeling, control testing workflows, audit management, and board-grade reporting.
The trade-off is cost and complexity; most require implementation partners and long onboarding cycles.
- Compliance automation platforms: Tools like Vanta, Drata, Sprinto, Scytale, and Secureframe focus on automating evidence collection for certifications like SOC 2 and ISO 27001.
They're great at what they do, but compliance automation and risk management aren't the same discipline.
You still need something to manage risks that don't fit neatly into a certification scope.
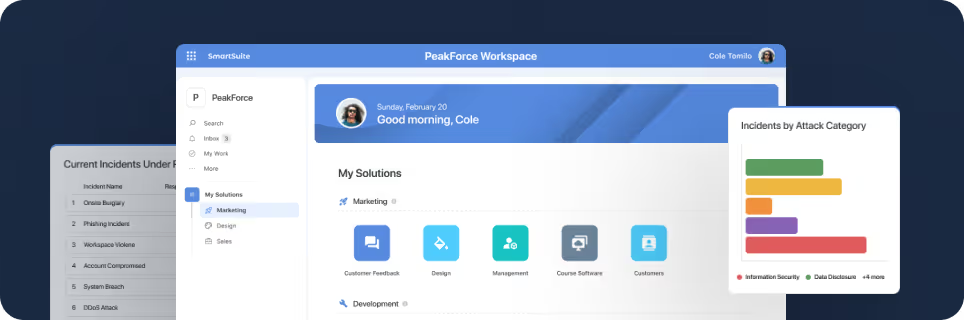
- Connected Work OS platforms: A newer category where GRC workflows live alongside the rest of operations in one flexible, no-code system, with solutions like SmartSuite.
This approach works well for mid-market companies and growing enterprises that want risk, compliance, audits, and incidents connected to real business work instead of being siloed off in a speciality tool.
➡️ If your risk program is outgrowing spreadsheets but you're not ready to commit to a six-figure enterprise GRC implementation, SmartSuite is worth a look.
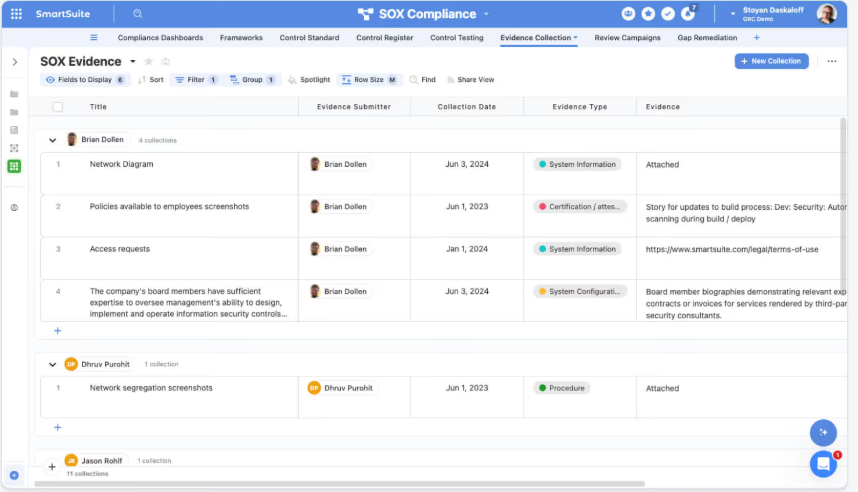
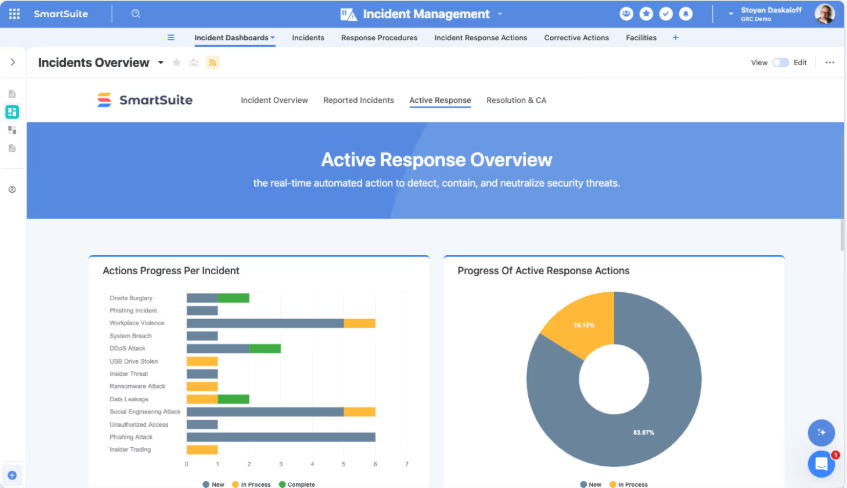
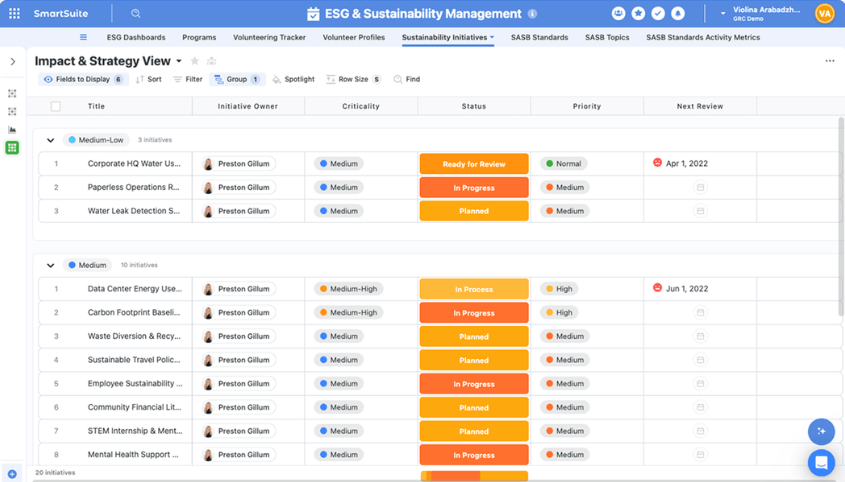
It's an AI-native Work OS that lets teams manage risk registers, controls, audits, incidents, third-party risk, AI governance, and remediation workflows in one connected workspace.
Because it's flexible by design, you can model your risk program around your business instead of bending your business to fit someone else's template.
Built-in automation handles recurring work like control testing reminders, escalation of high-rated risks, and vendor review cycles, while live dashboards give leadership a real-time view of exposure and remediation progress.
SmartSuite AI helps with the tedious parts, like summarizing vendor questionnaires, drafting policy updates, and flagging gaps in incident reports, without ever letting AI make governance decisions on its own.
It fits well for mid-market companies, regulated industries like banking and healthcare, and GRC teams that want compliance connected to the rest of their operations rather than isolated in a certification tool.
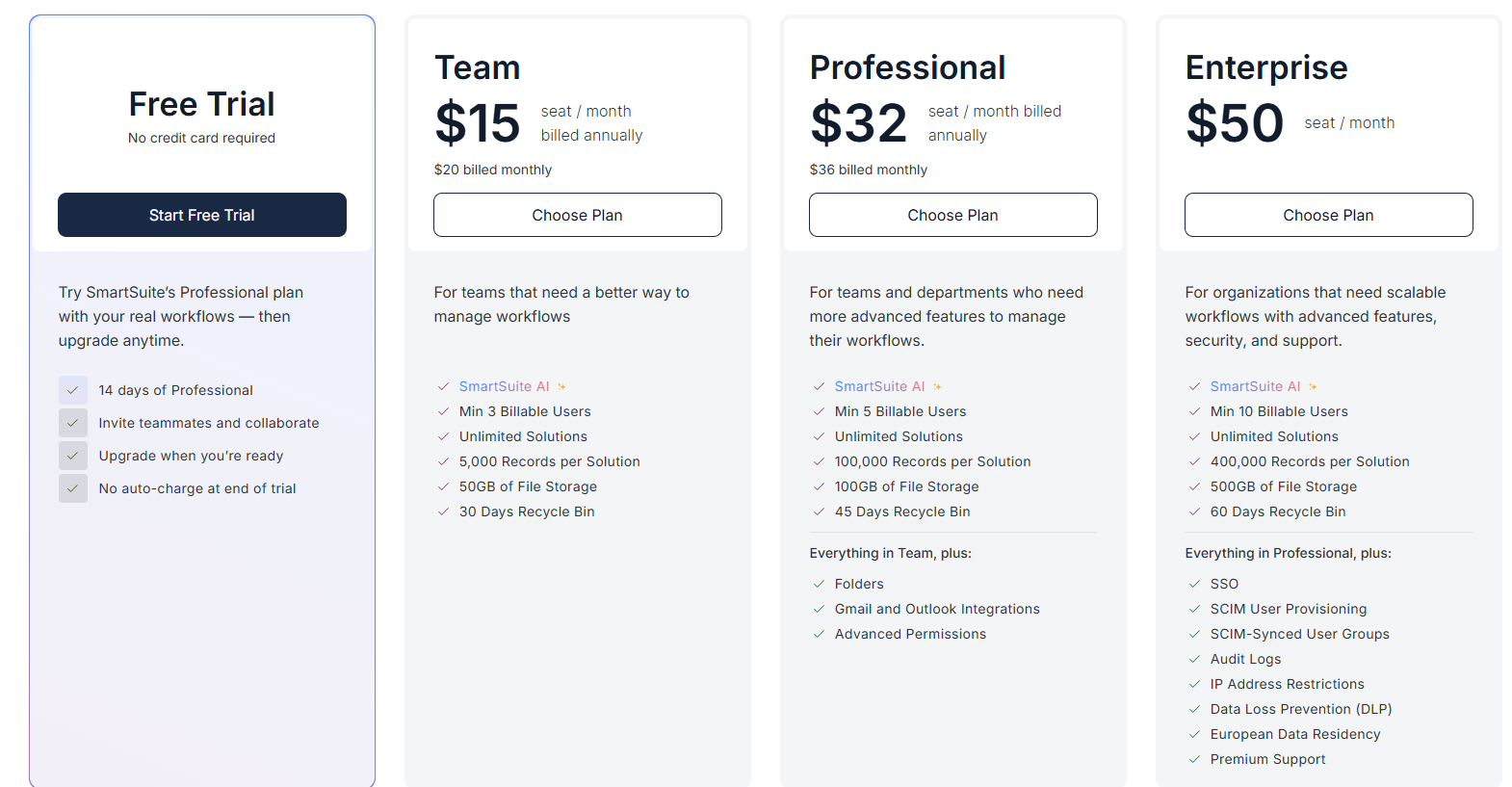
Pricing starts at $15/user/month for the Team plan, with solution-based pricing available for regulated enterprises that need to structure access by department or regulatory scope.
Run your risk program on a platform built for it
The tools above each solve a slice of the risk management problem.
- Dedicated GRC platforms like Archer and IBM OpenPages are built for large enterprises with deep risk modeling needs and the budgets to match them.
- Compliance automation tools like Vanta and Drata do a great job on certification work but weren't designed to be full risk platforms.
- Spreadsheets are fine for small programs and painful for scaling ones.
For mid-market companies and growing teams, the sweet spot is a platform that handles risk, controls, audits, incidents, and third-party management in one place, connects naturally to the rest of the business, and doesn't need a six-month implementation to turn on.
That's the gap SmartSuite fills.
Instead of forcing you to choose between flexibility and governance, it gives you both: a no-code environment where your risk team can model the program however it needs, backed by enterprise-grade permissions, audit logs, and AI governance.
Risk, controls, audits, incidents, vendors, and remediation work all sit in one governed workspace, with dashboards that update as the work changes.
➡️ Start a free SmartSuite trial or book a demo to see how your team can manage governance, risk, and compliance in one place.
SmartSuite provides work platform for standardizing workflows in the following areas:
- Governance, Risk & Compliance
- IT & Service Ops
- Project / Portfolio Management
- Business Operations















