Vendor compliance has quietly become one of the highest-stakes parts of running a regulated business in 2026.
This is because regulators no longer care whether the failure happened inside your walls or three suppliers down the chain.
In this guide, I'll walk through what vendor compliance actually means, the types you'll run into, the frameworks worth knowing, and how to run a vendor compliance assessment from sourcing through offboarding.
TL;DR
- Vendor compliance is a discipline, not a checkbox: it's the ongoing work of confirming that the third parties you rely on meet your regulatory, security, contractual, and operational obligations across the full relationship.
- The categories matter more than people think: regulatory, security, contractual, industry-specific, ESG, and operational compliance each carry different evidence requirements and different consequences when they slip.
- Regulators hold you accountable for your vendors' failures: DORA, the federal banking regulators' interagency guidance on third-party risk, HIPAA's Business Associate rules, and the EU AI Act have all reinforced that point in recent years.
- A working program covers the full vendor lifecycle: pre-onboarding due diligence, contracted onboarding with the right legal hooks, ongoing monitoring, and a clean offboarding path that proves data and access were actually closed out.
- Tools matter because spreadsheets break at scale: connected platforms that link vendors, contracts, controls, and incidents in one place (like SmartSuite) outperform the old setup of a TPRM tool plus a contract repository plus a GRC system that don't talk to each other.
What is vendor compliance?
Vendor compliance comes down to one thing: proving that the third parties handling part of your business are actually running it the way your regulators, your contracts, your security team, and your own policies say they should.
In practice, this is where procurement, legal, security, and compliance all run into each other, asking the same question from different angles:
Can we trust this vendor with the part of our business we've handed them, and can we evidence it when a regulator comes knocking?
What "compliant" looks like also keeps moving.
A vendor that was clean two years ago might have lost their SOC 2 attestation, missed a renewal, gotten acquired, or suffered a breach.
Vendor compliance is what catches those changes before they become your problem.
The shape of the work depends on the industry:
- A hospital is verifying that its EHR vendor still encrypts patient data at rest and that the BAA hasn't lapsed.
- For a community bank, it's evidencing that its oversight of the core processor still satisfies the bank's obligations under the interagency third-party risk guidance, with documented committee review.
- EU asset managers have to produce DORA-aligned ICT third-party registers with exit plans baked into every critical contract.
- In fintech, the same vendor gets mapped against PCI DSS, GDPR, and a growing pile of US state privacy laws all at once.
Underneath the variation, the job stays consistent. Vendors do the work, but you're the one explaining it to a regulator.
What are the different types of vendor compliance?
Vendor compliance fragments into categories, and most organizations end up caring about more than one at the same time.
- Regulatory compliance: GDPR, HIPAA, SOX, DORA, the SEC cybersecurity disclosure rules, and the EU AI Act all flow downhill into your vendor relationships.
If a vendor handles regulated data on your behalf, your regulators will treat their failures as yours.
- Security compliance: SOC 2 Type II reports, ISO 27001 certifications, ISO 27701 for privacy, and CSA STAR for cloud-specific assurance are the artifacts that get collected, reviewed, and renewed every year.
- Contractual compliance: SLAs, MSAs, DPAs, source code escrow clauses, audit rights, breach notification windows.
Most teams have the loosest grip here because the contract gets signed, and nobody reads it again until something goes wrong.
- Industry-specific compliance: HITRUST and PCI DSS in healthcare and payments. FFIEC and OCC interagency guidance in banking. NIS2 for European critical infrastructure. NERC CIP for energy.
Each carries vendor-facing obligations that don't show up in the generic frameworks.
- ESG and supply chain compliance: The German Supply Chain Due Diligence Act, the EU Corporate Sustainability Due Diligence Directive, the UK and Australian Modern Slavery Acts, and California's SB 657 all push compliance obligations onto vendor relationships in ways that have grown sharper over the last five years.
Although the EU's recent Omnibus I package and Germany's draft LkSG amendments have softened reporting and liability under CSDDD and LkSG, the underlying due diligence obligations remain, and equivalent regimes (UK Modern Slavery Act, California's SB 657, Australia's Modern Slavery Act) still apply.
- AI governance: With the EU AI Act, companies are now asking vendors for "AI transparency reports" and "Model Cards" to ensure the third-party software they use isn't introducing bias or "black box" risks into their operations.
Why is vendor compliance important?
Vendor compliance is important because the cost of a vendor failure almost always lands on you.
The 2013 Target breach is the canonical example, where stolen credentials from a small HVAC vendor named Fazio Mechanical eventually cost Target around $420 million (projection) in settlements, technology upgrades, and legal expenses.
The MOVEit file transfer exploit ultimately impacted more than 2,700 organizations and roughly 93 million people.
The pattern hasn't softened in 2026. If anything, regulators are getting less patient with the "our vendor did it" defense.
DORA, which became enforceable on January 17, 2025, holds EU financial entities directly accountable for managing the operational resilience risks tied to their critical ICT vendors.
The June 2023 interagency guidance from the FDIC, Federal Reserve, and OCC tells banks plainly that outsourcing the activity doesn't outsource the responsibility.
HIPAA has worked that way for decades, with enforcement intensifying in recent years.
Regulators want to know who your vendors are, what they're doing for you, what could go wrong, and what you're doing about it.
What are the benefits of vendor compliance?
Fewer bad surprises is the easy answer to the benefits of vendor compliance.
A working program does more than that, though. Here are a few more benefits worth calling out:
- Faster procurement decisions: when the security review, legal review, financial review, and business owner approval all run on the same vendor record, deals close in days instead of weeks.
- Cleaner audits: SOC 2 and ISO 27001 audits both ask hard questions about vendor management; having the answers documented and current saves real money on audit cycles.
- Lower cyber insurance premiums: insurers increasingly look at TPRM maturity as a pricing input, especially after the wave of vendor-driven breach claims in 2023 and 2024.
- Stronger negotiation leverage: when you can see SLA misses across your vendor portfolio, you walk into renewal conversations with data, not vibes.
- Real audit-ready exit plans: regulated industries are now expected to have working alternatives identified for critical vendors, not just paper plans.
In the GRC community, the pattern is consistent.
Organizations treating third-party risk as a continuous program tend to absorb fewer material incidents, and when something does go wrong, it costs less and gets resolved faster than at peers running point-in-time reviews.
Vendor risk is one of those areas where the cheapest dollar you'll ever spend is the one you spent before signing.
➡️ Mature vendor compliance programs don't slow procurement down. They speed it up by giving every team a shared definition of what "good" looks like.
How can you approach vendor compliance?
The single biggest mistake I see is treating every vendor the same.
A risk-based approach starts by tiering vendors before you assess them, with the tier driving how deep you go on due diligence, what shape the contract takes, how often you re-review, and what the exit plan needs to look like.
There's a meaningful gap between a full security questionnaire and a quick lite review, and you don't want to spend either on the wrong vendor.
A simple tiering model that works for most organizations:
- Tier 1 (critical): the vendors a regulator would care about.
They process regulated data, sit inside a business-critical workflow, or are tied into your operations deeply enough that an outage on their side becomes an outage on yours. Core banking platforms, EHR vendors, payroll processors, and primary cloud providers all live here.
- Tier 2 (important): vendors with access to sensitive but non-regulated data, or whose disruption would be painful but survivable. Most SaaS tools sit here.
- Tier 3 (low risk): vendors with minimal data access, easily replaceable, and low operational impact.
Tier 1 gets the full treatment: detailed security questionnaire, SOC 2 review, financial health check, business continuity plan review, contractual audit rights, and quarterly check-ins.
Tier 3 might get a basic vendor profile and a contract on file.
Ownership matters as much as tiering. Vendor compliance fails when it's everyone's job and no one's responsibility.
Mature programs name a single owner who runs the program, with clear hand-offs to Legal for contracting, Security for technical assessments, and the business owner who actually uses the vendor.
Cadence comes third.
A point-in-time assessment at onboarding tells you the vendor was clean on the day you signed; continuous monitoring tells you whether they still are.
How to conduct a vendor compliance assessment
A vendor compliance assessment runs as a lifecycle, not a one-off event, and most teams trip up because they overinvest in one phase and underinvest in the others.
I think of it in four phases that follow the actual vendor relationship: pre-onboarding, onboarding, ongoing monitoring, and offboarding.
In practice, the phases overlap.
New vendors are being onboarded while existing ones are being monitored, and offboarding triggers feed back into pre-onboarding decisions about replacement vendors.
The phase model still gives you a clean way to think about what should be happening when.
Phase 1: Pre-onboarding
Pre-onboarding answers the first question: should this relationship exist at all? Intake kicks it off.
Someone in the business identifies a need, names a candidate vendor, and starts the request.
From there, you assign a tier based on the data the vendor will touch, the process they'll run, and the regulatory environment they pull you into.
Tier in hand, assessment depth follows.
Tier 1 vendors get a full security questionnaire (often a SIG variant), a SOC 2 Type II report review, financial health checks via Dun & Bradstreet or similar, sanctions screening, and a business continuity plan review.
Tier 3 vendors get a much shorter intake form.
Regulatory fit gets confirmed in the same phase.
- A vendor that will process protected health information needs a signed BAA before any data moves.
- A vendor outside the EU touching EU personal data needs the DPA written with the right SCCs and a transfer impact assessment.
- A vendor providing ICT services that support critical or important functions for an EU financial entity needs DORA-aligned exit clauses in the contract before signature.
- A vendor handling cardholder data needs PCI DSS scope confirmed and segmentation evidenced.
This phase closes on a single decision: approve, approve with conditions, or reject.
Phase 2: Onboarding
Once approved, the vendor moves into onboarding, where three things get set up at the same time: the contract, the operational connection, and the compliance baseline.
The contract carries most of the weight.
It needs the right SLAs (with real consequences), audit rights, breach notification windows that match regulatory expectations (72 hours under GDPR where the breach poses a risk to individuals), sub-processor disclosure obligations, data residency requirements, and a working exit clause.
For Tier 1 vendors in regulated industries, the regulatory minimums in those clauses aren't negotiable.
Operational onboarding runs alongside the contract: account provisioning, integration setup, security configuration review, and access permissions wired to the principle of least privilege.
The compliance baseline gets locked in at the same time.
- Which framework controls does this vendor map to?
- What evidence do you need from them annually?
- What are the renewal dates for their SOC 2 and insurance certificates?
- Who owns the relationship internally?
Done well, onboarding takes weeks. Done poorly, it takes months and leaves gaps that show up in your next audit.
Phase 3: Ongoing monitoring
Most vendor compliance programs collapse here. Vendors don't stand still.
Their security posture decays, they get acquired, they lose key staff, they expand into new geographies, and they sub-contract work to fourth parties you've never heard of.
None of that shows up in the onboarding artifacts you collected last year.
Ongoing monitoring covers several streams running in parallel: annual or semi-annual recertification (collecting renewed SOC 2 reports, insurance certificates, attestations), continuous security monitoring, SLA tracking against the contract, incident reporting (breaches, outages, sub-processor incidents, near-misses), and regulatory change monitoring that affects vendor obligations.
💡 An immature program re-collects the same vendor questionnaire every year and files it away.
A mature program reads it, compares it to last year's version, and acts on the deltas.
Contract obligation tracking lives in this phase as well: renewal windows, price escalators, auto-renewal clauses, and notice periods for termination.
Most contracts have a notice period in the 60 to 90 day range that, if missed, rolls you into another year automatically.
A working program flags those windows months before they close.
Phase 4: Offboarding
Nobody plans for offboarding, and almost everyone regrets skipping it.
When a vendor relationship ends (voluntarily, after a breach, or because of consolidation), the work doesn't stop with the contract terminating.
You need verified data deletion or return, access revocation across every integrated system, parallel instructions to sub-processors, and a documented closeout that an auditor can read two years later and understand what happened.
Regulated industries pick up extra obligations here.
DORA exit plans and the interagency guidance's expectations on termination both land in this phase, and banks that quietly drift away from a critical vendor without a documented exit plan are exactly what those rules were written to prevent.
Done right, offboarding leaves a clean record: the vendor's gone from active inventory, the data's gone from their systems, and both can be proved.
What are the kinds of tools you can use for vendor compliance?
Tooling for vendor compliance falls into a handful of categories, and the right fit depends on the size of your program, your regulatory environment, and how connected the vendor data needs to be with the rest of your business:
- Spreadsheets: where most programs start.
A vendor inventory in Excel, a folder of SOC 2 reports in SharePoint or Google Drive, a calendar of renewal dates.
It works when you have 10 vendors and one person tracking them. Somewhere between 50 and 100 vendors, the model collapses, and nobody can tell which version of the spreadsheet is current.
- Dedicated TPRM platforms: tools like ProcessUnity, OneTrust, and Mitratech are purpose-built for third-party risk.
They handle questionnaire workflows, evidence collection, risk scoring, and continuous monitoring.
Strong at what they do, with contract lifecycle management, sourcing events, and the broader compliance program often living in adjacent tools.
- Continuous monitoring services: BitSight, SecurityScorecard, UpGuard, and RiskRecon scan vendor external posture (open ports, leaked credentials, certificate hygiene) and surface scores.
- Enterprise GRC platforms: Archer, MetricStream, ServiceNow GRC, IBM OpenPages, Diligent, Riskonnect, and LogicGate.
They are built for enterprise-scale GRC and are increasingly capable of handling third-party risk as a module.
Powerful platforms, with the trade-off being cost and implementation timelines that can run into months.
- Compliance automation tools: Vanta, Drata, Sprinto, Secureframe, and Scytale focus on certification automation (SOC 2, ISO 27001).
Most have added vendor risk modules in recent years, with the depth varying by platform, and the certification side of the product still being where they're strongest.
- Connected work platforms: a newer category that brings vendor compliance, contract operations, and broader GRC into one customizable workspace. SmartSuite (that’s us) is here.
➡️ For mid-market and regulated organizations who want vendor compliance connected to procurement, contracts, and the rest of the GRC program, SmartSuite is worth a serious look.
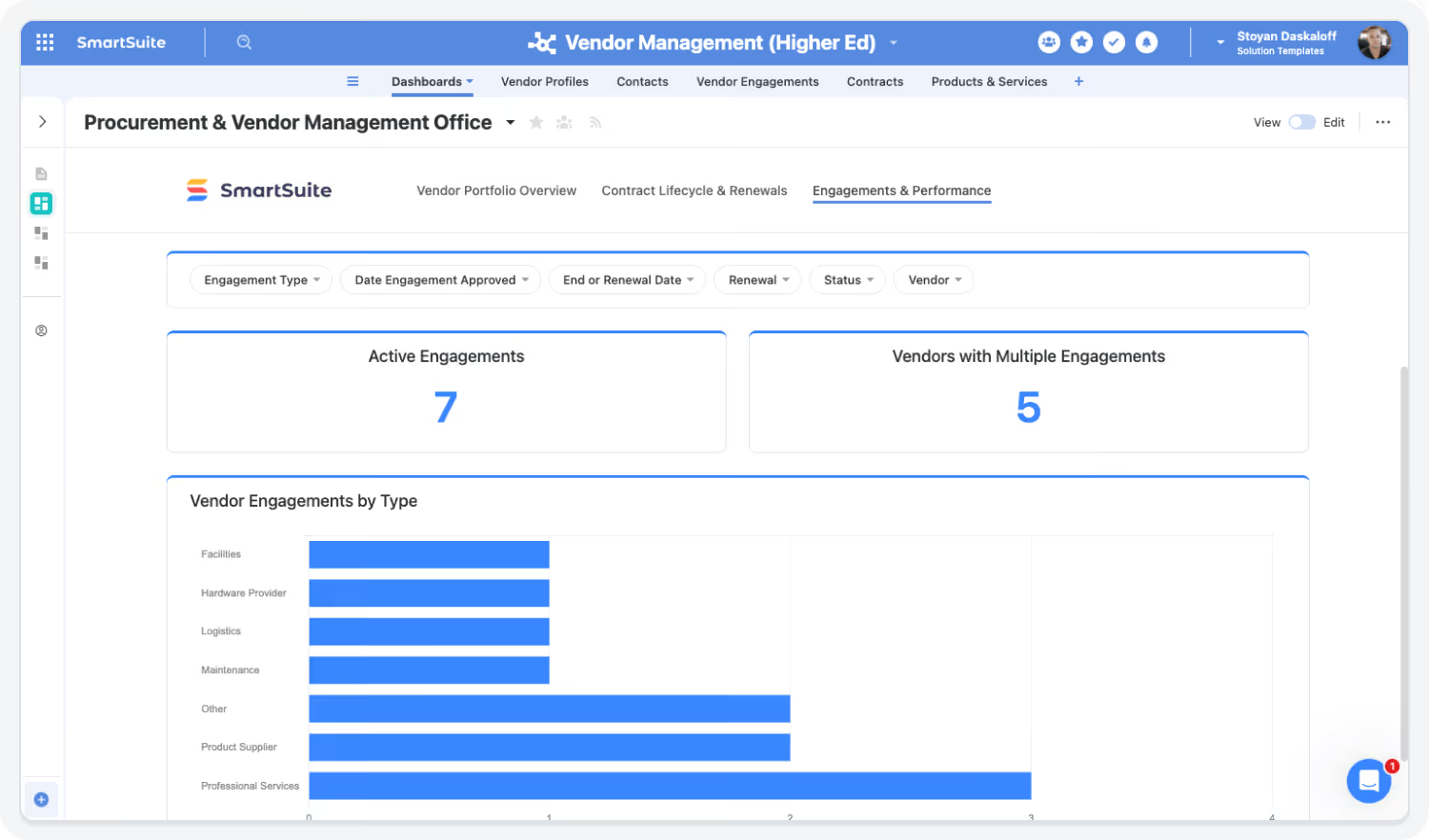
Our platform puts vendor onboarding, due diligence, contract lifecycles, obligation tracking, and continuous monitoring inside one no-code workspace, where every vendor record carries the contracts, SLAs, security assessments, and renewal dates attached to it directly.
SmartSuite AI handles the tedious parts of the program: summarizing vendor questionnaires, surfacing risk patterns inside responses, mapping findings to control frameworks, and flagging gaps in due diligence packets, with humans approving the actual governance decisions.
Because the platform is no-code, you shape the program around how your team actually works (procurement-led, security-led, or compliance-led) rather than fitting yourself to a vendor-defined template.

Live dashboards give Procurement, Legal, Security, and the business owners a shared view of vendor status, contract health, and obligations, which is the part that usually breaks down when vendor data is scattered across three different systems.

Regulated industries are where this lands hardest: banks managing OCC and DORA expectations, healthcare organizations tracking BAAs and HIPAA evidence, fintechs juggling PCI DSS and state-level data protection rules, and asset managers running DORA and SEC obligations side by side.

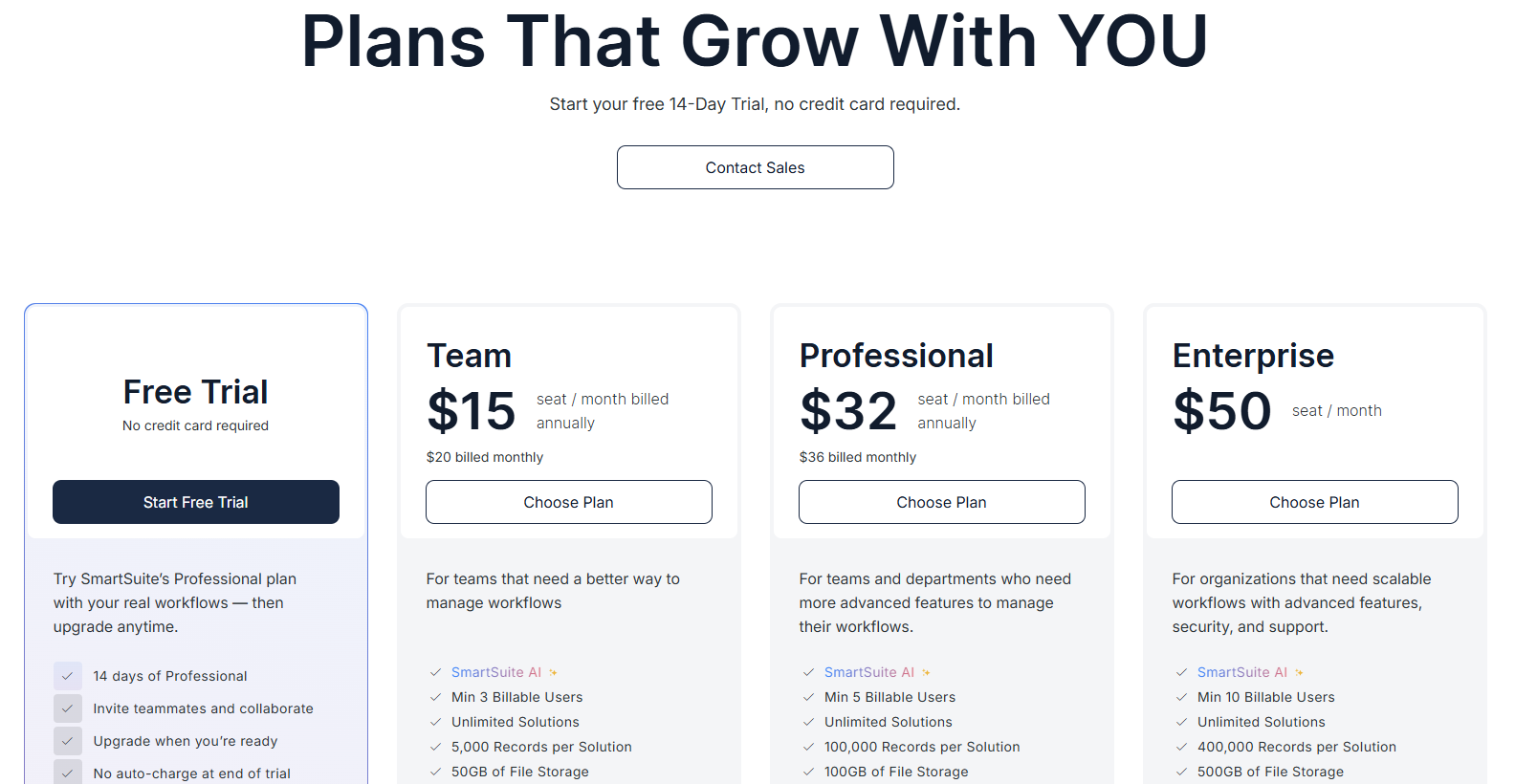
Pricing starts at $15/user/month for the Team plan, with solution-based pricing available for regulated enterprises that need to structure access by department, region, or regulatory scope.
Run your vendor compliance program on a platform built for it
Each tool category above solves a slice of the vendor compliance problem.
- Dedicated TPRM platforms like ProcessUnity and OneTrust go deep on questionnaires and risk scoring, while contract lifecycle and sourcing typically live elsewhere.
- External posture services like BitSight are strongest as a continuous signal feed alongside a program.
- Enterprise GRC platforms are powerful and built for the largest organizations, which is also why the implementations run into months.
- Compliance automation tools handle certification work cleanly, with vendor management modules being a more recent addition, where depth varies by platform.
For regulated mid-market and enterprise teams (banks, fintechs, healthcare organizations, asset managers), the gap is usually the same: vendor records, contracts, controls, evidence, and obligations all sit in different systems that don't talk to each other.
That's the gap SmartSuite fills.
Our platform pulls vendor onboarding, due diligence, contract lifecycles, obligation tracking, sourcing events, and the broader compliance program into one governed workspace.
Vendor records connect to contracts. Each contract carries its obligations. Obligations map to controls. Controls roll up into frameworks.
The whole chain stays visible to Procurement, Legal, Security, and Compliance at the same time, on dashboards that update as the work changes.
For regulated industries facing DORA, the interagency third-party risk guidance, HIPAA, PCI DSS, and the rest of the alphabet, that connected view is the difference between a program you can defend in front of a regulator and a binder of disconnected artifacts.
➡️ Start a free SmartSuite trial or book a demo to see how your team can manage governance, risk, and compliance in one place.
⚠️ Disclaimer: This article is for general information and isn't legal advice. Regulatory dates, scope, and enforcement details change. Confirm with qualified counsel before making compliance decisions.
SmartSuite provides work platform for standardizing workflows in the following areas:
- Governance, Risk & Compliance
- IT & Service Ops
- Project / Portfolio Management
- Business Operations















