This guide breaks down what compliance management means, why it carries more weight than ever for banks, fintechs, and healthcare organizations, and how to run a program that holds up when a regulator starts asking pointed questions.
TL;DR
- The job of compliance management is turning a stack of regulations into controls, evidence, and accountability auditors can verify, not running an annual prep sprint that goes quiet between audits.
- Regulated industries are carrying a heavier load in 2026, with DORA, HIPAA, SOC 2, NIS2, OCC interagency guidance, the CRI Profile, and the EU AI Act all overlapping and pulling at the same control libraries.
- Reactive programs collapse the moment two or three trigger events land in the same quarter, which is why mature compliance teams move toward continuous control monitoring and the Three Lines of Defense governance model.
- Mixing frameworks beats picking one, and most working programs run a blend of ISO 27001, NIST CSF 2.0, COSO ERM, SOC 2, and the CRI Profile depending on industry and customer demands.
- Tooling determines whether the program scales, and connected GRC platforms like SmartSuite are quietly replacing spreadsheets and certification-only tools across mid-market banking, fintech, healthcare, and insurance.
What is compliance management?
Compliance management is the operating discipline that takes a pile of regulatory obligations and turns them into something a business can actually run on a day-to-day basis.
That means controls with named owners, evidence with timestamps, policies with attestations, and a paper trail that survives a regulator's questions on a bad week.
The work isn't glamorous, but for regulated industries, the stakes are real.
A failed audit at a bank or hospital can mean a multi-million-dollar fine, a consent order that freezes new product launches, or a corrective action plan that ties up engineering for the next 18 months.
Underneath all of it, four jobs run on repeat:
- Figure out what rules apply to you.
- Design controls that satisfy those rules.
- Prove the controls actually work.
- Adjust when either the rules or the business shift.
What are the different types of compliance management?
Most regulated companies juggle several compliance regimes at once, not just one.
Regulatory compliance covers laws and rules that come straight from governments and supervisors: DORA for European financial institutions, HIPAA for U.S. healthcare, SOX for public companies, OCC interagency guidance for U.S. national banks, and NIS2 for important and essential entities across the EU.
A second layer comes from industry self-regulation, where the sector has agreed to enforce standards on itself.
PCI DSS for anyone touching cardholder data, NACHA for ACH transactions, the CRI Profile for financial institutions managing cyber risk, and the FFIEC IT Examination Handbook for U.S. banks all live in this bucket.
Then there's the information security stack that sits at the intersection of customer contracts and auditors: SOC 2 Type II, ISO 27001, ISO 27701, and the NIST Cybersecurity Framework, which enterprise buyers and partners increasingly demand before they'll sign.
Internal policy compliance is the layer nobody outside the company sees.
Access reviews, change management approvals, code review attestations, exception handling logs, all invisible until something goes wrong, and all of them show how the rest of the program actually gets enforced.
ESG and AI governance are the newest entrants.
Voluntary territory until recently, this category got real regulatory weight from the EU AI Act, the CSRD, ISO 42001, and the NIST AI Risk Management Framework.
For a fintech or a healthcare provider, the headache isn't any single regime.
It's how they overlap.
A SOC 2 control on quarterly access reviews can also satisfy parts of HIPAA's administrative safeguards, parts of ISO 27001's Annex A, and parts of DORA's ICT risk management requirements, but only if you've mapped them properly.
Why is compliance management important?
The cost of getting compliance wrong has gone up significantly in the last two years.
Regulators are issuing larger fines more frequently.
The OCC, the SEC, HHS OCR, and EU data protection authorities all stepped up enforcement during 2023 and 2024, and DORA's January 17, 2025, deadline added an entirely new front for European banks and their critical ICT providers.
Fines are the visible cost. Look harder, and the invisible costs usually run larger:
A delayed SOC 2 renewal stalling enterprise sales for a quarter, a failed HIPAA audit triggering a corrective action plan that ties up engineering for a year, a consent order with the OCC freezing new product launches until the bank proves it's remediated.
There's an upside argument here, too, and it's measurable rather than soft.
Enterprise deals in regulated verticals routinely turn on how fast and how cleanly your team can answer a 200-question security questionnaire, and increasingly on whether you can produce a DORA mapping or a CRI Profile assessment when asked.
What are the benefits of compliance management?
A working compliance program pays back in places most CFOs don't see on a P&L line, but feel everywhere else.
Audit prep stops being a fire drill once controls and evidence sit in one system with version history.
The team checks the status instead of reconstructing the last 12 months on a deadline.
In regulated verticals, compliance maturity can also shorten sales cycles directly.
Many customers in financial services, healthcare, and critical infrastructure now want SOC 2 reports, BAA-ready evidence, and DORA mappings on the call rather than three weeks later.
Third-party defensibility is another underrated win.
When a vendor breach lands on your perimeter, the first question regulators ask is whether reasonable diligence was in place beforehand, and that question goes much more smoothly when your vendor risk file isn't an email thread.
Remediation economics shift, too.
Catching a control gap in a quarterly review costs a fraction of catching it in an examiner's deficiency letter, and an order of magnitude less than catching it in the post-incident report.
How can you approach compliance management?
The default approach in some companies is reactive.
A regulator sends a request, sales loses a deal because of a missing certification, an auditor flags a deficiency, an enterprise customer escalates a failed security questionnaire, and the team lurches into action.
That works until two or three trigger events land in the same quarter, and at that point, everyone's burned out, and the program is still patchwork.
A more durable model comes from the Institute of Internal Auditors: the Three Lines of Defense.
- The first line is the business itself, where engineers, operations teams, line managers, and individual contributors own the controls in their day-to-day work because they're the ones executing them.
- The second line is compliance and risk, which designs the framework, monitors effectiveness, owns the regulator relationships, and translates regulatory expectations into operational controls.
- The third line is the internal audit, which independently verifies that the first two lines are doing what they say they're doing.
Some of the most expensive compliance failures usually happen when one team is wearing all three hats, and there's nobody left to catch the gap.
Beyond the structural piece, mature programs also move from point-in-time audits to continuous control monitoring, where controls are evaluated on a rolling basis with evidence captured automatically when possible.
How to conduct a compliance management assessment
A compliance management assessment is the structured exercise of figuring out what rules apply to you, what controls you have in place, and where the gaps live.
Worth distinguishing from an audit: an audit is a formal, usually independent verification of whether controls are operating as intended, while an assessment is the internal management exercise of mapping the terrain and finding gaps before an auditor does.
Both involve testing controls, but the audit is the higher-stakes formal review.
In practice, the assessment work runs as four overlapping phases:
Phase 1: Scope the obligations
The starting point is a clean list of every regulation, framework, and contract you're actually accountable to.
For a U.S. fintech, that might be SOC 2, PCI DSS, state money transmitter licenses, the BSA and AML rules, and customer-driven SOC 2 expectations baked into MSAs.
A European bank's list looks more like DORA, GDPR, EBA guidelines, and national regulator-specific requirements.
Each obligation has to tie back to something specific: a regulatory citation, a contract clause, an internal policy, or a customer agreement.
Anything you can't tie to a source doesn't belong on the list.
Phase 2: Map controls to obligations
Each obligation needs at least one control behind it, and a control is a specific, repeatable activity rather than an aspiration:
- Quarterly access reviews.
- Annual penetration testing.
- Encryption of data in transit and at rest.
- Vendor risk assessments before onboarding.
Mapping is where most programs find redundancy that they can actually recover.
A single control on multi-factor authentication might satisfy parts of SOC 2, ISO 27001, HIPAA, NIST CSF, and DORA all at once, and mapping it once and reusing it everywhere is the difference between a program you can afford to run and one that drowns in duplicate work.
Phase 3: Test the controls
Until you've verified it works, a control on paper is a hypothesis.
Two flavors of testing matter: design testing, which asks whether the control as written would actually achieve its purpose if executed faithfully, and operating effectiveness testing, which asks whether it's being executed consistently in the real world.
Sample sizes, frequency, and evidence requirements vary by framework.
SOC 2 Type II typically requires control testing across the audit period, while DORA expects continuous monitoring for ICT-related operational resilience controls.
Phase 4: Remediate and report
Each gap from testing needs an owner, a remediation plan, a target date, and a verification step that confirms the fix has been made.
The biggest failure mode here is letting findings sit.
A finding without a deadline turns into a finding next year, then a deficiency, then an audit issue, and eventually an enforcement matter.
The cleanest programs maintain a single issues log running across all frameworks, so a control gap surfaced during a SOC 2 audit also triggers updates to the HIPAA, ISO 27001, and DORA mappings tied to it.
What are the different compliance management frameworks?
Frameworks are the shared language compliance teams use, and most working programs blend two or three depending on industry, regulators, and customer expectations.
- You can start with ISO 27001, the international standard for information security management systems and the framework most enterprise customers in Europe and APAC will ask for first.
Its 2022 revision restructured Annex A into four themes (organizational, people, physical, and technological) to align with cloud and supply chain risks.
The U.S. equivalent in practice is SOC 2 Type II, which is technically an attestation report rather than a certification, but functioning as the de facto gate for SaaS sales into mid-market and enterprise accounts.
Its five Trust Services Criteria (security, availability, processing integrity, confidentiality, and privacy) let you scope the audit to what's relevant to your service.
- Federal contractors and U.S. critical infrastructure increasingly run on the NIST Cybersecurity Framework.
- For public companies and the audit committees watching over them, COSO ERM is usually the default.
It ties risk and compliance to enterprise strategy, and most internal audit teams already speak its language.
- DORA, the EU's Digital Operational Resilience Act, became enforceable on January 17, 2025, and it's reshaping how European financial institutions and their critical ICT providers handle operational resilience, third-party risk, incident reporting, and threat-led penetration testing.
- Over in U.S. banking, the Cyber Risk Institute's CRI Profile has gained real ground after the FFIEC sunset its Cybersecurity Assessment Tool in August 2025.
Learn how you can use SmartSuite for CRI compliance: SmartSuite for Cyber Risk Institute (CRI) Compliance
Its cross-mapping lets cyber controls satisfy NIST CSF, ISO 27001, and other frameworks at once, which means banks don't have to rebuild the library for each audit lens.
- For U.S. healthcare, the floor is still HIPAA: the Security Rule, the Privacy Rule, and the Breach Notification Rule.
What kind of tools can you use for compliance management?
Compliance tooling lands in a handful of distinct categories, and the right pick depends on program maturity, industry, and regulatory load.
- Most teams start with a mix of Excel for the control library, Google Drive or SharePoint for evidence, shared inboxes for auditor back-and-forth, and a long Slack thread.
Cheap and familiar, until it stops scaling.
The breaking point usually comes with the second framework, an auditor asking for a clean change history, a regulator wanting to know who approved a policy revision in 2024, or an examiner requesting a 30-day evidence pull at midnight.
- Compliance automation platforms, such as Vanta, Drata, Sprinto, Secureframe, and Scytale.
They handle automated evidence collection from cloud infrastructure, identity providers, and HR systems well, which removes most of the manual screenshot-chasing.
However, many of these tools were built around the audit, not the full breadth of GRC.
- Enterprise GRC platforms, such as Archer, MetricStream, IBM OpenPages, LogicGate, and Workiva, sit at the other end of the spectrum, purpose-built for large GRC programs with deep risk modeling, policy lifecycle management, audit workflows, regulatory change tracking, and board reporting.
The catch is what it takes to run them: integration partners, onboarding cycles measured in months rather than weeks, and license costs that explain why these platforms live at Tier 1 banks and Fortune 500s.
Then there's a newer category that doesn't fit cleanly into any of the boxes above.
- Connected work management platforms like SmartSuite, Monday, and Asana blend the customization of a flexible work platform with the depth of a dedicated compliance tool, which fits well for mid-market banks, fintechs, healthcare organizations, and insurance carriers that want compliance connected to the rest of their operations rather than walled off in a specialty tool.
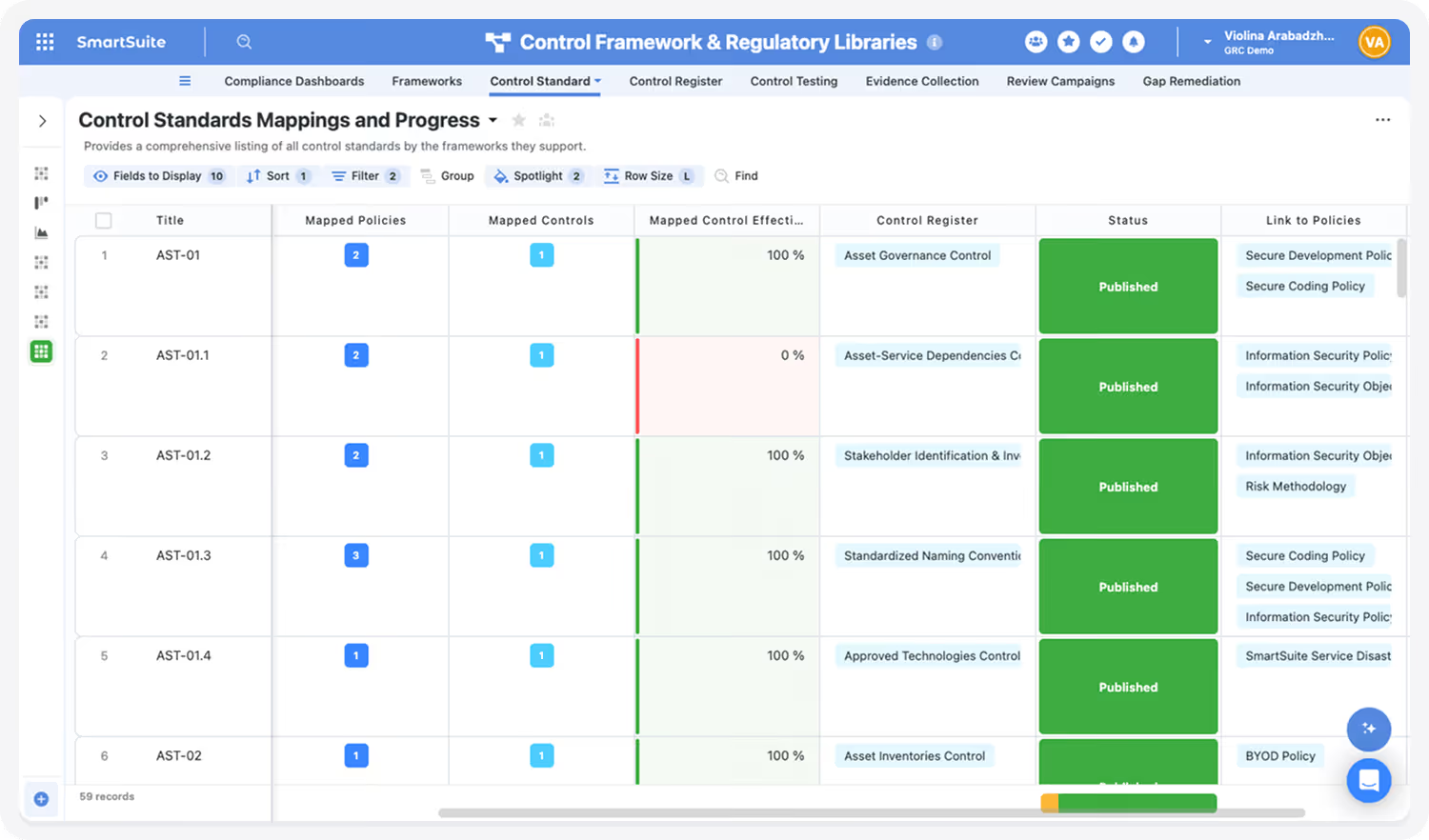
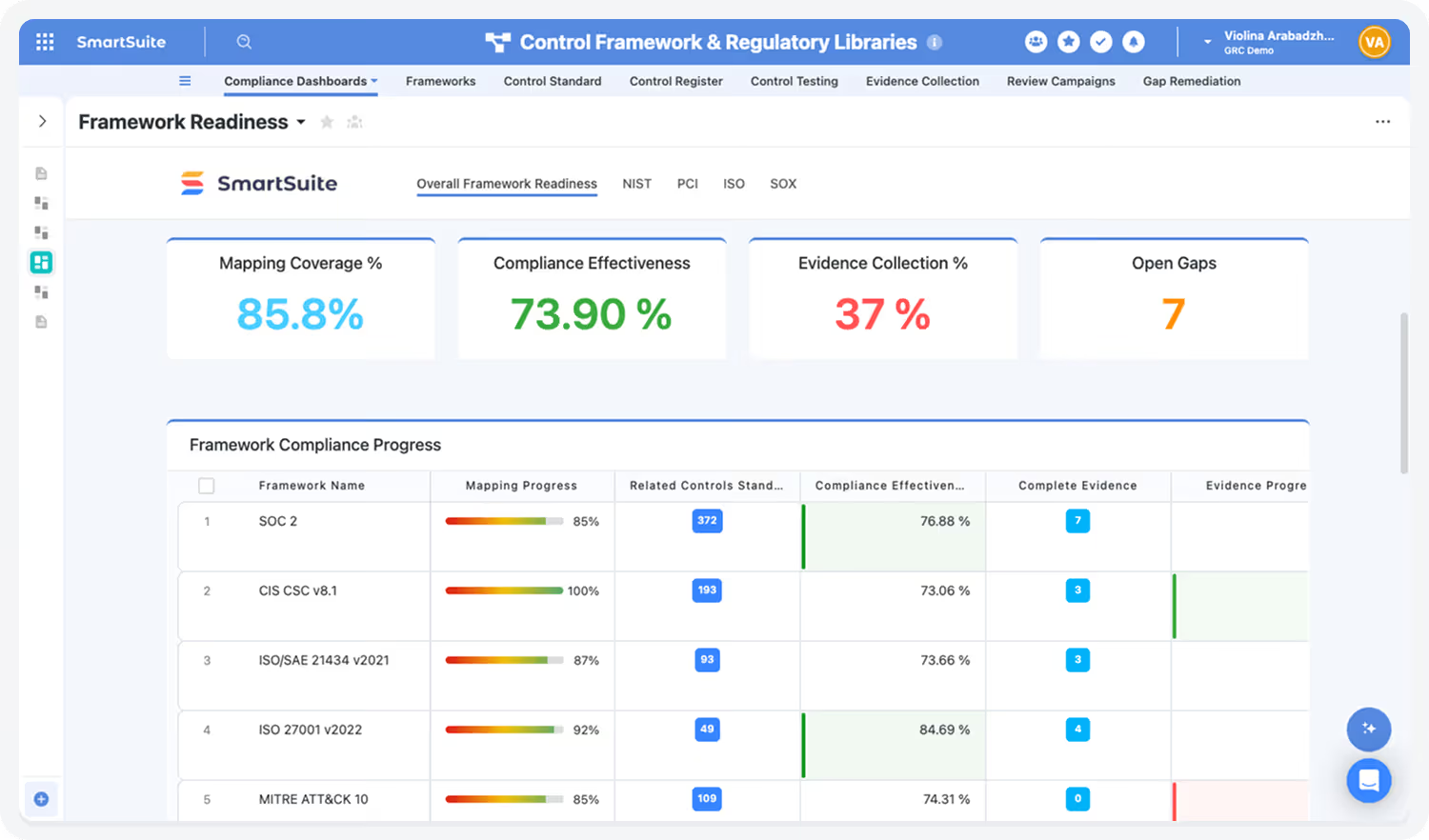
➡️ SmartSuite built its Compliance Management Suite as a purpose-built solution category, not a generic work platform with audit templates bolted on.
The core idea behind the suite is "test-once, comply-many."
Map a control once to SOC 2, ISO 27001, HIPAA, DORA, and the CRI Profile, then reuse it across audit cycles instead of rebuilding the library every time a new framework lands.
That mapping logic flows through the rest of the suite.
- Compliance Assessments & Testing handles recurring assessment campaigns with a reusable question library and automated evidence requests.
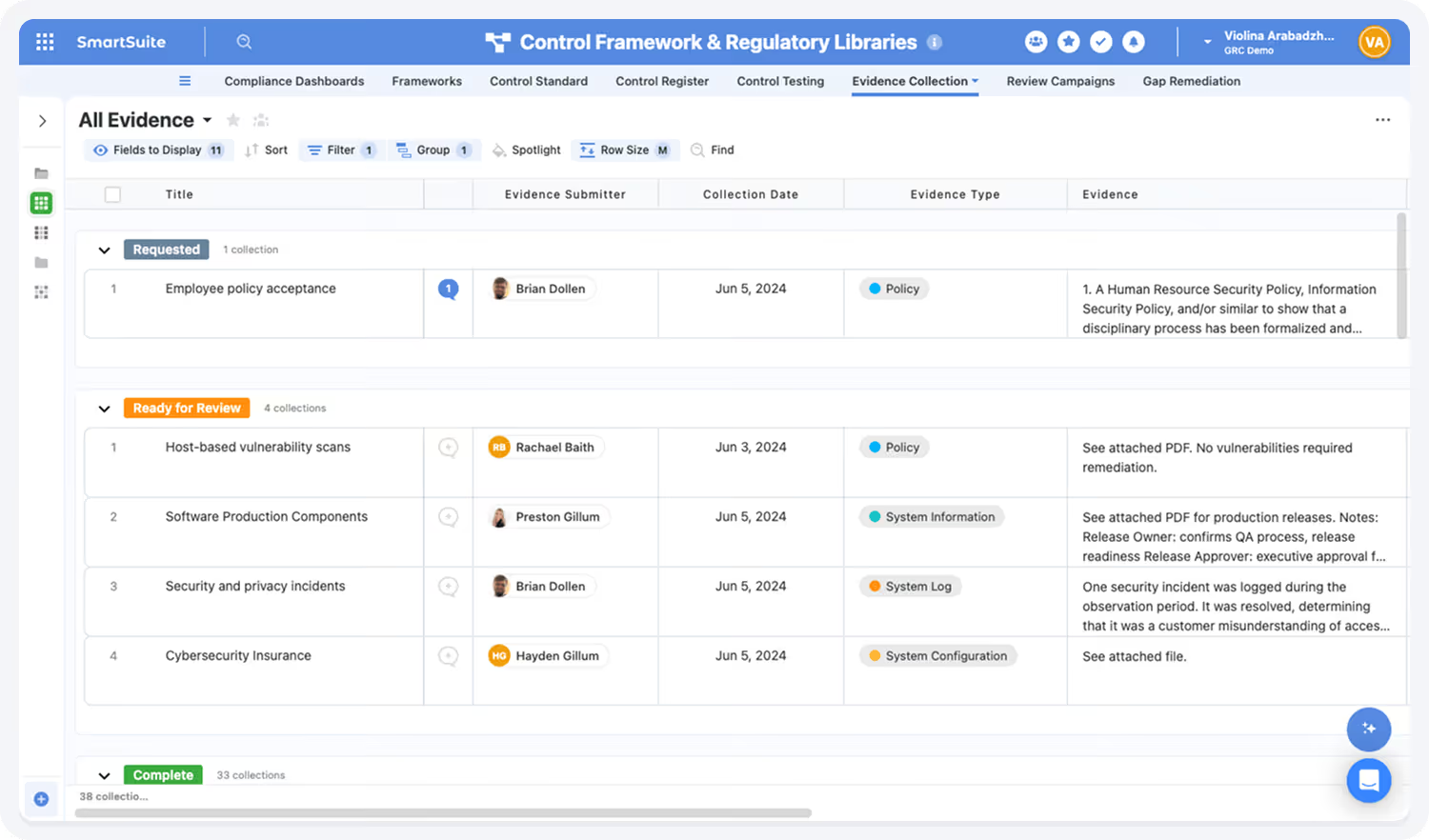
- Policy Management runs the full lifecycle (creation, review cycles, approvals, versioning, distribution, and attestation logging), so when an auditor asks who acknowledged the latest information security policy and when, the answer is one click rather than three weeks of email archaeology.
- Issues Management ties findings from audits, control tests, assessments, and incident reviews into a single remediation queue, with structured ownership, root cause analysis, follow-up workflows, and audit-traceable closure tracking.
- Regulatory Change Management tracks supervisor updates, runs impact analysis on existing controls and policies, and surfaces what needs updating, which is where most programs without dedicated tooling fall behind.
- Regulatory Inquiries lives in the same workspace, so when an examiner schedules an exam or sends a request, the team responds from the same system the policy was approved in rather than pulling from five different tools.
For U.S. banks, SmartSuite's 2025 partnership with the Cyber Risk Institute delivers structured CRI Profile workflows for institutions transitioning off the discontinued FFIEC CAT framework.
SmartSuite AI handles the tedious parts (summarizing vendor questionnaires, drafting policy revisions, flagging gaps in incident reports, and pulling first-draft control narratives) without making governance decisions on its own.
Real-time dashboards roll all of it up into live KPIs and executive-ready reports on control health, framework readiness, overdue items, and remediation status, so compliance leaders and audit committees see the same numbers without waiting for a quarterly PDF.
Pricing starts at $15/user/month for the Team plan, with solution-based pricing available for regulated enterprises that need to structure access by department, region, or regulatory scope.
Learn how you can use SmartSuite for compliance management: Compliance Management -- GRC Solution Walkthrough | SmartSuite
Pick the compliance tool that actually fits how your team works
The honest test isn't which tool is best on paper. It's which tool your team will still be using in 18 months when the program has doubled in scope.
You can start with where the last audit went sideways.
- Manual evidence collection running you up against a SOC 2 deadline? A compliance automation tool like Vanta or Drata moves you forward fast.
- A Tier 1 bank's worth of frameworks across multiple business lines with a custom risk taxonomy nobody else can read? Enterprise GRC platforms like Archer or IBM OpenPages are still where the depth lives.
For most teams between those two ends, especially mid-market banks, fintechs holding state regulator licenses, healthcare organizations carrying HIPAA alongside SOC 2, and insurance carriers managing NAIC and state DOI requirements, the answer increasingly looks like a connected work management platform.
That's the gap SmartSuite was built to fill.
It runs the whole program from one workspace: framework libraries, controls, evidence, policies, audits, regulatory change tracking, issues management, and remediation, with cross-mapping across SOC 2, ISO 27001, HIPAA, DORA, NIST CSF 2.0, and the CRI Profile baked in rather than bolted on.
What that means practically: when a SOC 2 control test fails, the same finding updates the HIPAA, ISO 27001, DORA, and CRI mappings tied to it without manual work.
When a new regulation lands, Regulatory Change Management surfaces which policies and assessments need updates.
When an examiner asks for a year-end attestation log, the team produces it from the same system in which the policy was approved.
Audit trails, role-based permissions, segregation of duties, and compliance certifications are part of the platform rather than paid add-ons.
➡️ Start a free SmartSuite trial or book a demo to see how your compliance team can run the entire program from one connected workspace.
⚠️ Disclaimer: This article is for general information and isn't legal advice. Regulatory dates, scope, and enforcement details change. Confirm with qualified counsel before making compliance decisions.
Read more
- Financial Risk Management: Definitions & Best Practices
- What is GRC (Governance, Risk, and Compliance)?
- How To Choose a GRC Tool: Factors To Evaluate & Vendors
- GRC Audit: What Is It & How To Conduct One?
- Risk Management: What Is It & Why It's Important?
- How To Choose a Risk Management Platform?
- Third-Party Risk Management: What Is It & How It Works?
- Compliance Risk: What Is It & Why You Should Care?
- Vendor Compliance: What Is It & Why You Should Care?
- AI Risk Management: Definitions & Frameworks
SmartSuite provides work platform for standardizing workflows in the following areas:
- Governance, Risk & Compliance
- IT & Service Ops
- Project / Portfolio Management
- Business Operations















