In this guide, I'll cover what third-party risk management is, the kinds of risk vendors introduce, how to run an assessment, the frameworks worth knowing, and the tools modern programs are actually built on.
TL;DR
- Third-party risk management is the ongoing work of identifying, scoring, and monitoring threats that vendors, suppliers, contractors, and partners bring into your business.
- Vendor risk shows up in many forms, including cyber, operational, compliance, financial, reputational, geopolitical, concentration, ESG, AI, and fourth-party exposure.
- Choosing a response means matching one of the five recognized actions (mitigate, transfer, avoid, share, accept) to the criticality of the vendor relationship.
- Framework choice usually answers itself, because the regulators and frameworks that apply in your jurisdiction (NIST, FFIEC, OCC, DORA) decide most of what your program needs to look like.
- The right platform matters, since spreadsheets and disconnected tools create blind spots, and connected GRC platforms like SmartSuite tie vendor risk to controls, audits, and remediation in one governed workspace.
What is third-party risk management?
Third-party risk management (TPRM) is the structured way an organization identifies, evaluates, and monitors the threats that come from outside the systems that its own team directly controls.
It applies to anyone you've handed work, money, data, system access, or brand reputation to: SaaS vendors, cloud providers, payroll processors, marketing agencies, contractors, joint venture partners, and (increasingly) the AI providers behind your own AI features.
The reality of vendor risk in 2026 is that the boundary between "your stack" and "their stack" is mostly fictional.
When your CRM vendor goes down, your sales team stops working that morning.
A breach at your payroll provider puts your employees' SSNs on a forum somewhere.
If your sub-processor's sub-processor has a hiring freeze, your support tickets quietly stop getting answered.
A TPRM program exists to surface those exposures early, tie each vendor to an internal owner, score them against the right depth of due diligence, keep watch as things change, and document every decision along the way.
➡️ The teams doing this well don't treat vendor risk as a once-a-year questionnaire scramble.
They treat it as continuous oversight stitched into procurement, security, legal, and operations.
What are the different types of third-party risk?
Vendor risk doesn't show up in a single shape, and pretending it does is how mature programs miss things.
Cyber risk is the headline category most teams start with.
Account takeovers, ransomware spreading through a vendor's connection, breaches at a sub-processor, and supply-chain malware planted in routine software updates are the patterns that show up most often.
On the operational side, anything that disrupts service delivery from a vendor's side falls in scope.
- Outages, fulfillment failures, capacity shortfalls, and key staff leaving usually hide until they're already affecting customers.
- When a vendor falls short of GDPR, HIPAA, SOX, DORA, the EU AI Act, or the SEC cyber disclosure rules, the compliance hit lands on you. Regulators don't care that the failure happened at a sub-processor. The obligation sits with whoever owns the relationship.
- Late filings, missed payroll runs, mass layoffs, or a parent company restructuring all signal financial trouble at a critical vendor.
- A supplier that's months from going dark has an outsized chance of cutting corners on security and service in the meantime.
- Poor labor practices at a supplier, biased outputs from an AI vendor, or a partner caught in a sanctions investigation can drag your brand into the same news cycle.
- Strategic risk shows up when a vendor's roadmap drifts away from yours, when a competitor acquires them, or when they pivot to a market that no longer includes you.
- Geopolitical and concentration exposure have become impossible to ignore since 2022.
Tariff swings, shifting sanctions regimes, single-region supplier dependence, and over-reliance on a single provider for a critical service all put real continuity at stake.
ESG sits firmly inside vendor reviews now, especially for public companies and EU-regulated entities.
Carbon disclosures, modern slavery statements, ethical sourcing claims, and supply chain transparency reports all flow upstream into your reporting.
Down the chain, you also carry exposure from your vendors' vendors.
If your CRM uses a hosting provider that uses a CDN that gets breached, the chain still ends at your data.
That's fourth-party (or nth-party) risk, and it's the hardest category to keep visibility on.
AI risk is the newest category that most TPRM teams are scrambling to cover.
Model drift in vendor-supplied AI, training data sourced from copyrighted material, embedded LLMs that hallucinate inside customer support, and shadow AI usage by your suppliers' employees are all areas regulators and auditors now ask about.
Why is third-party risk management important?
The short answer: because the average enterprise relies on hundreds of vendors, and any one of them can become your worst quarter.
The longer answer is that TPRM does several things at once for the business:
- It puts visibility against an ecosystem that's grown faster than most procurement teams can track.
- It gives security, legal, compliance, and procurement functions a shared system instead of four disconnected spreadsheets.
- And it gives leadership a defensible answer when the board, auditors, regulators, or insurers ask what happens if a critical vendor has a bad day.
Regulatory pressure is also a real driver here.
DORA went live in January 2025 across the EU financial sector, and its third-party requirements are some of the strictest ever written.
US federal banking regulators released their joint Interagency Guidance on Third-Party Relationships in 2023, replacing the older patchwork of agency-specific guidance, including OCC Bulletin 2013-29 and the Federal Reserve's SR 13-19.
The SEC's cybersecurity disclosure rule turned vendor breaches into material events for public companies overnight.
➡️ Companies with real visibility into vendor exposure can negotiate harder, switch faster, and absorb shocks better than competitors who only learn about a vendor problem after it's already in production.
What are the benefits of third-party risk management?
A working TPRM program pays off across procurement, legal, finance, and security at the same time.
Some of the wins worth calling out:
- Faster vendor onboarding when diligence steps live in a workflow instead of a chain of emails.
- Cleaner audit responses, with evidence, scores, and decisions tied to specific vendors and specific dates.
- Lower breach exposure as risky vendors get caught at intake, not after they've already had an incident.
- Better insurance terms. Cyber insurers now ask about third-party programs in detail before pricing your policy.
- Stronger vendor relationships, since suppliers know what's expected of them, when reviews happen, and how scoring works.
- Fewer renewal surprises. Contract dates, SLAs, and risk reviews sit alongside each other instead of in three different systems.
The pattern shows up clearly in how organizations handled DORA.
Financial entities that built their ICT third-party register, classified critical contracts, and drafted exit strategies through 2024 walked into the January 2025 deadline with the work largely done.
The ones still treating TPRM as quarterly spreadsheet hygiene are now backfilling under regulator pressure, with much higher costs and tighter timelines.
I’ve noticed that the same dynamic plays out for SaaS companies hit with enterprise security questionnaires.
💡 Mature TPRM data answers questions in days; an immature program bleeds weeks of engineering time.
How can you respond to third-party risks?
Identifying a vendor risk is the easy part. Deciding what to do about it is where most programs lose momentum.
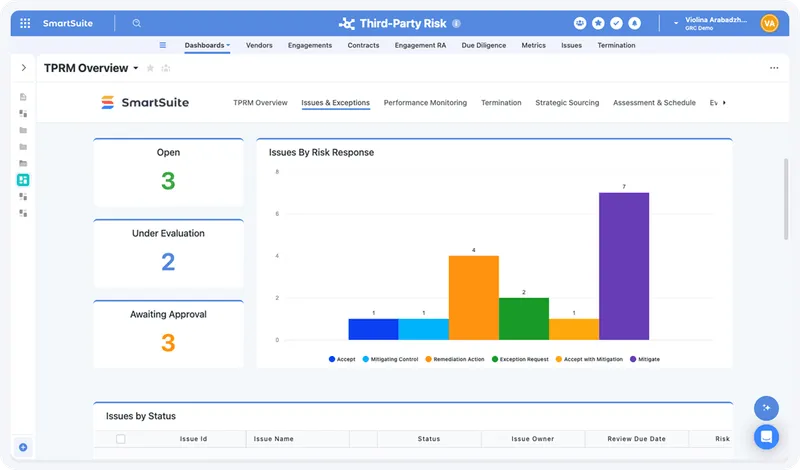
The five recognized responses are mitigate, transfer, avoid, share, and accept.
None of them is universally correct.
Each fits a specific kind of risk, and TPRM programs that treat mitigation as the default for everything end up wasting effort on small risks while missing big ones.
Here's how each plays out in vendor risk:
- Mitigate is where most TPRM work lives.
You can influence the vendor's controls, the contract, or the way your organization uses them.
Common examples include requiring MFA before granting system access, signing a security addendum that mandates breach notification timelines, requesting a remediation plan for SOC 2 exceptions, and insisting on encryption at rest before data leaves your perimeter.
- Transfer moves the financial consequence of a risk somewhere else.
Cyber insurance with third-party coverage, contractual indemnification language, and sub-processor flowdown clauses all transfer some part of the loss exposure. Probability stays the same; only the cost-bearer changes.
- Avoid is the response most teams underuse.
If a vendor can't pass core diligence, fails financial checks, operates from a sanctioned jurisdiction, or won't agree to baseline contractual security terms, the right answer is often "we don't engage."
Avoiding a risky vendor at intake costs less than mitigating one already in production.
- Share applies to joint accountability arrangements.
It's less common in vendor risk than in enterprise risk, but it does show up in joint venture partnerships, syndicated services, and shared infrastructure deals where two parties carry the loss together.
- Accept is the right call for low-criticality, low-impact vendors where the cost of mitigation exceeds the expected loss.
A small vendor with no system access, no regulated data, and a peripheral business role gets logged, assigned an owner, and revisited at renewal.
The trap most programs fall into is treating every vendor like a tier-1 vendor.
A full SIG Core questionnaire (600+ questions) sent to a single-seat design tool is overkill.
Buying cyber insurance to cover losses from a vendor with no data access is wasted spend.
Match the response to the actual exposure, and your program scales without burning out the team running it.
How to conduct a third-party risk management assessment
A TPRM assessment isn't a single event.
It's a sequence of activities that runs across the entire vendor relationship, from the day procurement spins up a contract to the day you cut the vendor's access for good.
Most regulatory frameworks describe the lifecycle in five stages.
The labels differ between OCC's Interagency Guidance, DORA, FFIEC, and NIST, but the underlying flow is consistent:
Stage 1: Inventory and tiering
Start by pulling data from procurement, finance, security, legal, and IT to build a complete vendor list.
I’ve seen many times how the first time large organizations run this exercise honestly, they surface more vendors than the procurement system thought existed, because shadow IT is real.
After that, you want to tier each vendor by inherent risk:
- Data sensitivity.
- System access.
- Financial dependence.
- Customer impact.
- Regulatory exposure.
A four-tier model (critical, high, medium, low) is enough for most programs.
Tiering decides every downstream choice, including how deep the diligence goes and how often reviews repeat.
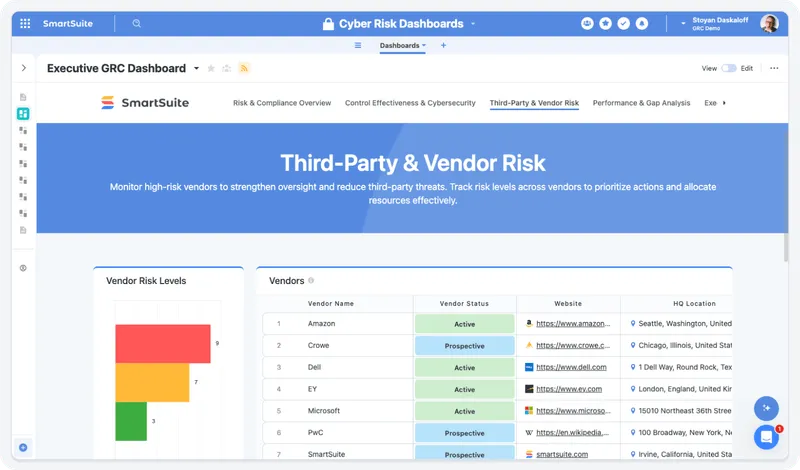
You can unify all vendor records, risk profiles, and assessments in a single, searchable workspace with SmartSuite.
Our platform provides a complete picture of your third-party ecosystem and offers linked records for vendors, contracts, and assessments and configurable fields for custom risk categories.
Stage 2: Due diligence
You want to match the depth to the tier.
Critical vendors get a full SIG Core questionnaire, SOC 2 review, financial check, sanctions screening, and a real conversation with their security team.
Medium vendors get a SIG Lite or a tailored question set. Low-risk vendors get a short attestation and an annual nudge.
Score the findings against your control library, document the gaps, and decide on a response.
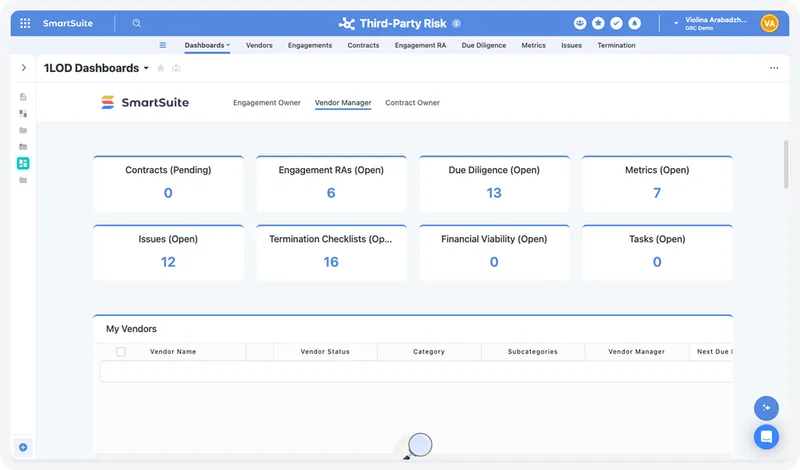
With SmartSuite, you can automate data collection, risk scoring, and approval workflows for new vendors to accelerate onboarding without compromising compliance.
You can build customizable onboarding templates and questionnaires, as well as integrated approval routing with audit history.
Stage 3: Contracting and onboarding
Bake the risk decisions into the agreement.
Security addendums, SLAs, audit rights, exit clauses, breach notification timelines, sub-processor approval rights, and insurance requirements all anchor here.
Whatever isn't in the contract is voluntary. Treat each vendor agreement as a security document, not just a commercial one.
Stage 4: Monitoring and remediation
Vendor risk doesn't stand still.
- Companies get acquired.
- Controls drift.
- New regulations land.
- Sub-processors change without telling anyone.
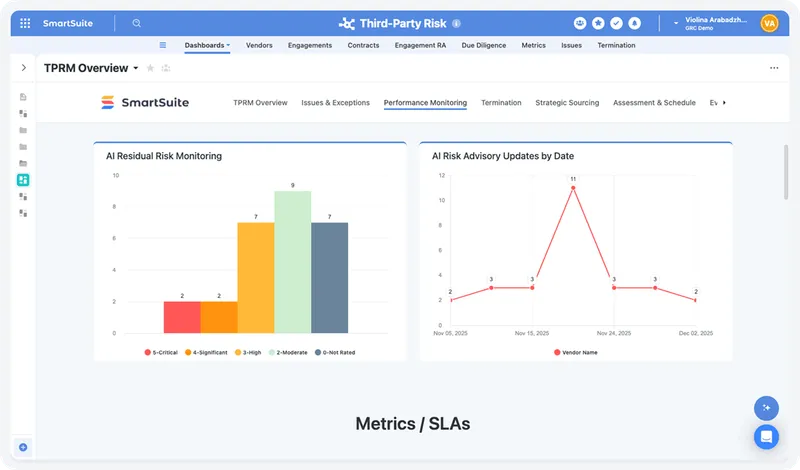
💡 Continuous monitoring blends scheduled reassessments with always-on signal: external risk scoring feeds, breach notifications, news alerts, financial filings, and changes to vendor questionnaire responses.
Every finding gets an owner, a target date, evidence requirements, and a closeout review.
SmartSuite helps risk leaders move from point-in-time assessments to continuous oversight. You can conduct scheduled reassessments, trigger-based reviews and build real-time dashboards for risk exposure.
Stage 5: Offboarding
I think that this is the most neglected stage in most TPRM programs, and the one auditors are starting to ask about.
Access revocation, data return or destruction, final audits, and documented termination of the relationship all matter for regulatory and contractual reasons.
A vendor with active credentials a year after you stopped paying them is a finding waiting to happen.
Worth noting: the lifecycle isn't strictly linear in practice.
Findings from Stage 4 often kick a vendor back into Stage 2 for re-assessment.
An acquisition that brings new vendors into scope sends Stage 1 work into your inbox without warning.
The point of running the lifecycle as a system rather than a checklist is that the program keeps working when reality doesn't follow the script.
What are the different third-party risk management frameworks?
The framework question usually answers itself. Where you operate and who regulates you decides most of it.
Programs that try to standardize on a single framework regardless of context end up either over-engineered or out of compliance with their actual obligations.
💡 The smarter path is to identify which frameworks apply to your business, then layer them appropriately.
The NIST family covers two related areas.
NIST SP 800-161r1, revised in 2022, is the dominant US federal reference for vendor and supply chain cyber risk, and it's the baseline if you sell to federal agencies or federal contractors.
NIST CSF 2.0 added a "Govern" function in 2024 that elevated governance and supply chain oversight to a core function alongside Identify, Protect, Detect, Respond, and Recover, with cybersecurity supply chain risk management sitting as one of its six categories.
For US banks and credit unions, the FFIEC IT Handbook and the 2023 Interagency Guidance from the OCC, FDIC, and Federal Reserve set the operational bar.
The 2023 guidance consolidated prior agency expectations from each regulator and is now the dominant US banking reference for third-party relationships.
EU financial entities and their critical ICT vendors operate under DORA (Digital Operational Resilience Act), in force since January 2025.
Its requirements include a mandatory register of information, contractual provisions, exit strategies, concentration risk reviews, and direct regulator inspection rights over critical providers.
Two ISO standards anchor the methodology layer.
ISO 27036 is the international counterpart to NIST 800-161, focused on information security in supplier relationships, while ISO 31000 defines enterprise-level risk management principles that TPRM programs borrow for their identify, analyze, evaluate, treat, and monitor loop.
ISO 27001:2022 controls A.5.19 through A.5.23 govern supplier risk specifically and most security teams will already be familiar with them.
The questionnaire layer is largely standardized around Shared Assessments SIG and SIG Lite, which most enterprise security teams expect to see at intake.
Cloud Security Alliance's CAIQ questionnaire and CCM control matrix play complementary roles for SaaS- and cloud-specific assessments, with CAIQ used for vendor responses and CCM mapping the underlying controls.
Sitting above all of these, the OCEG GRC Capability Model is more of an integration blueprint than a standalone framework, built for organizations that want governance, risk, and compliance running as one system rather than several functions reporting to different VPs.
The goal isn't framework purity.
It's a TPRM program with the right reference for each layer (regulatory baseline, security questionnaire, methodology, certification mapping) and the operational maturity to run them together.
What kinds of tools can you use for third-party risk management?
Tooling for TPRM scales with two things: the size of your vendor portfolio and the number of regulated frameworks you're answering to.
A 50-vendor program with one annual auditor expects different things from a 5,000-vendor program facing examiners every quarter.
The market sorts roughly into five categories.
- Spreadsheets and shared drives still run a surprising number of small programs.
They're free, familiar, and workable until the vendor count climbs past a few dozen, or until the first auditor asks for a defensible audit trail.
- Dedicated TPRM platforms cover the full vendor lifecycle out of the box.
Prevalent, ProcessUnity, OneTrust, Whistic, and Venminder all sit here, with questionnaire automation, vendor portals, evidence collection, tiering, and continuous monitoring.
The trade-off is cost, plus the tendency for vendor risk to live separately from the rest of your GRC stack.
- External risk intelligence is a different layer entirely.
SecurityScorecard, Bitsight, and UpGuard score vendors based on outside-in cyber signals (open ports, expired certificates, dark web mentions, breach history).
Useful as a continuous monitoring feed, less so as a standalone TPRM platform.
- Enterprise GRC suites take the broadest scope.
Archer, MetricStream, IBM OpenPages, ServiceNow GRC, and Riskonnect fold TPRM into a wider risk and compliance environment that handles the full GRC mandate. Implementation cycles run in quarters, and budgets follow.
- Compliance automation platforms, such as Vanta, Drata, Sprinto, Scytale, and Secureframe, come at TPRM from the certification side.
They focus on SOC 2 and ISO 27001 work and have added vendor risk as an adjacent capability, which fits well when TPRM is a smaller part of your overall compliance posture.
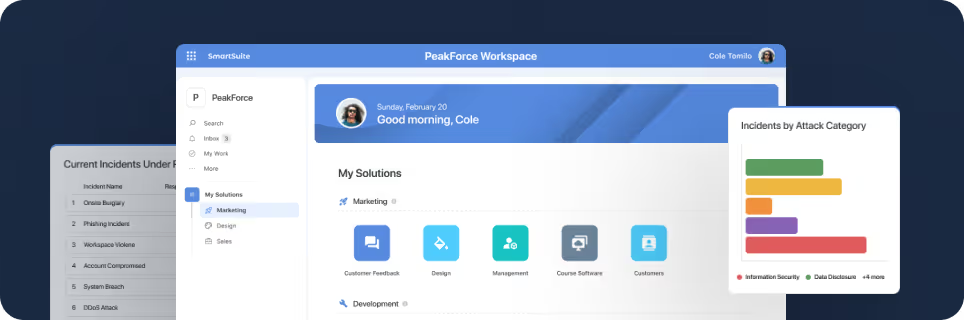
- Connected Work OS platforms are the newest entrant in this space, with TPRM workflows running alongside the rest of operations in one no-code environment. SmartSuite is the example here.
➡️ Our platform is built for organizations that want vendor risk connected to the rest of their GRC and operations work, instead of locked inside a specialist tool.
SmartSuite brings vendor inventory, due diligence questionnaires, tiering, contract obligations, monitoring cadences, issue tracking, and remediation workflows into one no-code workspace, so security, legal, procurement, and compliance can stop pulling from separate systems every time leadership asks for a vendor risk update.
- Built-in AI handles the repetitive parts.
- SmartDoc summarizes long questionnaire responses.
- The AI Field Agent flags missing context or anomalies in vendor records.
- Third-party risk intelligence maps findings back to required controls and frameworks.
Every AI suggestion goes through human review, so governance stays auditable.
What separates SmartSuite from purpose-built TPRM tools is flexibility.
You build the program around how your vendor lifecycle actually runs, with relational data models, role-based interfaces, and over 40 field types, instead of templates that fight your process.
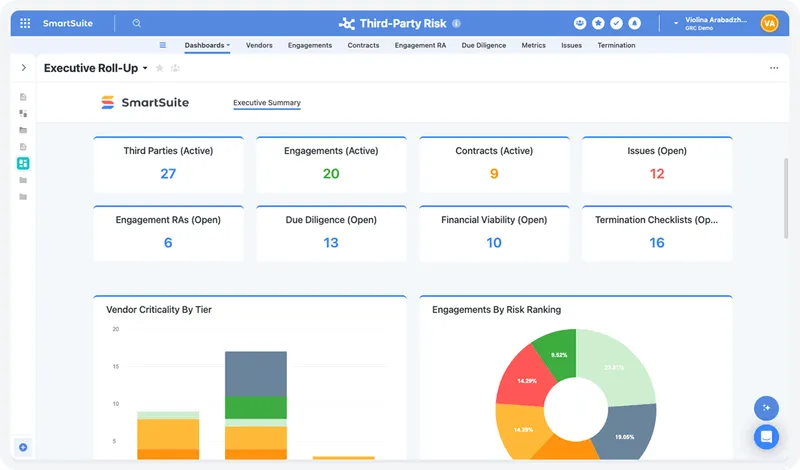
Live dashboards give a shared real-time view of vendor exposure, audit logs keep every change defensible, and SmartSuite Studio lets you adapt the workspace as new regulations or new vendor categories enter scope.
The platform fits well for mid-market companies, regulated industries like banking and healthcare, and TPRM teams who want vendor risk connected to contracts, audits, and incidents in one place.
Pricing starts at $15 per user per month for the Team plan, with solution-based pricing available for regulated enterprises that need access structured by department or regulatory scope.
Choose the TPRM platform that fits your program
Each tool category covered above is built for a different kind of program.
- Dedicated TPRM platforms like Prevalent and ProcessUnity work well when vendor risk is a deep, standalone discipline with significant headcount behind it.
- External risk intelligence feeds (SecurityScorecard, Bitsight) earn their place as a monitoring layer on top of whatever assessment tool you already run.
- Enterprise GRC suites suit large regulated organizations with the implementation budget and the breadth of risk programs to justify the cost.
- Compliance automation tools handle certification-driven TPRM well, less so for programs where vendor risk has its own scope and cadence.
The harder question is what to do when your program has outgrown its tooling but your business doesn't sit cleanly inside any one of those categories.
You need a platform that runs the full vendor lifecycle, connects to procurement, legal, security, and operations, and can be turned on without a six-month implementation contract.
This is the slot SmartSuite was built for.
The platform pairs no-code flexibility with the governance controls regulated programs need (granular permissions, full audit logs, AI governance, SCIM provisioning, SSO), so vendor risk runs alongside contract management, audit work, incident response, and remediation tracking inside one connected workspace.
Vendors, contracts, assessments, controls, incidents, and remediation tasks share the same data model, with live dashboards built on top and AI assistance embedded across every workflow.
➡️ Start a free SmartSuite trial or book a demo to see how your team can manage governance, risk, and compliance in one place.
SmartSuite provides work platform for standardizing workflows in the following areas:
- Governance, Risk & Compliance
- IT & Service Ops
- Project / Portfolio Management
- Business Operations















