SmartSuite Solutions
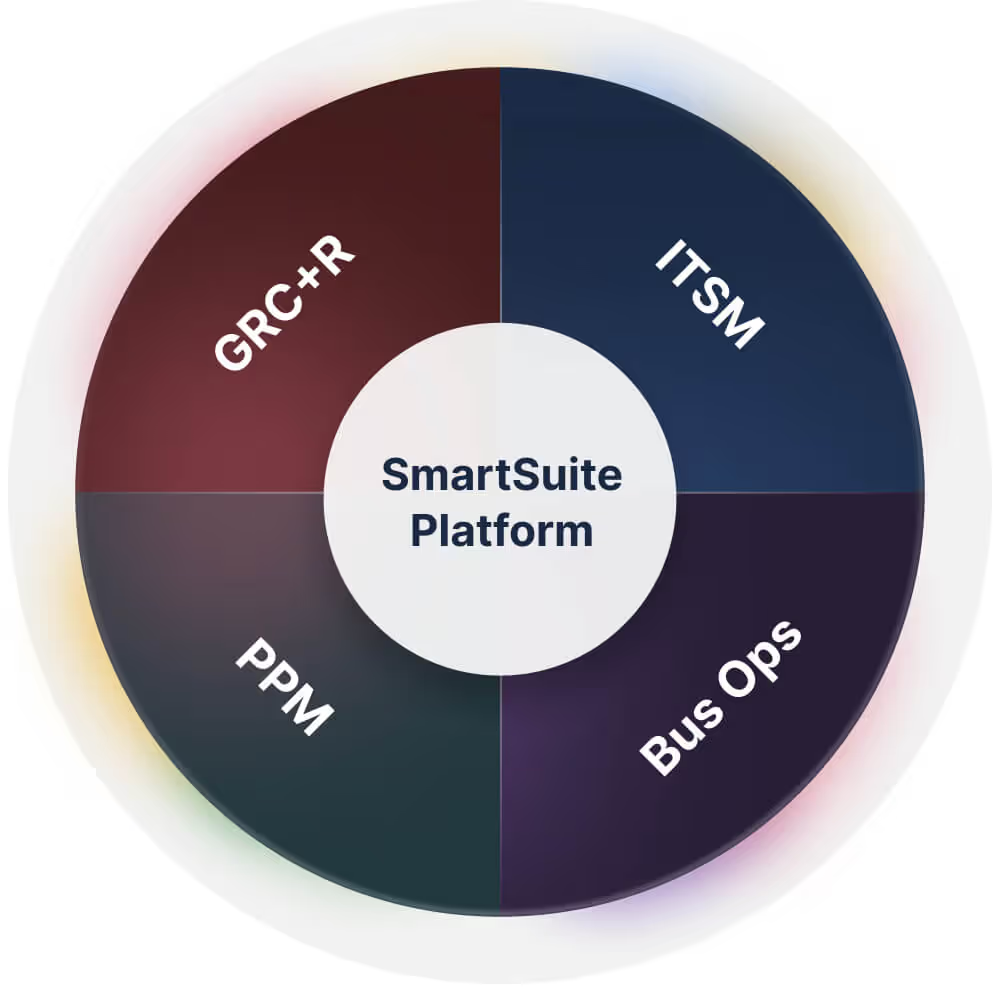
SmartSuite delivers purpose-built solution suites for GRC, IT & Service Delivery, Projects & Portfolios, and Business Operations—powered by a unified platform to build, connect, and scale workflows across your organization.

Solution Areas
One Platform for Governance, Risk, Compliance and Resilience, IT Service Delivery, Project & Portfolio Management, and Business Operations
Unify risk, compliance, audit, third-party risk, operational resilience, business continuity, regulatory readiness, privacy, AI governance and ESG.
Manage incidents, changes, requests, assets, and service operations – with connections to workflows, automation, and real-time visibility.
Unify portfolio reporting across projects and initiatives - so teams stay aligned on priorities and leaders can track progress against ORKs in real time
Manage sales, marketing, product, operations, human resources, procurement, and more - across teams and departments.
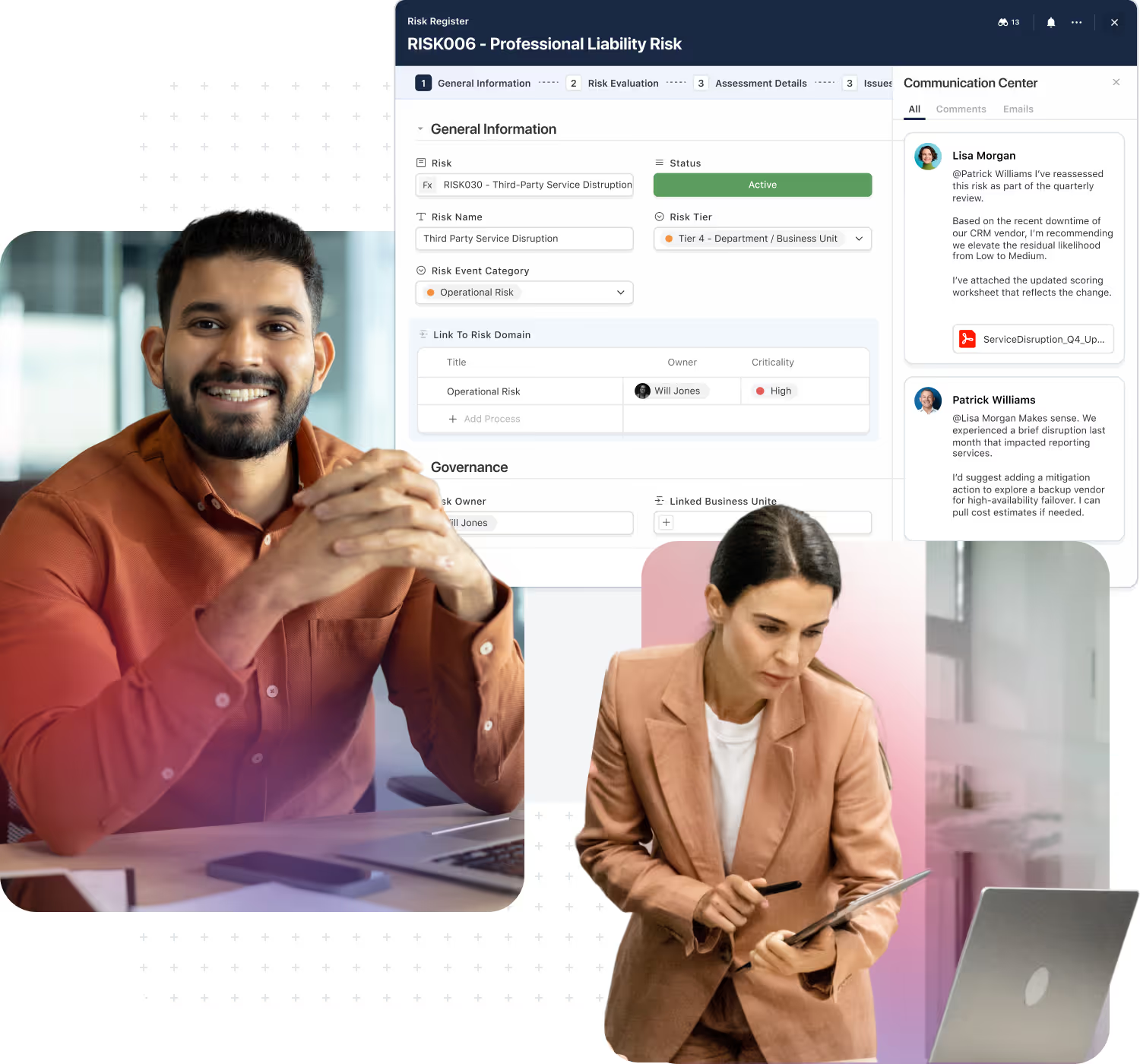
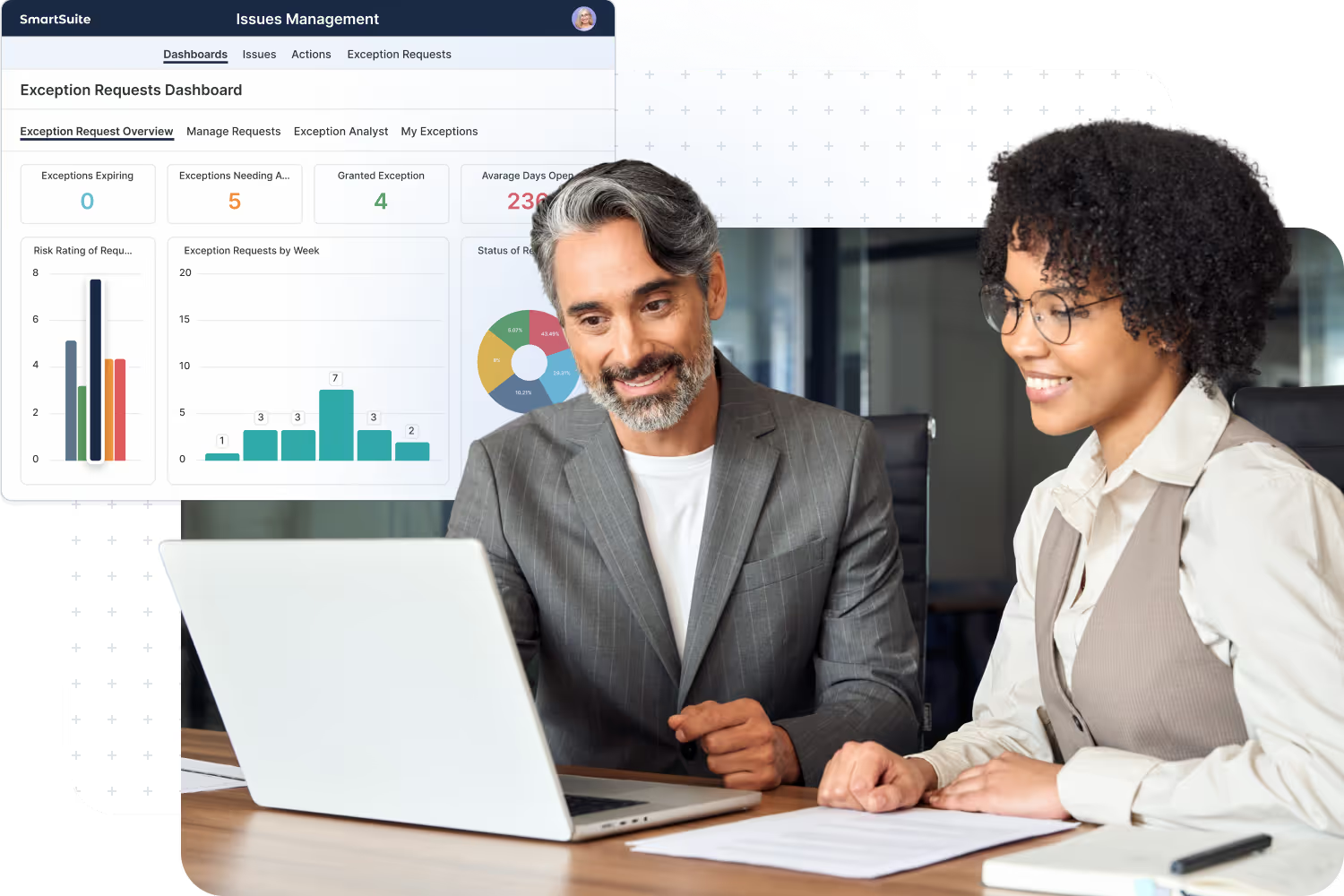
GRC & Operational Resilience
Manage GRC and Resilience programs on one unified platform.
Organizations manage risk, compliance, audit, cybersecurity, and resilience across dozens of disconnected tools—creating blind spots, duplicated effort, and slow response when it matters most. SmartSuite replaces this fragmented approach with one connected platform that unifies governance, risk, and resilience workflows across the enterprise.
SmartSuite connects risks, controls, policies, audits, incidents, third parties, and continuity plans into a single system of record. Teams gain real-time visibility into exposure, control effectiveness, and readiness—while maintaining full traceability for regulators, auditors, and executives.
SmartSuite helps organizations:
- Integrate risk, compliance, audit, cyber, and resilience workflows
- Eliminate silos created by point GRC and legacy systems
- Standardize assessments, testing, evidence, and remediation
- Improve cross-team coordination during incidents and audits
- Maintain continuous oversight of risk, controls, and obligations
IT Service Delivery
Deliver IT services on one connected platform.
IT and internal service teams are under constant pressure to deliver reliable services while managing growing demand, complexity, and risk. SmartSuite provides a modern foundation for IT and service operations—bringing structure, automation, and visibility to the workflows that keep the business running.
From IT service management and asset tracking to internal service delivery across HR, Facilities, Finance, and Legal, SmartSuite centralizes requests, incidents, changes, and operational data into one connected platform. Teams gain consistent processes, SLA visibility, and real-time reporting—without sacrificing flexibility.
SmartSuite helps IT & service teams:
- Centralize service requests, incidents, assets, and operations
- Automate routing, approvals, SLAs, and escalations
- Improve visibility into service performance and operational health
- Coordinate work across IT, shared services, and business teams
- Scale service delivery without adding complexity or tools

Projects & Portfolios
Connect project execution to portfolio strategy.
Projects, programs, and strategic initiatives are how organizations execute change—but too often they’re managed across disconnected tools that obscure priorities, dependencies, and outcomes. SmartSuite connects project delivery to portfolio governance and strategy execution in one unified system.
Teams plan and execute work with shared workspaces, real-time dashboards, and automated workflows, while leaders gain portfolio-level insight into progress, risk, capacity, and value. From project intake through delivery and benefits realization, SmartSuite ensures work stays aligned to what matters most.
SmartSuite helps organizations:
- Plan and execute projects with consistent governance
- Prioritize demand and manage portfolios with confidence
- Track risks, dependencies, and financial performance
- Align projects and programs to strategy and OKRs
- Provide executives with real-time delivery and outcome visibility
Business Operations
Manage business workflows on a unified platform.
Every organization runs on hundreds of core business processes that cut across teams—customer operations, finance, HR, legal, procurement, marketing, and industry-specific workflows. SmartSuite provides a single platform to design, run, and scale these operational processes with clarity and control.
Instead of relying on spreadsheets, email, and disconnected point tools, teams use SmartSuite to standardize intake, approvals, execution, and reporting. Work moves faster, coordination improves, and leaders gain visibility into how the business actually operates day to day.
SmartSuite helps operations teams:
- Standardize and automate cross-functional workflows
- Replace manual coordination with structured execution
- Improve transparency across departments and stakeholders
- Track work, approvals, and outcomes in real time
- Adapt processes as the business evolves—without code
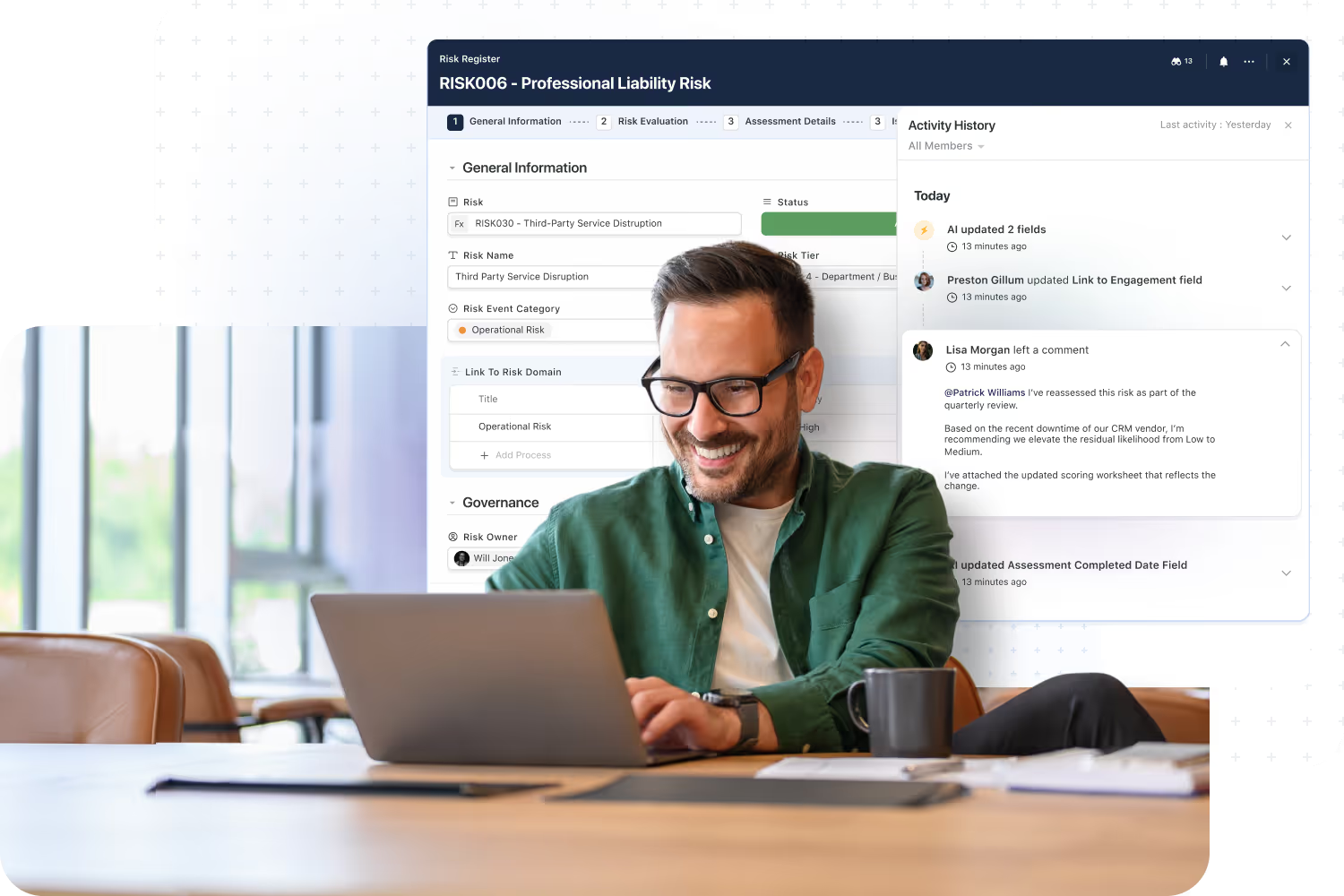
A single foundation powers every solution suite—shared data model, permissions, automation, and reporting.
Work doesn’t break at team boundaries—handoffs, dependencies, and outcomes stay linked across functions.
Enterprise-grade permissions and auditability are built in, so you can scale workflows with confidence.
Teams can configure and evolve workflows quickly—without custom code or long implementation cycles.
AI accelerates building, documentation, analysis, and decision support inside your workflows—not in a separate silo.
Standardize processes, reduce tool sprawl, and gain real visibility because everything runs on one system.
Why SmartSuite?
SmartSuite is built for organizations that want work to stay connected across teams—not fragmented across disconnected processes.
Our AI-native platform is designed with security and governance at the core, supports reliable performance at scale, and integrates with the systems teams already depend on—so workflows stay connected across the business.
SmartSuite includes purpose-built solution suites for GRC, IT Service Delivery, Project Management, and Business Operations, plus a no-code foundation to build and manage any type of workflow.
Leaders choose SmartSuite because it improves execution with clearer ownership and real-time visibility—while delivering a defensible ROI through standardization, efficiency gains, and the ability to consolidate workflows onto one unified platform.
Frequently Asked Questions
Answers to the most common questions about SmartSuite’s pre-built Solutions and how they can be customized for your business.
SmartSuite Solutions are pre-built, customizable workflows designed to help teams manage specific business processes — from GRC and IT Service Delivery to Project Management and CRM. Each Solution includes templates, automations, dashboards, and reports that can be tailored to match your organization’s structure, terminology, and workflows
Yes. Every SmartSuite Solution is fully customizable using our no-code platform.
You can add fields, modify workflows, set permissions, and automate processes without relying on developers — ensuring each Solution fits your business exactly.
SmartSuite’s Integration Framework and open APIs make it easy to connect with your existing tools — including Slack, Microsoft Teams, Jira, Salesforce, ServiceNow, HubSpot, and more.
These integrations ensure your data flows seamlessly across departments and systems, reducing duplication and improving visibility.
Yes. SmartSuite is built for enterprise-grade security with SOC 2 Type II certification, role-based access, encryption at rest and in transit, and full audit logging.
Whether you operate in financial services, healthcare, or the public sector, SmartSuite provides the security, governance, and control your organization requires.
Implementation is fast and flexible. Most teams can deploy a Solution in a matter of days or weeks, depending on complexity.
Pre-built templates, step-by-step setup guides, and onboarding support make it easy to get started and realize value quickly.
Absolutely. In addition to pre-built Solutions, SmartSuite allows you to create your own workflows using drag-and-drop configuration.
Teams can build fully custom Solutions for any business process, then scale or replicate them across departments — all within the same platform.
Let’s Talk About Transforming Your Workflows
Discover how SmartSuite’s productized Solution Suites, AI automation, and no-code tools can streamline your most critical processes—tailored to your organization.



