In this guide, I'll walk through what compliance risk actually means in practice, the categories worth tracking, how to respond when you find one, and how to run a proper assessment without bending your team around a framework that doesn't fit.
TL;DR
- Compliance risk lives in the gap between what regulators, contracts, customer attestations, and internal policies require, and what your business is actually doing day to day.
- The categories worth tracking include regulatory, statutory, contractual, ethical, data privacy, financial, operational resilience, and AI compliance risk.
- Your response options come down to four moves: avoid the activity, mitigate through controls, transfer with insurance or contracts, or accept the residual exposure on the record.
- A compliance risk assessment is a recurring cycle, not a one-time project, with phases that overlap rather than march in a straight line.
- Tooling matters more in 2026 than 3 years ago, and connected GRC platforms like SmartSuite are filling the gap between Excel registers and six-figure enterprise GRC suites.
What is compliance risk?
Compliance risk lives in the space between the policy and the practice.
It's what shows up when a contract you signed three years ago has a data residency clause your engineering team forgot about, when a regulator updates a rule.
Nobody notices for six months when your privacy notice says one thing and your CRM does another, or when a vendor's SOC 2 report quietly lapsed three months ago.
The textbook version is more compact.
It's the legal, financial, operational, and reputational exposure your organization carries when it fails to meet a regulator's requirement, a contract clause, an internal policy, or an industry standard.
But the textbook version makes it sound like a binary state. Compliant or not.
In real programs, you're never fully compliant and never fully exposed. You're somewhere on a spectrum, and your job will be to know exactly where.
The "compliance" half is the ongoing work of keeping pace with rules from regulators, industry bodies, customer contracts, and your own policies.
The "risk" half is the recognition that no compliance program is ever fully closed.
- There's always a control that hasn't been tested in a while.
- A vendor whose certifications quietly expired.
- A clause buried in a customer contract that nobody reread.
- Or a regulation that just changed underneath you.
Most teams treat compliance like a checklist for too long, then learn the hard way that being "compliant" on paper and being "low-risk" in practice aren't the same thing.
What are the different types of compliance risk?
Here are the main compliance risk categories worth knowing:
- Regulatory compliance risk is the one most people think of first.
It's the exposure when you fall behind on rules from the SEC, OCC, FINRA, FDA, FTC, or whatever regulator owns your space. GDPR, HIPAA, SOX, PCI DSS, the EU AI Act, and DORA all sit here.
- Statutory compliance risk is closely related but covers laws specifically, not regulator interpretations.
Wage-and-hour rules, anti-discrimination statutes, environmental laws like CERCLA, and OSHA workplace safety obligations all fall in this group.
- Contractual compliance risk covers the obligations you signed up for in agreements with customers, partners, lenders, or vendors. SLAs, data processing addendums, indemnity clauses, and exclusivity terms.
Miss one and you may not get fined by a regulator, but you'll be sued or lose the contract.
- Internal policy and ethical compliance risk covers the commitments your own organization has made: a code of conduct, an anti-bribery program, AI use policies, and supplier conduct expectations.
These don't always come with a fine attached, but they come with culture and hiring consequences, plus reputational damage when they break.
- Data privacy and security compliance risk has gone from "a category" to "the dominant category" in the last few years.
GDPR, CCPA, the Colorado Privacy Act, India's DPDP Act, and a long list of state laws all fall here.
- Financial compliance risk covers SOX 404 controls, anti-money-laundering (AML), Bank Secrecy Act, OFAC sanctions screening, and tax reporting. Banks live in this category.
So do public companies. Anyone running cross-border payments deals with it constantly.
- Operational resilience compliance risk has emerged as its own category in the last few years.
Regulators in financial services, energy, and healthcare now expect documented evidence that the business can absorb disruption (third-party outages, cyber incidents, service failures) and recover within tested tolerances.
The Bank of England's operational resilience rules, the FCA's PS21/3 (whose transition period ended March 2025), and DORA in the EU all sit here.
- AI compliance risk is the newest entry on the list. Model documentation, training data lineage, bias testing, transparency obligations under the EU AI Act, and a patchwork of US state laws on automated decision-making.
Why is compliance risk important?
There are 2 reasons why compliance risk is important:
- First, when compliance risk lands, it lands hard.
The SEC obtained $8.2 billion in financial remedies in fiscal year 2024, the highest figure in the agency's history.
Cumulative GDPR fines since 2018 now exceed €7.1 billion, with around €1.2 billion levied in 2025 alone.
A single misstep on data privacy can wipe out years of growth.
- Second, regulators are getting more demanding about how compliance is managed, not just whether it's met.
Auditors don't want to see your policies anymore.
They want to see how you map obligations to controls, who owns what, when controls were last tested, and how leadership is informed when something fails.
Industry guidance from groups like OCEG, ISACA, and the IIA has shifted in the same direction. Less paper, more evidence.
➡️ For a regulated business in 2026, compliance risk isn't a back-office function. It's a board-level metric that can affect valuation, insurance pricing, customer trust, and acquisition readiness.
What are the benefits of compliance risk management?
A working program pays off in ways that are hard to measure individually but obvious in aggregate.
A few payoffs worth calling out:
- Fewer surprises when regulators show up. When you've already mapped obligations to controls, you can pull a defensible answer in hours instead of weeks.
- Cleaner deals with enterprise customers. Most enterprise procurement now asks for SOC 2, ISO 27001, or HIPAA attestations before a contract starts. A working program turns those questionnaires from fire drills into routine.
- Better insurance economics. Cyber and D&O insurers reward documented programs with lower premiums, and some won't underwrite at all without proof of basic controls.
- Faster product launches in regulated markets. Banks entering new jurisdictions, healthcare companies launching new device categories, AI vendors selling into the EU, and SaaS startups expanding into Asia-Pacific all move more quickly when compliance is built into the development process instead of bolted on at the end.
- Lower internal friction. When everyone knows who owns which control and which obligation, audits stop becoming a quarterly crisis.
How can you respond to compliance risk?
Once you've identified a compliance risk, four responses show up across every framework: avoid, mitigate, transfer, or accept.
The right one depends on two variables: how much control you have over the obligation, and how much exposure you can absorb if something goes wrong.
- Avoid is the right move when the activity creating the compliance risk isn't core to the business and the exposure is high.
A US bank that decides not to onboard customers in a sanctioned country is avoiding.
A SaaS company that pulls out of California rather than meet CCPA obligations is avoiding (rare, but it happens).
- Mitigate absorbs the bulk of the day-to-day compliance workload.
You keep the activity, but you build controls to reduce the probability of a breach.
MFA on access controls, encryption for data at rest, mandatory training for employees, vendor due diligence reviews. The job here is making the residual risk small enough to live with.
- Transfer moves part of the risk onto someone else.
Cyber insurance, contractual indemnities, captive arrangements, or outsourcing the regulated activity to a specialist provider that carries its own attestations.
Transfer is rarely a complete answer because regulators usually still hold the original entity accountable, but it does change the financial picture.
- Accept is the response that mature programs use far more than people expect.
When the cost of mitigating outweighs the potential exposure, you document the decision, get sign-off, and move on.
Acceptance is only legitimate when it's deliberate, recorded, and periodically reviewed at the right level of the organization.
The trap most teams fall into is defaulting to "mitigate everything" because it feels responsible.
It's not. Mitigating a low-impact compliance risk you have no real control over is wasted effort.
Accepting a high-impact compliance risk you have lots of control over is negligence.
The job is to get every risk into the right quadrant first, then pick the right response.
How to conduct a compliance risk assessment
A compliance risk assessment is the structured process of figuring out where your obligations sit, what controls cover them, and where you're actually exposed.
Most playbooks describe this as a five-step linear march: scope, identify, score, treat, monitor.
That framing is fine for a textbook.
In real programs, the work doesn't move in a straight line because regulations don't wait for you to finish "step 3" before something changes.
It works better as three overlapping phases that cycle continuously.
Phase 1: Scope and discover
This phase defines the boundary of the assessment and surfaces what could go wrong inside that boundary.
Scope matters more than most teams give it credit for.
An assessment of "the whole company" turns into a shallow survey of nothing. An assessment of "our SOC 2 controls in North America for the data platform" gets you somewhere useful.
Discovery happens through interviews with department heads, obligation registers pulled from regulators and contracts, reviews of recent incident reports, and external signals like enforcement bulletins and analyst commentary.
Everything lands in a compliance obligation register, which becomes your single source of truth for the next two phases.
The mid-market reality check: most companies discover their obligation count runs well into the hundreds once they actually count, not the twenty or thirty their team initially estimated.
Phase 2: Assess, map, and respond
Phase 2 is where the real analytical work happens, and it has two halves.
The first half is scoring and prioritizing.
For every obligation you surface, you're answering two questions. What's the worst that happens if we breach it? And how likely is the breach, given how the business actually runs today?
A risk matrix puts those two variables into conversation. Plot likelihood against impact on a 5 by 5 grid and obligations cluster into a priority order.
- Quantitative methods work for obligations you can put a dollar figure on, like AML penalties or contractual SLA breaches.
- Qualitative methods (high, medium, low with narrative context) work better for ethical and reputational obligations where numbers would be guesswork.
The second half is mapping, testing, and deciding the response.
Once an obligation is prioritized, you map controls to it.
Mature programs build a control library once and reuse it across every framework they care about, instead of duplicating work for each new audit.
Then test the controls. Don't take "we have a policy" as evidence of anything. Pull samples, walk through procedures, look at logs, and talk to the person who actually runs the control.
Whatever the test reveals, score the residual risk (inherent risk minus the effect of working controls) and pick the response: accept, mitigate further, transfer, or avoid.
Each obligation gets an owner, a plan, a due date, and one or more controls tied to it.
Phase 3: Operate and monitor
This is the phase that separates a real compliance program from an annual binder exercise.
Regulations change. Contracts renew. New products launch. Vendors come and go. Controls decay.
💡 Mature programs run continuous compliance monitoring on top of the annual assessment, with KRIs that flag when a control is drifting, scheduled control re-tests, automated evidence requests on a cadence, and live dashboards that show readiness across every framework in scope.
Annual assessments are the floor, not the ceiling. The phases overlap.
New obligations identified in Phase 3 feed back into Phase 1, and controls scored as ineffective in Phase 2 get redesigned and re-tested when monitoring in Phase 3 surfaces problems.
The register is a living document, not a snapshot.
What are the different compliance risk frameworks?
Here's something the vendor pitches that don't tell you: almost no mature program runs on a single framework.
The teams doing this well blend two or three.
ISO 31000 covers enterprise-level risk principles. NIST CSF or ISO 27001 anchors the cyber and information security side. COSO ERM ties risk to strategy, especially in public companies. The OCEG GRC Capability Model integrates all three functions into one operating model.
With that framing in place, here's what each framework gives you:
- ISO 31000 is the international standard for risk management from the International Organization for Standardization. It's principles-based, lightweight, deliberately abstract, and widely used as the umbrella across enterprise programs.
- ISO 27001 and ISO 27002 are the dominant standards for information security management systems. 27001 is the certifiable version and 27002 covers the actual control set. Useful for any business that handles customer data and wants third-party validation.
- COSO ERM comes from the Committee of Sponsoring Organizations of the Treadway Commission. It's the framework most public-company audit committees and SOX programs are aligned with, especially in the US.
- NIST Cybersecurity Framework (CSF) 2.0 added the "Govern" function in 2024 and now covers governance, identify, protect, detect, respond, and recover. It's used well beyond US federal contractors at this point, especially in critical infrastructure and financial services.
- OCEG GRC Capability Model (Red Book) is more of an integration blueprint than a standalone methodology. It's designed for organizations that want governance, risk, and compliance working as one connected operating model instead of three separate functions.
- COBIT 2019 from ISACA is the framework for IT governance and management. Useful for companies that need to align IT controls with business objectives and regulatory expectations.
- FAIR (Factor Analysis of Information Risk) is the one to know when you need to put dollar figures on compliance and cyber exposure. Boards increasingly want risk reported in financial terms, and FAIR gives you the methodology to do it.
The point isn't framework purity.
It's a compliance program that fits your business, picks the right framework for each layer, and doesn't force the team to relearn methodology every time a new regulation lands.
What kind of tools can you use for compliance risk?
The tools available for compliance risk management fall into a few clear buckets.
- Spreadsheets: Most programs start here.
A compliance register in Excel or Google Sheets works fine when the program is small, and one person can keep it current.
It breaks the moment you need cross-team visibility, audit trails, version control, change history, or evidence that an external auditor can independently verify.
- Compliance automation platforms: Tools like Drata, Vanta, Sprinto, Secureframe, and Scytale focus on automating evidence collection for certifications like SOC 2, ISO 27001, HIPAA, and PCI DSS.
They're good at the certification job, especially for fast-growing tech companies that need their first SOC 2 in 90 days.
The trade-off is that they weren't built to manage the broader compliance risk picture: third-party risk, regulatory change management, AI governance, ethics and conduct.
- Enterprise GRC suites: Platforms like ServiceNow GRC, IBM OpenPages, MetricStream, Archer, and SAP GRC.
Built for organizations with hundreds of obligations, complex regulatory environments, and the budget for a six-month implementation.
They go deep on risk modeling, control testing, board reporting, and regulatory change tracking, but six- and seven-figure deals are common, and time-to-value is measured in quarters, not weeks.
- Mid-market GRC platforms: Tools like AuditBoard, Hyperproof, LogicGate, and StandardFusion sit between automation platforms and full enterprise GRC.
They cover risk, controls, audits, and policies in more depth than the certification platforms, with shorter onboarding than the IBM and SAP suites.
- Connected Work OS platforms: A newer category where compliance, risk, audit, and operational workflows live in one no-code system instead of being walled off in a specialty tool.
SmartSuite is the example most directly shaped by this approach. The angle is that compliance work is connected to everyday operations, not separated from them.
➡️ If your compliance program has outgrown spreadsheets but you're not ready to commit to an enterprise GRC build, SmartSuite is worth a serious look.
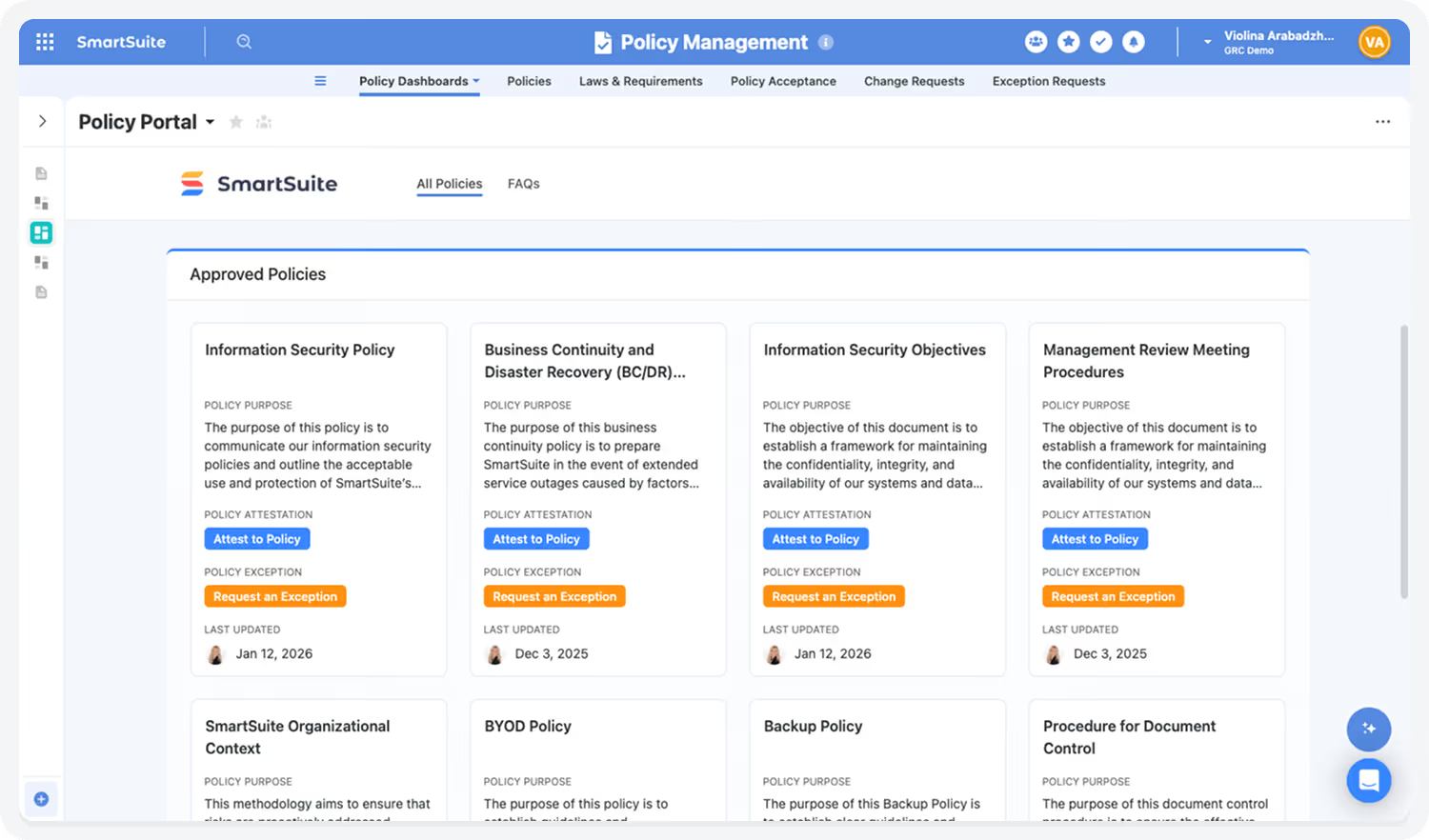
It's an AI-native work platform where compliance teams can run risk registers, control libraries, audit programs, third-party reviews, AI governance, and policy lifecycle management in one connected workspace.
Because the platform is no-code by design, you can model your compliance program around how the business actually runs, instead of bending the business to fit someone else's template.
Built-in automation handles the tedious work: evidence requests on a schedule, escalation when a control test fails, vendor reassessment cycles, attestation reminders, and review-cycle prompts.
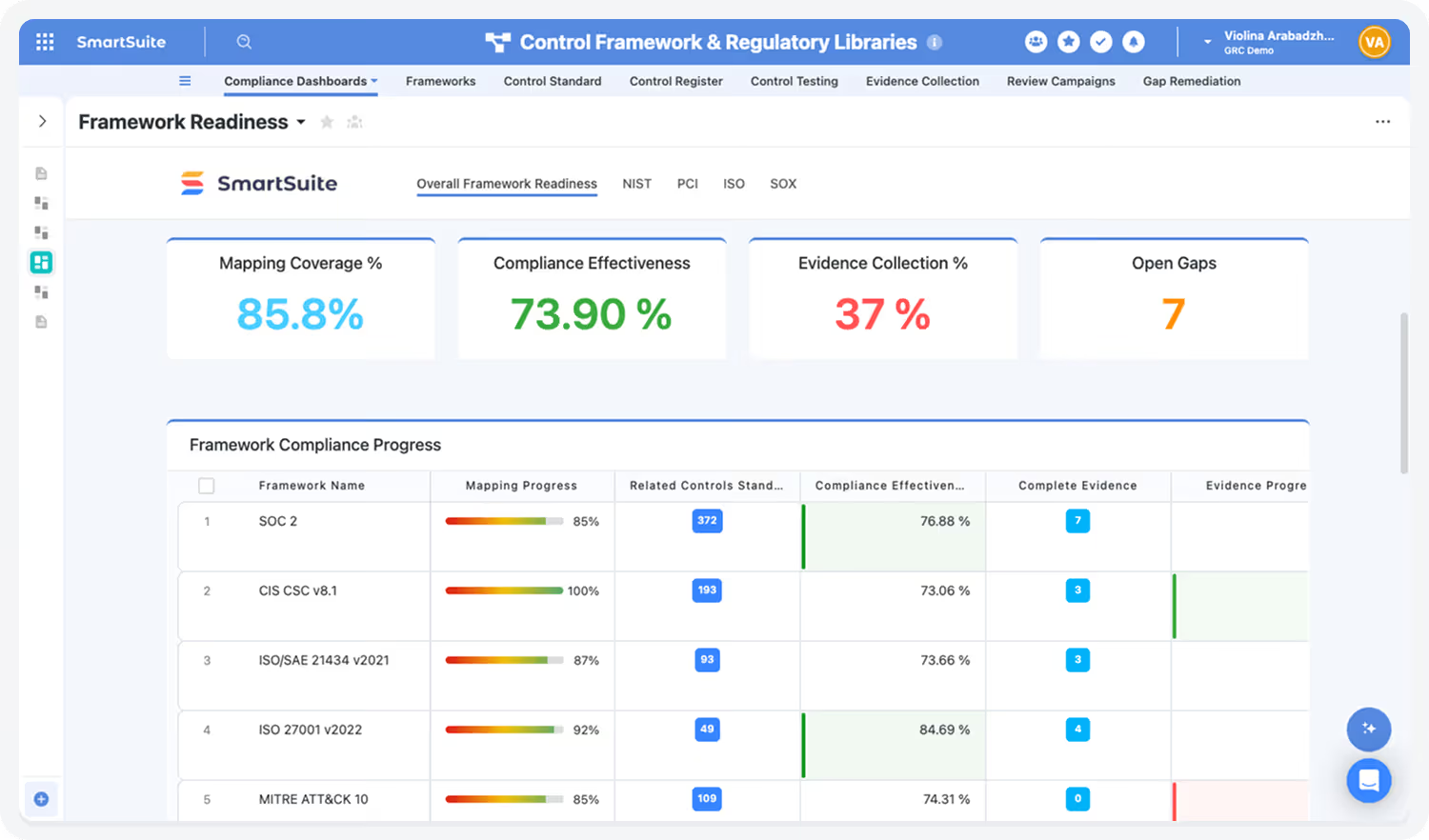
Live dashboards give leadership a real-time picture of compliance health across SOC 2, ISO 27001, GDPR, HIPAA, SOX, and any custom framework you map.
SmartSuite AI helps with summarizing vendor questionnaires, drafting policy updates, surfacing gaps in evidence, and flagging anomalies in incident reports, while keeping a human-in-the-loop check on every governance decision.
It fits well for mid-market companies and regulated industries like banking and healthcare, where compliance teams want their program connected to operations rather than isolated in a certification-only tool.
Pricing starts at $15/user/month for the Team plan.
Run your compliance program on a platform built for it
The tools above each solve a slice of the compliance risk problem.
- Spreadsheets are fine until the program scales past one person.
- Compliance automation platforms like Drata and Vanta handle certification work cleanly but were never designed to manage the full picture (third-party, regulatory change, AI, ethics).
- Enterprise GRC suites like IBM OpenPages and ServiceNow are built for the largest, most regulated organizations, and the budget profile reflects that.
For mid-market companies and growing teams, the sweet spot is a platform like SmartSuite that handles compliance risk, controls, audits, third-party reviews, and policy work in one place, connects to the rest of the business, and doesn't take six months to turn on.
You wouldn’t have to choose between flexibility and governance, as our platform gives you both:
- A no-code environment where your compliance team can shape the program however it needs.
- With enterprise-grade permissions, audit logs, AI governance, and full traceability built in.
Risks, controls, audits, vendors, incidents, policies, and remediation work all sit in one governed workspace, with dashboards that update as the work changes.
➡️ Start a free SmartSuite trial or book a demo to see how your team can run compliance risk, governance, and audit work in one place.
SmartSuite provides work platform for standardizing workflows in the following areas:
- Governance, Risk & Compliance
- IT & Service Ops
- Project / Portfolio Management
- Business Operations















